In 1998, I installed my first intrusion detection system. It was Snort, running on a repurposed Pentium II tower, sitting on a span port off a Catalyst switch. The thing generated so many alerts that we literally couldn’t read them all. After two weeks, the senior network admin unplugged it and said, “This is worse than useless. It’s generating anxiety.”
He wasn’t wrong, at least not about that particular deployment. But he was wrong about the technology. The problem wasn’t that intrusion detection was a bad idea. The problem was that we had no process for the alerts, no tuning discipline, and no understanding of our own baseline traffic. We were drinking from a fire hose and blaming the hose.
I’ve spent the intervening decades learning how to deploy these systems properly. The tools have matured enormously, but the fundamental challenges – signal versus noise, inline versus passive, detection versus prevention – remain. Let me walk you through the real differences between IDS and IPS, when each makes sense, and how to avoid the mistakes I made with that Pentium II.
The Core Distinction
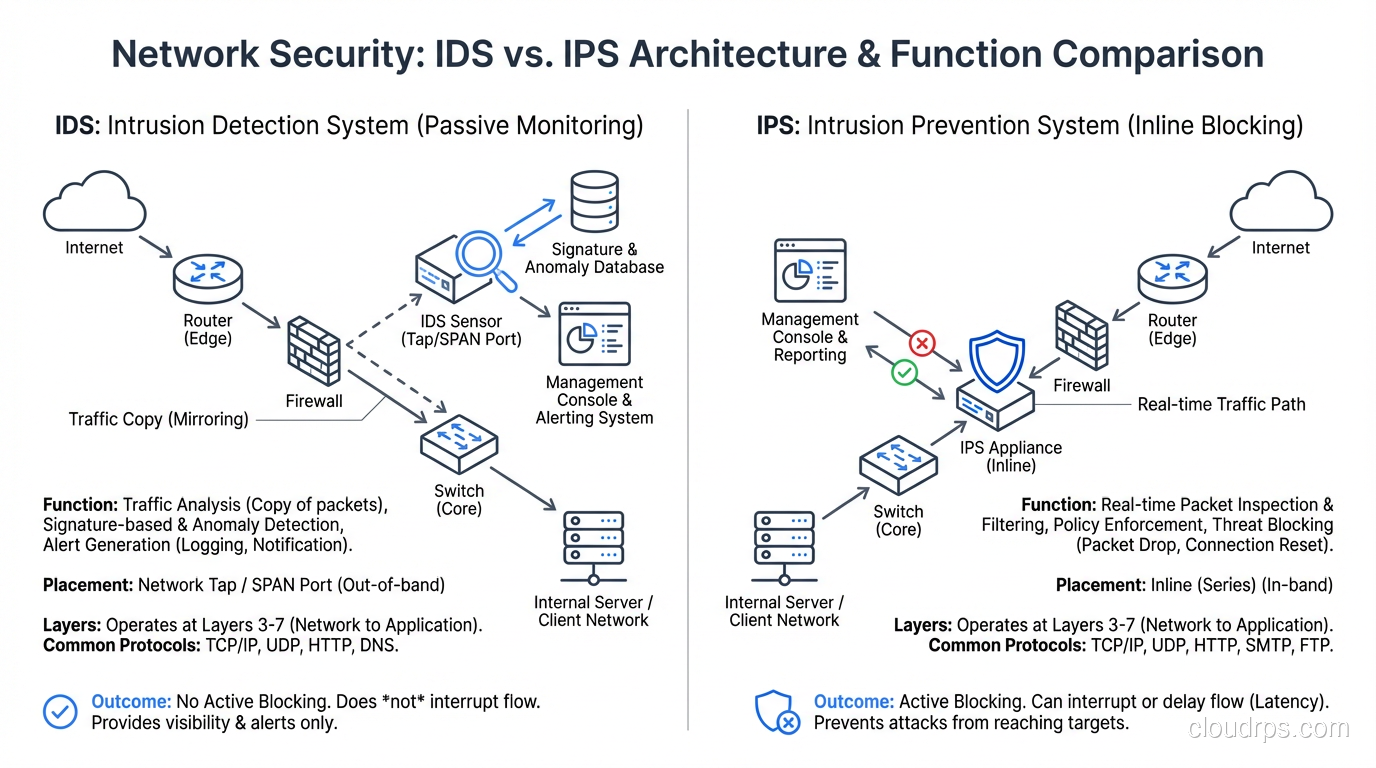
An Intrusion Detection System (IDS) monitors network traffic or system activity and alerts when it identifies suspicious patterns. It’s passive. It watches, it logs, it raises alerts. It does not block anything.
