In 2023, I was part of a project to help a European insurance company expand their cloud infrastructure to serve customers in India. The architecture we’d been using for their European platform was modern and clean: multi-region AWS, centralized identity and access management, a single data platform that aggregated customer data for analytics and risk modeling.
We spent three months designing the India expansion before our legal team flagged something that rearranged the entire project plan: India’s Digital Personal Data Protection Act (DPDP Act), which required certain categories of personal data for Indian citizens to be processed and stored within India’s borders. The personal data we’d planned to flow into our European analytics platform couldn’t legally go there.
We weren’t just adding a region. We were building a parallel data architecture, a parallel identity layer, and rethinking every system that touched personal data. The cloud architecture was the easy part. The compliance architecture was where the real work was.
That experience is increasingly common. Data sovereignty has gone from a compliance footnote to a first-class architectural constraint, and most engineering teams encounter it after they’ve already made commitments that are painful to reverse.
Defining the Terms (They’re Not the Same Thing)
I use these terms precisely because conflating them leads to bad architecture decisions:
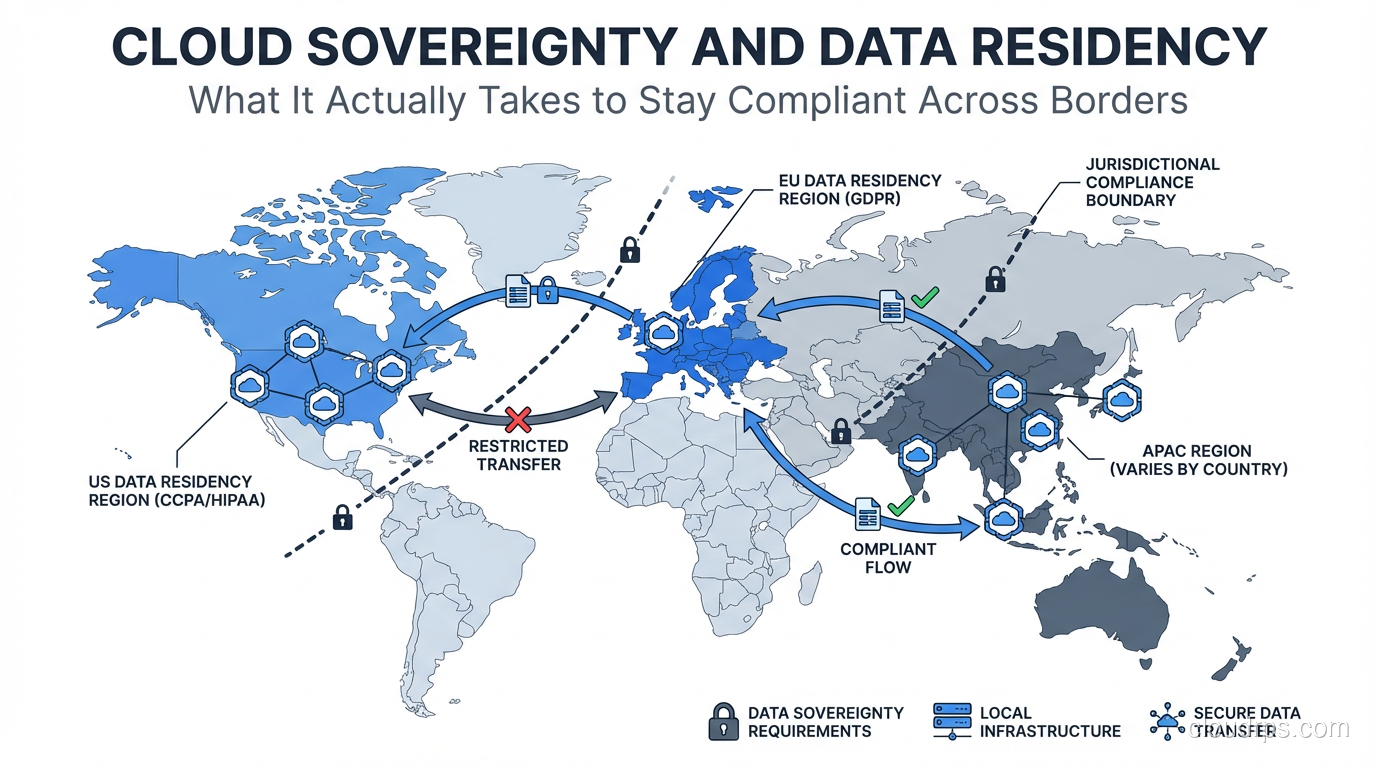
Data residency: A specific requirement that data must be stored within a defined geographic boundary (a country, a region, or a specific data center). This is the most common requirement. “EU customer data must be stored in the EU” is a data residency requirement.
