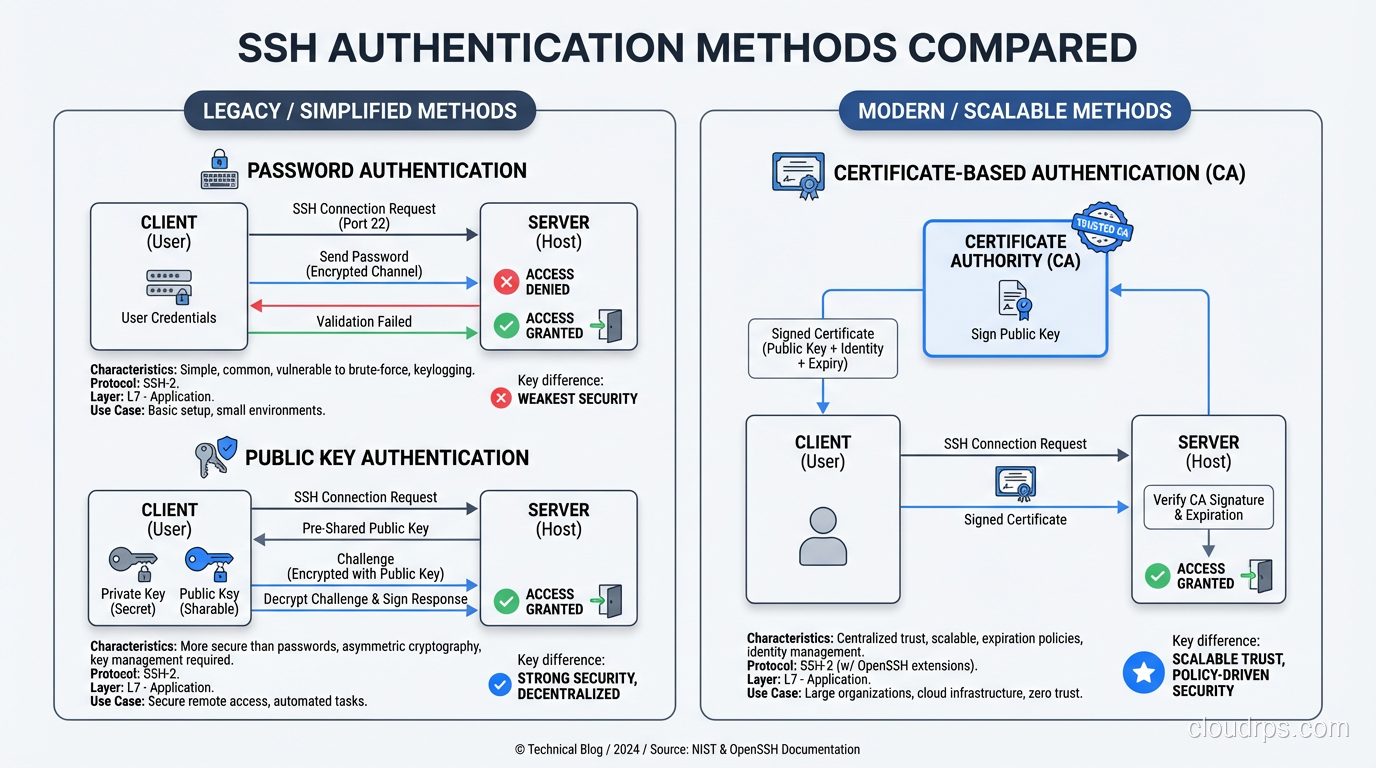
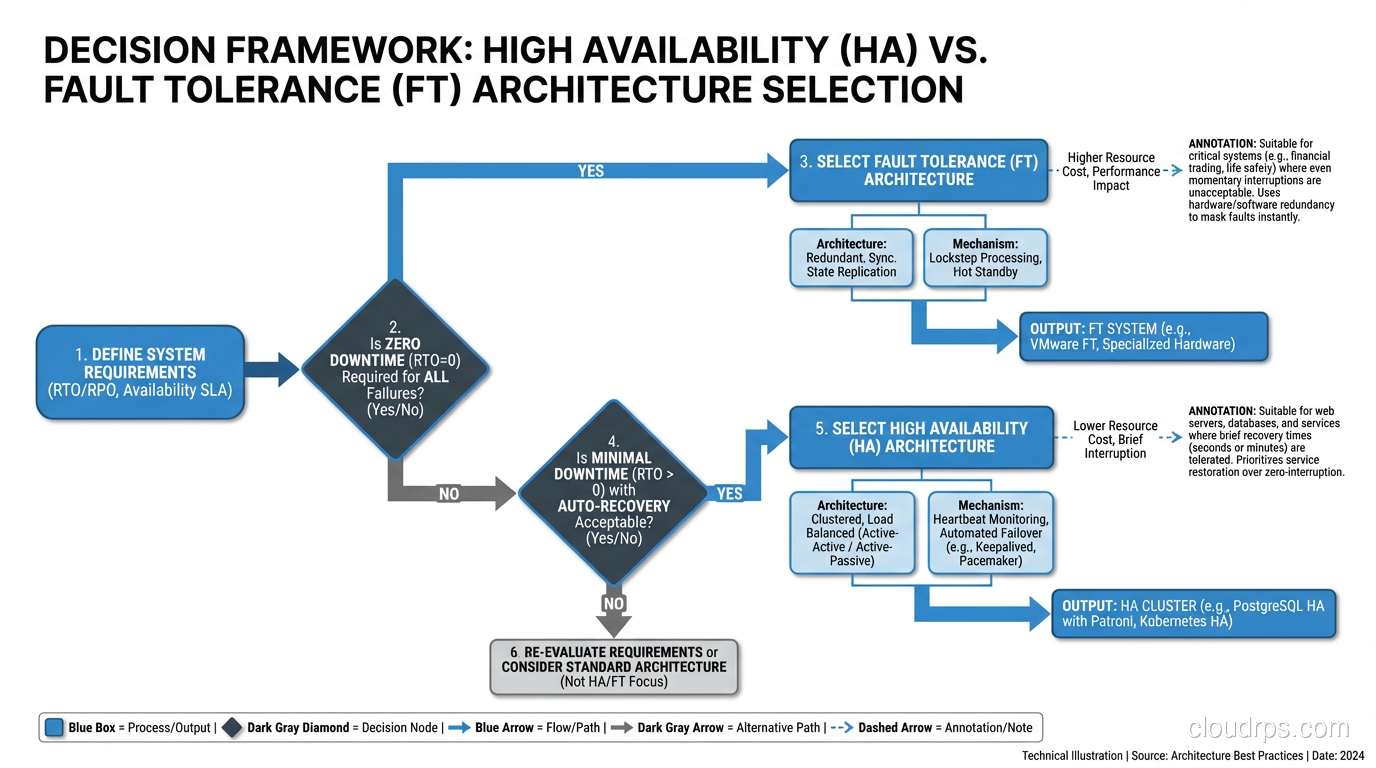
How SSH Works: Key Exchange, Authentication, and Tunneling Under the Hood
A deep dive into how the SSH protocol actually works: key exchange, host verification, authentication methods, and tunneling explained for practitioners.