An Intrusion Prevention System (IPS) does everything an IDS does, plus it sits inline in the traffic path and can actively block or modify malicious traffic before it reaches its destination. It’s active. It makes real-time decisions to allow or drop packets.
The analogy I use: an IDS is a security camera. An IPS is a security guard.
A security camera records everything and lets you review after the fact. It deters some threats but doesn’t physically stop anything. A security guard watches, assesses, and intervenes. But a security guard can also make mistakes – tackling the CEO’s kid who forgot their badge is the equivalent of a false positive that drops legitimate production traffic.
That tradeoff – detection accuracy versus action authority – is the central tension in every IDS/IPS deployment.
How Detection Works
Both IDS and IPS use the same detection engines. The difference is what happens after detection. Let me explain the detection mechanisms first.
Signature-Based Detection
The system maintains a database of known attack signatures – specific byte patterns, protocol anomalies, or behavior sequences associated with known exploits. When traffic matches a signature, an alert fires (IDS) or the traffic is blocked (IPS).
Signature databases are maintained by security vendors and open-source communities. Snort and Suricata, the two dominant open-source engines, have rule sets maintained by Emerging Threats, Snort’s Talos team, and community contributors.
A typical signature rule (Snort format) looks like:
alert tcp $EXTERNAL_NET any -> $HOME_NET 445 (msg:"EXPLOIT MS17-010 EternalBlue SMB";
content:"|ff|SMB"; offset:4; depth:4; content:"|23 00 00 00 07 00|";
distance:56; within:6; sid:2024218; rev:2;)
This rule triggers on SMB traffic that matches the specific byte pattern used by the EternalBlue exploit. Signature detection is fast, has well-understood false positive characteristics, and catches known threats reliably. Its weakness is zero-day attacks – if there’s no signature, there’s no detection.
Anomaly-Based Detection
Instead of matching known bad patterns, anomaly detection builds a statistical model of normal behavior and flags deviations. This can detect novel attacks that don’t match any known signature.
Anomaly-based systems learn what “normal” looks like during a baseline period: typical packet sizes, protocol distributions, connection patterns, bandwidth profiles. Deviations beyond a configurable threshold trigger alerts.
The challenge with anomaly detection is the false positive rate. Networks are noisy. A new application deployment, a backup job, a conference call with fifty participants – all create traffic patterns that deviate from the baseline. Tuning anomaly thresholds to catch real attacks without drowning in false positives is an ongoing battle.
Protocol Analysis
Deep protocol analysis decodes network traffic according to protocol specifications and flags violations. An HTTP request with an impossibly long header, an SSH connection using a deprecated cipher, DNS queries that exceed normal size limits – these protocol anomalies often indicate attacks or reconnaissance.
This technique is particularly effective against protocol-level exploits and evasion techniques. Attackers frequently abuse protocol edge cases that legitimate software handles normally but exploit code leverages to bypass simpler detection methods.
Behavioral Analysis
Modern IDS/IPS platforms incorporate behavioral analysis that looks at patterns over time rather than individual packets. Repeated failed authentication attempts across many hosts (indicating lateral movement), gradual data exfiltration patterns, beaconing to command-and-control servers – these behaviors only become apparent when you analyze traffic over minutes or hours, not individual packets.