Data sovereignty: A broader concept that the data is subject to the laws and regulations of the country where it is stored or processed. Data residency is often imposed to achieve data sovereignty, but they’re not equivalent. Your data can be stored in a compliant region while still being legally accessible to another government through contracts or corporate structure.
Data localization: The strictest form, where data must not only be stored locally but often processed locally, and may not be transferred out even with encryption or anonymization. Russia, China, and increasingly India have localization requirements for specific data categories that are functionally stricter than GDPR.
Data portability: The opposite requirement, from GDPR: data subjects have the right to receive their data in a portable format. This creates an interesting tension with localization requirements in some jurisdictions.
Understanding which requirement you’re actually subject to changes the architecture completely. Residency requirements are usually solvable with region selection and proper data routing. Sovereignty requirements sometimes require avoiding US-based cloud providers entirely (because of CLOUD Act considerations). Localization requirements may require truly isolated infrastructure.
The Regulatory Landscape in 2026
The compliance environment has become significantly more complex in the past few years. What’s in play:
GDPR (EU): The baseline everyone knows. Data transfers outside the EU require adequate protections: adequacy decisions, Standard Contractual Clauses (SCCs), or Binding Corporate Rules. The Schrems II ruling invalidated Privacy Shield, and the EU-US Data Privacy Framework that replaced it is under ongoing legal challenge. Treat US transfers as having compliance risk that requires legal review.
DPDP Act (India): India’s data protection law has teeth. Personal data of Indian citizens must be processed in India, with some categories (“sensitive” personal data) subject to stricter localization. The list of countries approved for cross-border transfer is still evolving. For any India market expansion, assume you need India-region infrastructure.
PIPL (China): China’s Personal Information Protection Law is comprehensive and extraterritorial. Processing Chinese citizens’ personal data outside China requires a security assessment, standard contract, or certification. In practice, most enterprises serving Chinese users run completely separate infrastructure inside China, often with a local partner.
State laws (US): CCPA, CPRA, and similar state laws are primarily data use and disclosure laws rather than residency laws, but the compliance obligations create complexity in your data architecture. The patchwork of state laws is one of the arguments for architecting for data minimization: only collect what you need, store it where you must.
Sector-specific requirements: Healthcare (HIPAA in the US, similar frameworks elsewhere), financial services (various national banking regulations), and government contractors (FedRAMP, IL4/IL5 in the US; equivalents elsewhere) have residency or cloud security requirements layered on top of general privacy law.
The key insight: this isn’t going to simplify. The trend is more localization requirements, stricter enforcement, and increasing incompatibility between jurisdictions. Architecting for sovereignty flexibility is not a one-time compliance exercise; it’s ongoing infrastructure design.
The Sovereign Cloud Options
The major cloud providers have recognized this as a market opportunity and built sovereign cloud products:
AWS GovCloud: US-only, designed for US government and federal contractors. Physically separate region, operated by US citizens, isolated from standard AWS regions. Meets FedRAMP High, ITAR, and similar requirements. Not the right answer for EU or APAC sovereignty requirements.
AWS European Sovereign Cloud: Announced in 2023, operational and expanding by 2026. Designed specifically for EU data sovereignty: EU-resident operators, EU-based infrastructure, operational separation from standard AWS regions. Relevant for organizations where GDPR compliance requires operational sovereignty (not just data residency).