Deep-dive technical articles on cloud architecture, networking, security, databases, and infrastructure. Written by practitioners who build and scale production systems.
A deep dive into how the SSH protocol actually works: key exchange, host verification, authentication methods, and tunneling explained for practitioners.
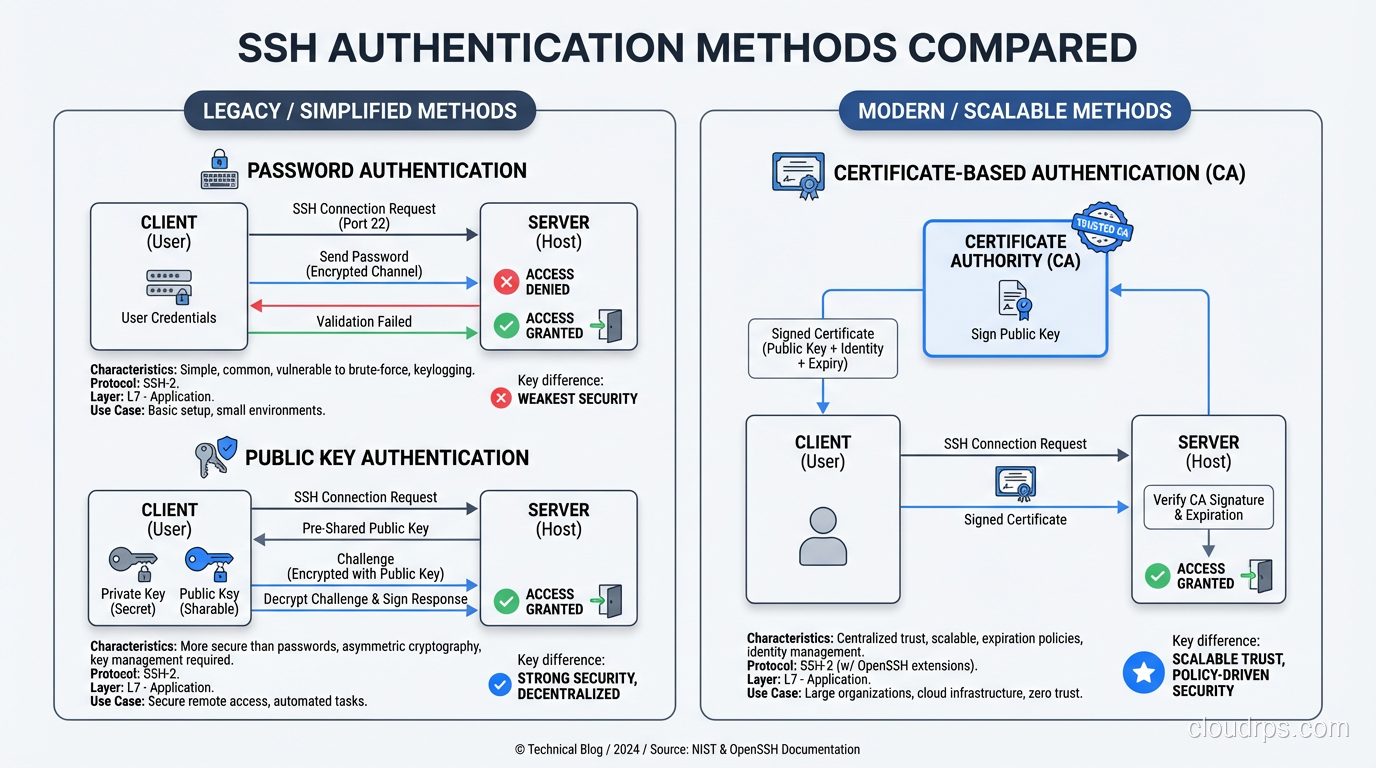