IDS Deployment Patterns
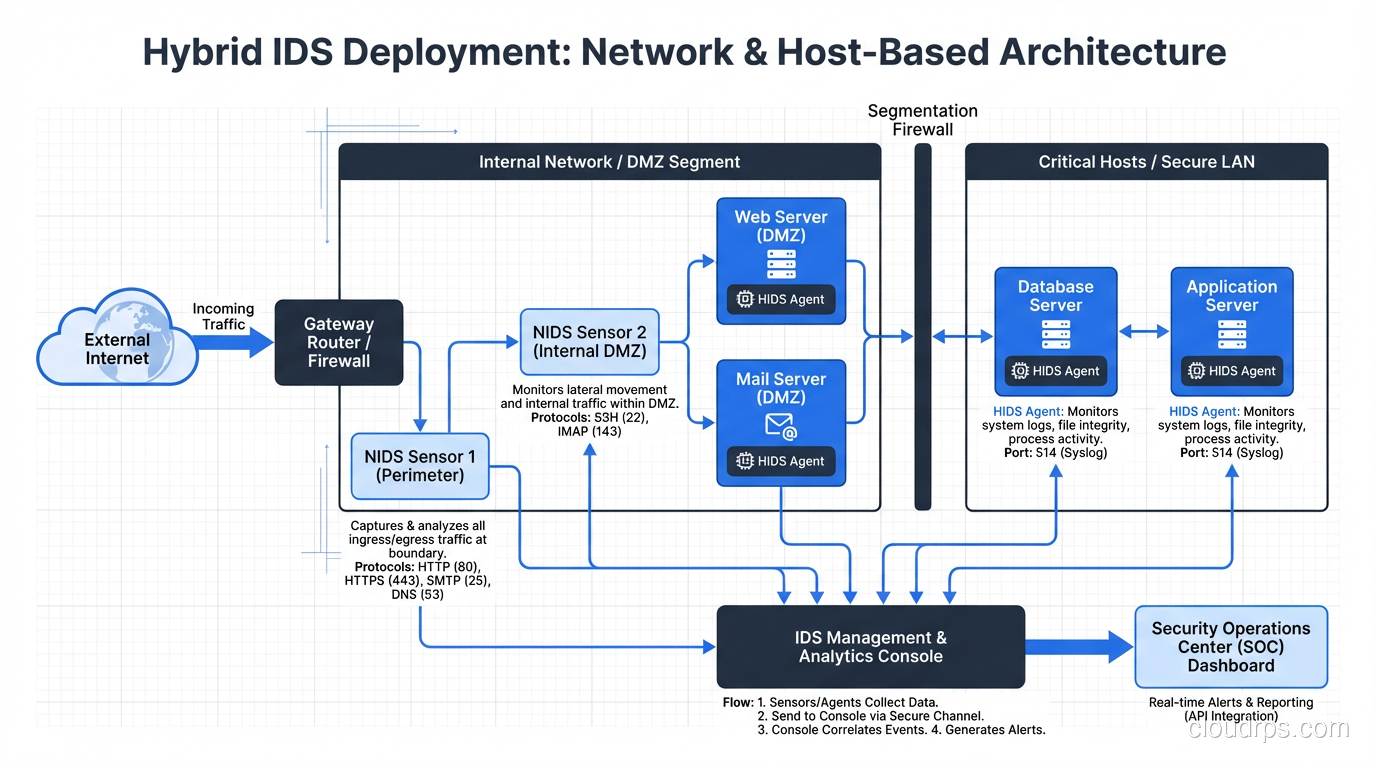
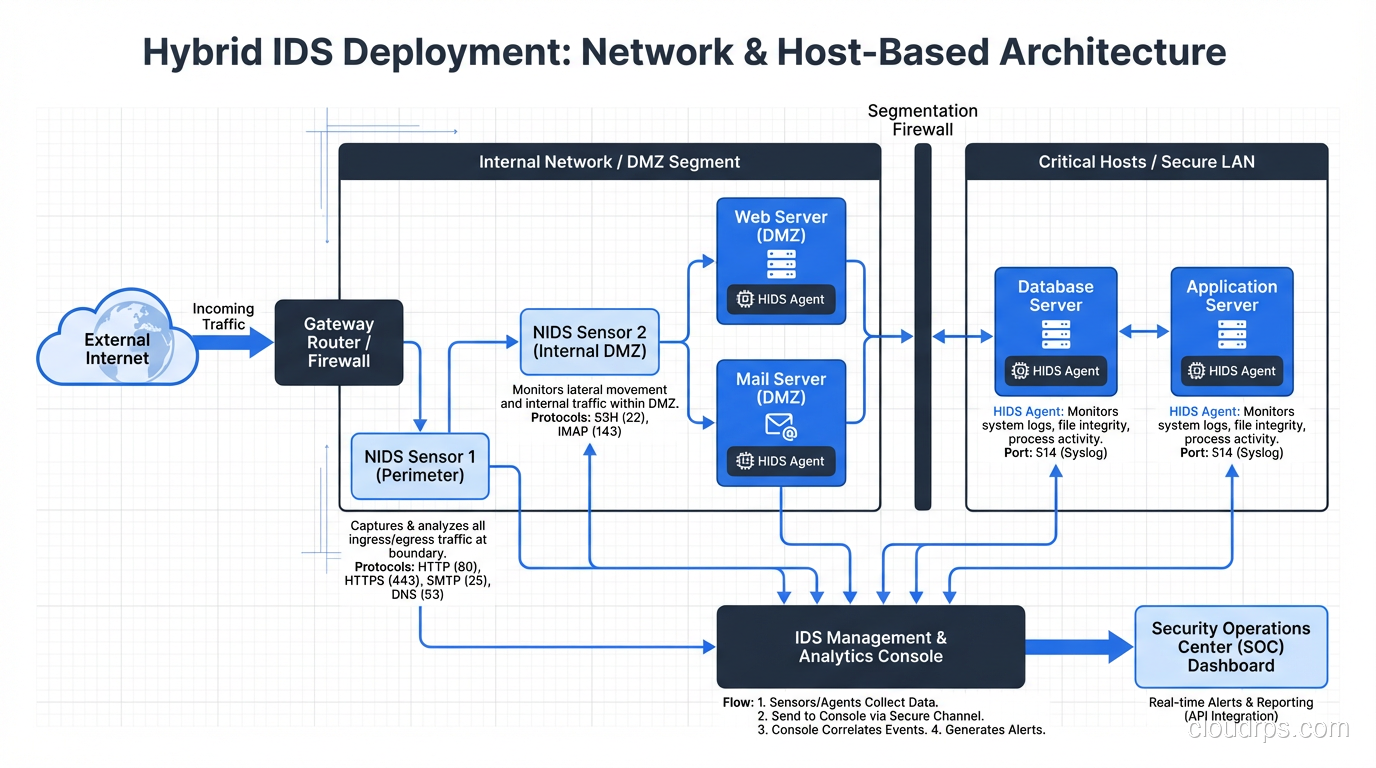
Network IDS (NIDS)
NIDS monitors traffic at strategic network points. Typically deployed on:
- Network perimeter: Monitors all ingress/egress traffic
- Internal segment boundaries: Monitors east-west traffic between zones
- Critical asset fronts: Monitors traffic to high-value targets (databases, domain controllers)
NIDS sensors connect to the network through span ports (port mirroring) or network TAPs. TAPs are preferred because they’re passive, introduce no latency, and don’t drop packets under load – span ports can drop mirrored packets when the switch is busy.
Host IDS (HIDS)
HIDS runs on individual systems and monitors local activity: file system changes, registry modifications, log entries, process execution, and network connections. OSSEC and Wazuh are the most common open-source HIDS platforms.
HIDS catches things NIDS misses entirely – encrypted traffic (HIDS sees the decrypted content at the host), local privilege escalation, file integrity violations, and insider threats that don’t generate network anomalies.
The downside is operational overhead. Every host needs an agent. Every agent needs configuration. Across thousands of servers, that’s significant management burden.
IPS Deployment Patterns
IPS must be inline – traffic flows through it, not past it. This changes the architectural requirements significantly.
Inline Network IPS
The IPS sits between network segments, typically between the firewall and the internal network. Every packet passes through the IPS and is either forwarded (clean) or dropped (malicious).
The critical consideration is availability. An inline device that fails can take down the network. IPS deployments require:
- Bypass capability: Hardware bypass (fail-open) that allows traffic to flow if the IPS process crashes
- High availability: Active-passive or active-active clustering
- Performance headroom: The IPS must handle peak traffic volumes without introducing unacceptable latency
I’ve seen IPS deployments that introduced 200ms of latency to production traffic because the engine couldn’t keep up with the rule set complexity at peak load. That’s unacceptable. Performance testing under realistic load is mandatory before production deployment.
Host IPS (HIPS)
HIPS runs on individual hosts and can block malicious activity in real time. Modern endpoint detection and response (EDR) platforms have largely absorbed this function, combining host-based intrusion prevention with behavioral analysis, threat intelligence, and incident response capabilities.
IDS vs IPS: The Decision Framework
After deploying both across dozens of environments, here’s my honest assessment of when each is appropriate.
Choose IDS When:
- You’re starting out. If you don’t have mature detection and response processes, an IPS will either block too much (causing outages) or be so permissive it adds no value. Start with IDS, build your tuning discipline, and graduate to IPS.
- You can’t afford inline downtime risk. Some environments (trading floors, medical devices, industrial control systems) cannot tolerate the availability risk of an inline device.