Azure Sovereign Cloud: Azure Government (US), Azure Germany (operated by Deutsche Telekom’s T-Systems as a data trustee, though this model has evolved), Azure operated by 21Vianet (China). Microsoft has the most mature sovereign cloud portfolio by country.
Google Cloud Sovereign: Google’s sovereign cloud offerings are building out, with partnerships with local providers in key markets. Less mature than AWS and Azure sovereign options.
Local cloud providers: For some jurisdictions, the right answer isn’t a global cloud provider’s sovereign offering but a genuinely local provider. OVHcloud in France, Deutsche Telekom in Germany, NTT or KDDI in Japan. These are more operationally complex to use (smaller service catalog, less tooling maturity) but provide genuine data trustee arrangements that satisfy requirements global providers can’t.
The sovereign cloud options typically cost 20-40% more than equivalent standard cloud capacity and have smaller service catalogs. Not every AWS service is available in GovCloud or the EU Sovereign Cloud. Budget for this and plan your architecture around what’s available.
Architecting for Multi-Jurisdiction Compliance
The hard part isn’t understanding the regulations. It’s building an architecture that satisfies multiple, sometimes conflicting, requirements simultaneously.
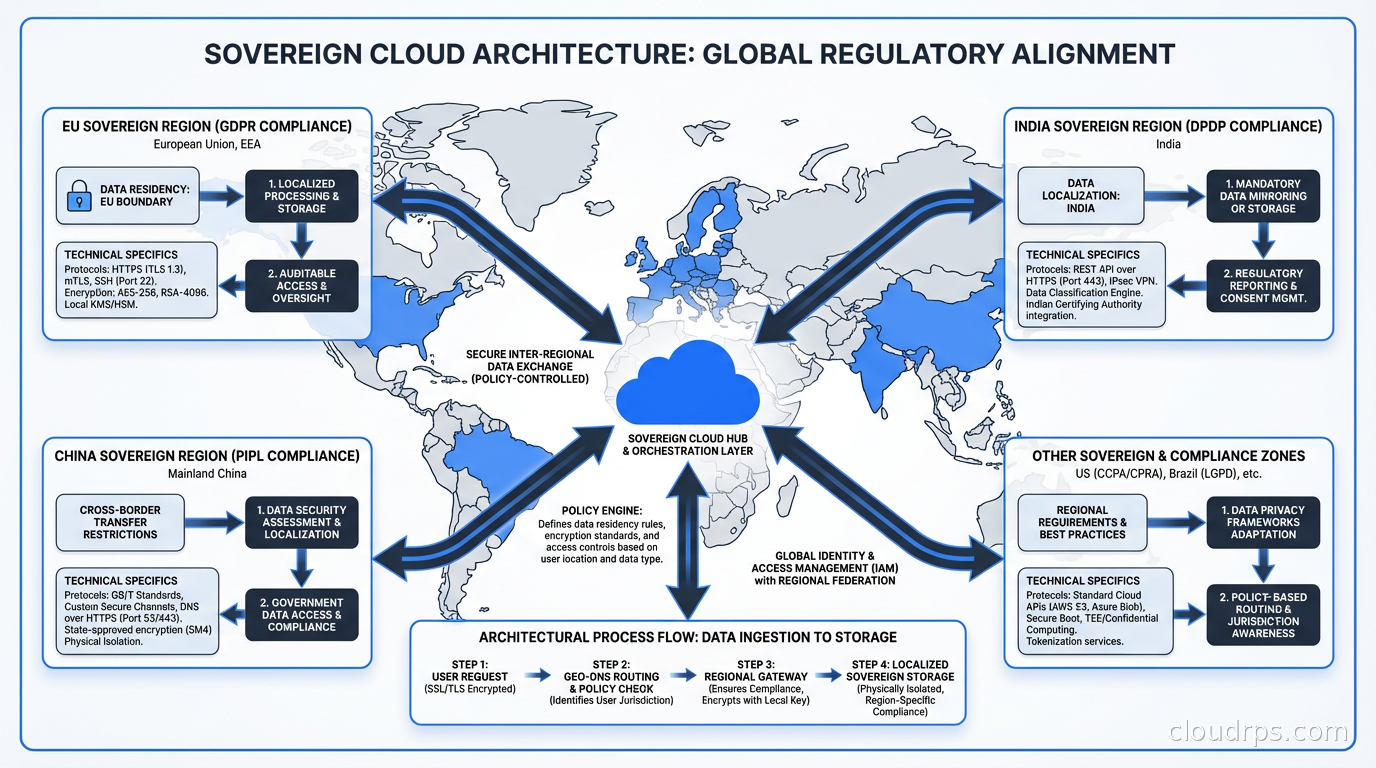
The approach I’ve found most durable: design around data classification, not data location.