A veteran architect explains the critical difference between fault tolerance and high availability, with real-world examples of when each matters and how to implement both.
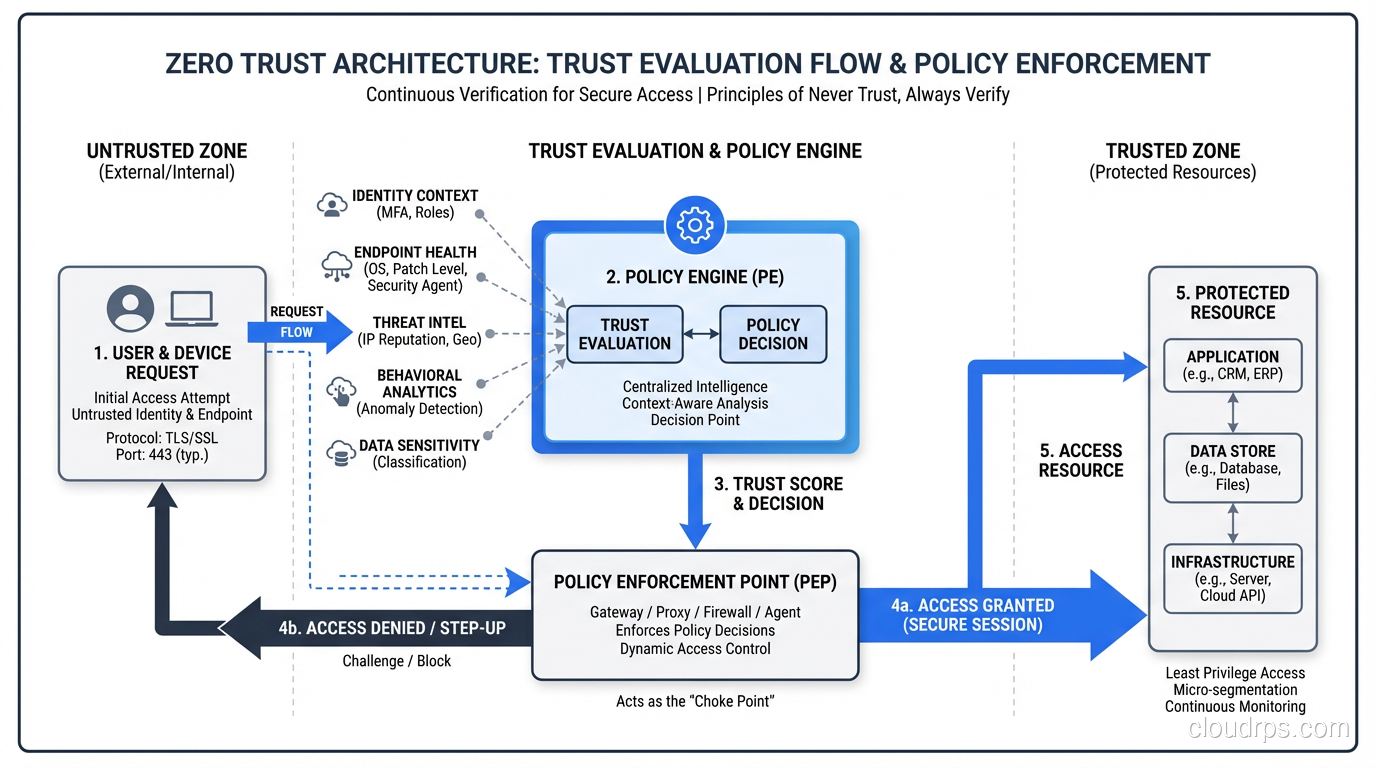
A practical guide to Zero Trust security architecture: core principles, real implementation strategies, and how to move beyond the perimeter model.