- You need visibility into encrypted east-west traffic. NIDS with TLS decryption or HIDS on endpoints provides visibility without the inline risk.
- Compliance requires monitoring but not blocking. Some compliance frameworks mandate intrusion detection without requiring prevention.
Choose IPS When:
- You have mature security operations. A SOC that can manage the rule set, tune false positives, and respond to blocked traffic inquiries.
- You’re protecting internet-facing infrastructure. Known exploit traffic from the internet should be dropped, period. There’s no reason to let a Heartbleed probe or EternalBlue exploit reach your servers.
- You need automated response speed. Network attacks move faster than humans. By the time an analyst reviews an IDS alert, the damage may be done. IPS acts in microseconds.
- Your Zero Trust architecture requires enforcement points. IPS at segment boundaries enforces the principle that all traffic is untrusted.
The Hybrid Approach (What I Actually Deploy)
In practice, I almost always deploy both. IPS inline at the perimeter and between critical trust boundaries, with aggressive rules for known bad traffic. IDS in detection mode on internal segments and high-value targets, with broader rule sets tuned for visibility.
The IPS drops the obvious attacks. The IDS catches the subtle ones. Together, they cover significantly more of the threat landscape than either alone.
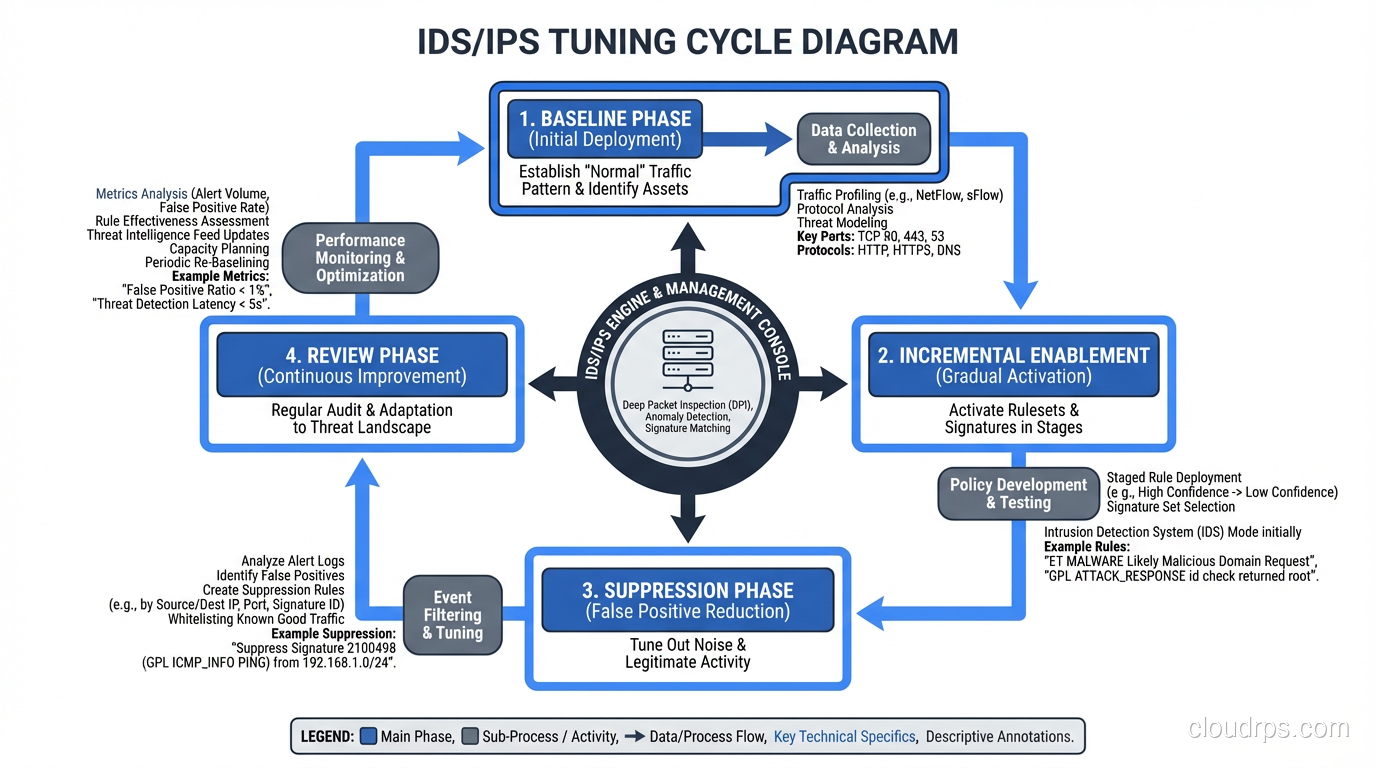
Tuning: Where Deployments Succeed or Fail
If I had to name the single factor that determines whether an IDS/IPS deployment succeeds, it’s tuning. Out-of-the-box rule sets generate too many alerts for any team to process, and the noise drowns out real attacks.