Step 1: Classify your data by sensitivity and regulatory scope. Not all data needs the same treatment. Most enterprises have at least three tiers:
- Non-personal, non-regulated data: internal operational metrics, aggregated analytics, public content. Can go anywhere.
- Personal data with residency requirements: customer PII, behavioral data. Must stay in appropriate regions.
- Sensitive personal data with localization requirements: financial data, health data, biometric data in certain jurisdictions. Strict location constraints, possibly no-cross-border.
Step 2: Tag data at ingestion. Every piece of data that enters your platform should be tagged with its classification and the jurisdiction(s) it’s subject to. This sounds simple; doing it consistently at scale is genuinely hard. You need a data catalog, a classification taxonomy, and a process for keeping it current as your data model evolves. The data mesh architecture approach of domain ownership can help here: each domain team owns the classification of their data products.
Step 3: Build jurisdiction-aware routing. Data flows should respect classification tags. EU personal data doesn’t leave EU regions. India personal data stays in the India region. Data that’s classified as non-personal can flow globally. This requires your pipeline infrastructure to be sovereignty-aware: you can’t just run a global Kafka cluster that ingests everything and decides where to route later.
Step 4: Separate control plane from data plane where necessary. One of the more nuanced requirements in some jurisdictions is the distinction between data operations (access by operators to the customer’s data) and data storage. You might be able to centralize your control plane (orchestration, monitoring, identity) while keeping the data plane regional. But some sovereign cloud requirements go further and require that operational access to customer data be restricted to personnel in the same jurisdiction. This affects your on-call rotation, your security team’s access, and your data engineering team’s tooling.
Encryption Isn’t a Silver Bullet
I’ve seen a lot of architectural designs where the answer to data sovereignty is “we encrypt everything with customer-managed keys, so it doesn’t matter where it’s stored.” This is sometimes true and sometimes dangerously wrong.
For basic GDPR data residency, storing encrypted data outside the EU can be acceptable if the encryption is strong, the keys are managed by an EU-based entity, and the data can’t be meaningfully accessed by the storage provider. But this is a legal question, not just a technical one, and it has been tested and found insufficient in some interpretations.
For data localization requirements (China, Russia, certain Indian data categories), encryption doesn’t help. The requirement is that the data physically be within the jurisdiction, regardless of encryption state.
For zero trust security models, encryption at the data layer is essential but doesn’t substitute for jurisdiction controls. You need both: data encrypted with appropriate key management AND stored in the right location.
The right approach to encryption in sovereign architectures: use encryption everywhere as a defense-in-depth measure, use customer-managed keys (BYOK) where regulations require you to maintain control, but don’t use encryption as a substitute for proper data residency. They serve different purposes.
Key Management Across Jurisdictions
Key management becomes a sovereignty question in its own right. If your data is stored in the EU but your encryption keys are managed by a US-based key management service, a US legal order compelling the key management service to disclose keys effectively gives the US government access to your EU data. This is the core concern behind CLOUD Act considerations in EU sovereign cloud requirements.
The architecture for genuine sovereignty:
Use region-locked KMS instances. AWS KMS, Azure Key Vault, and GCP Cloud KMS all support region-pinned key stores. Keys created in eu-west-1 don’t replicate to us-east-1. Make this explicit in your key policies.
Consider HYOK (Hold Your Own Key) for the most sensitive data. Some scenarios require that the cloud provider never has access to the decryption keys. This is operationally complex and creates availability risks (lose the key, lose the data), but it’s the right answer for certain compliance profiles.