Establish a Baseline
Before enabling any rules, capture a baseline of your normal traffic patterns. Understand what protocols are in use, what the typical traffic volumes look like, and what applications generate traffic that might look suspicious to generic rules.
Enable Rules Incrementally
Don’t enable the entire rule set on day one. Start with high-confidence, high-severity rules – known exploit signatures, protocol violations, and obvious malware indicators. Add rule categories gradually as you verify they don’t generate excessive false positives.
Threshold and Suppress
Use alert thresholds to batch repeated alerts and suppression rules to silence known false positives for specific source/destination pairs. A printer that triggers the same false positive every five minutes generates 288 useless alerts per day. Suppress it, document why, and move on.
Tune for Your Environment
Generic rules assume generic environments. Your network has specific applications, protocols, and traffic patterns. Tune rules to match:
- Disable rules for protocols you don’t use (why run Microsoft IIS rules if you’re all Nginx?)
- Adjust thresholds based on your traffic volumes
- Create custom rules for application-specific threats
Review and Iterate
Weekly rule review during the first three months, monthly thereafter. Check which rules are generating the most alerts, investigate whether those alerts are true or false positives, and adjust accordingly.
Modern IDS/IPS: Where the Technology Is Heading
The standalone IDS/IPS appliance is evolving into broader platforms:
Next-Generation IPS (NGIPS) combines traditional IPS with application awareness, threat intelligence feeds, and automated rule updates. Cisco’s Firepower and Palo Alto’s Threat Prevention are examples.
Network Detection and Response (NDR) platforms like Darktrace, Vectra, and ExtraHop go beyond signature-based detection to use machine learning for behavioral analysis. They excel at detecting lateral movement, data exfiltration, and insider threats that traditional IDS/IPS miss.
Extended Detection and Response (XDR) unifies network, endpoint, cloud, and email detection into a single platform. This is the direction the industry is heading – breaking down the silos between network IDS, host IDS, and cloud security monitoring.
Cloud-native IDS/IPS is built into cloud platforms. AWS Network Firewall, Azure Firewall Premium, and GCP Cloud IDS provide IDS/IPS functionality integrated with cloud networking. If your workloads are in the cloud, these are often the right starting point.
Lessons From the Trenches
Alert fatigue is the real enemy. I’ve watched security teams miss genuine compromises because the IDS was generating 50,000 alerts per day and the real attack was buried in the noise. Fewer, higher-quality alerts are infinitely better than comprehensive, unmanageable alert floods.
IPS false positives are outages. When your IDS false-positives, someone gets an incorrect alert. When your IPS false-positives, legitimate traffic gets dropped. Treat IPS rule changes with the same rigor as firewall rule changes – change management, testing, and rollback plans.
Encrypted traffic is the blind spot. With pervasive TLS, a network IDS that can’t decrypt traffic is increasingly blind. Either deploy TLS interception (with all its privacy and operational implications) or rely more heavily on endpoint-based detection. The detection strategies for dealing with DDoS attacks have a parallel challenge – you need visibility into traffic that’s increasingly encrypted.
IDS/IPS is not set-and-forget. The threat landscape changes constantly. New exploits are discovered weekly. Rule sets need regular updates, tuning needs regular review, and the security team needs regular training. Budget for the ongoing operational cost, not just the initial deployment.
That Pentium II Snort box from 1998 taught me a lesson I carry to every engagement: the technology is only as good as the process around it. Invest in tuning. Invest in response. Invest in the people who run these systems. The detection engine is the easy part.
Get Cloud Architecture Insights
Practical deep dives on infrastructure, security, and scaling. No spam, no fluff.
By subscribing, you agree to receive emails. Unsubscribe anytime.