Audit key access thoroughly. Who can access the keys that decrypt sensitive data? In a sovereignty context, this isn’t just a security question, it’s a compliance question. Key access logs are evidence of whether you’re living up to your sovereignty commitments.
For teams managing secrets across jurisdictions, the secret management infrastructure you build needs to be jurisdiction-aware: secrets for EU deployments live in EU vaults, accessed by EU-based automation, audited separately from your global secrets store.
The Federated Identity Problem
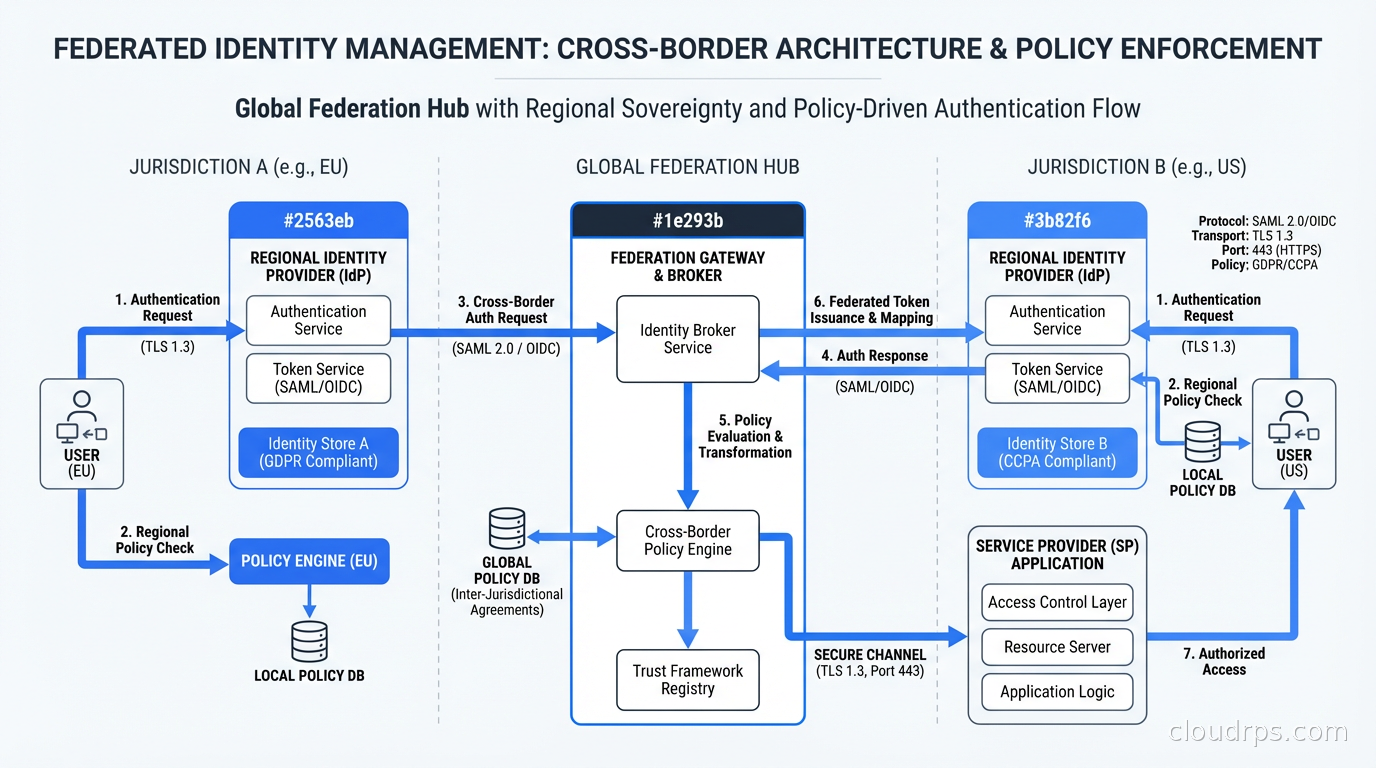
Cross-border identity management is where sovereignty requirements create the most architectural pain. Most enterprise identity platforms are global by design: a single Azure AD or Okta tenant, a central user directory, authentication policies that apply globally.
Sovereignty requirements can conflict with this in two ways:
Data residency of identity data: The user’s profile, authentication history, and authorization data may itself be personal data subject to residency requirements. An EU user’s authentication logs might need to stay in the EU.
Operational access controls: If your identity platform is operated globally, you may have US-based administrators who can access EU users’ identity data. Some sovereignty requirements prohibit this even if the data is stored in the EU.
The solutions range in complexity. Simple data residency: replicate your global identity platform to regional instances, keep identity data in-region. Stricter operational sovereignty: run genuinely separate identity tenants per jurisdiction, with separate administrative staff. The strictest: completely isolated identity stacks per jurisdiction, accepting that a user is separate personas in each region.
I’ve implemented each of these. The strictest approach means your users don’t have a single account that works everywhere, which creates product UX complexity your business teams will push back on. These are conversations worth having before you commit to an architecture, not after.
Cost and Complexity Tradeoffs
Sovereignty-compliant architectures cost more. This is a fact, not a complaint, and architects who pretend otherwise end up with executives who are surprised by the numbers.
The cost drivers:
Duplicate infrastructure: Running separate stacks per jurisdiction means duplicate compute, duplicate storage, duplicate monitoring. There’s limited opportunity to share infrastructure across compliance boundaries.
Sovereign cloud premiums: As mentioned earlier, sovereign cloud options typically cost 20-40% more than equivalent standard cloud. Budget for this explicitly.
Operational complexity: Running five regional compliance stacks is harder than running one global stack. Your SRE team needs expertise in each region’s quirks. Your incident response processes need to account for jurisdictional differences in who can access what.
Legal and compliance overhead: You need legal review of data transfer mechanisms (SCCs, adequacy decisions), regular audits, and documentation that demonstrates compliance. This is not a one-time cost.
My approach to making the business case: frame the cost of compliance as the cost of market access. If you want to operate in India, the DPDP compliance architecture is the price of entry. If you want to serve EU government customers, data sovereignty compliance opens a market you can’t otherwise access. The comparison isn’t “sovereignty architecture vs no sovereignty architecture”; it’s “what’s the value of the market segment you’re enabling?”
For the multi-cloud strategy conversation, data sovereignty is increasingly one of the legitimate reasons to operate across multiple providers. If your Indian operations need to use a local provider due to data localization requirements, but your EU and US operations use AWS, you’re multi-cloud by regulatory necessity, not by choice.
Practical Starting Points
If you’re starting this journey, the place to start is a data map, not an architecture diagram.
Sit down with your legal team and build a data map: what personal data do you collect, from which jurisdictions, for which purposes, and where does it flow? This map will reveal the compliance requirements that actually apply to your organization. Don’t build architecture for requirements you don’t have.
From the data map, identify the high-risk flows: EU data going to US systems, Indian customer data going through global platforms. Focus your sovereignty architecture on these flows first.
Then engage your cloud provider’s compliance teams. AWS, Azure, and GCP all have compliance and sovereignty specialists who can map your requirements to their product offerings. These conversations are free and often very useful.
Build your compliance architecture incrementally: start with data residency controls (the minimum viable compliance), then layer in operational sovereignty controls (who can access what), then key management isolation, then federated identity separation. Each layer adds cost and complexity; do the cheaper layers first and ensure they’re working before adding the next.
And document everything. Compliance is an audit sport. The difference between a compliant architecture and a certified-compliant architecture is the documentation that proves what you built and why it meets the requirements. Start the documentation before the auditors arrive.
The regulatory environment will keep changing. GDPR enforcement continues to evolve through court decisions. New data protection laws are being passed in more jurisdictions every year. The engineers who build sovereignty-aware architectures now, with the flexibility to adapt to new requirements, are building something that will serve their organizations for the decade ahead. The ones who build global-by-default and add compliance as an afterthought will keep running expensive remediation projects every time a new regulation comes into force.
Get Cloud Architecture Insights
Practical deep dives on infrastructure, security, and scaling. No spam, no fluff.
By subscribing, you agree to receive emails. Unsubscribe anytime.