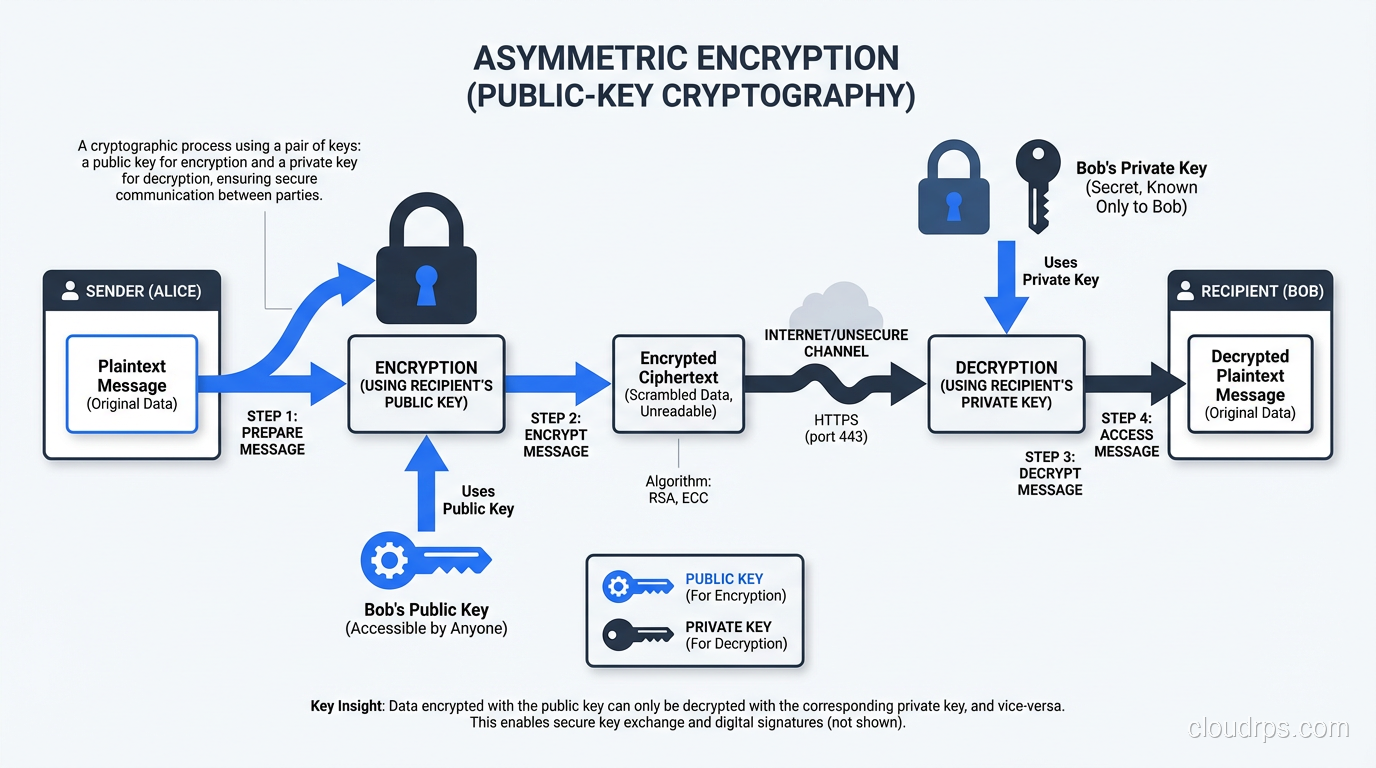
Understand the mechanics of symmetric and asymmetric encryption, compare AES vs RSA vs ECC, and learn how TLS combines both for real-world security.
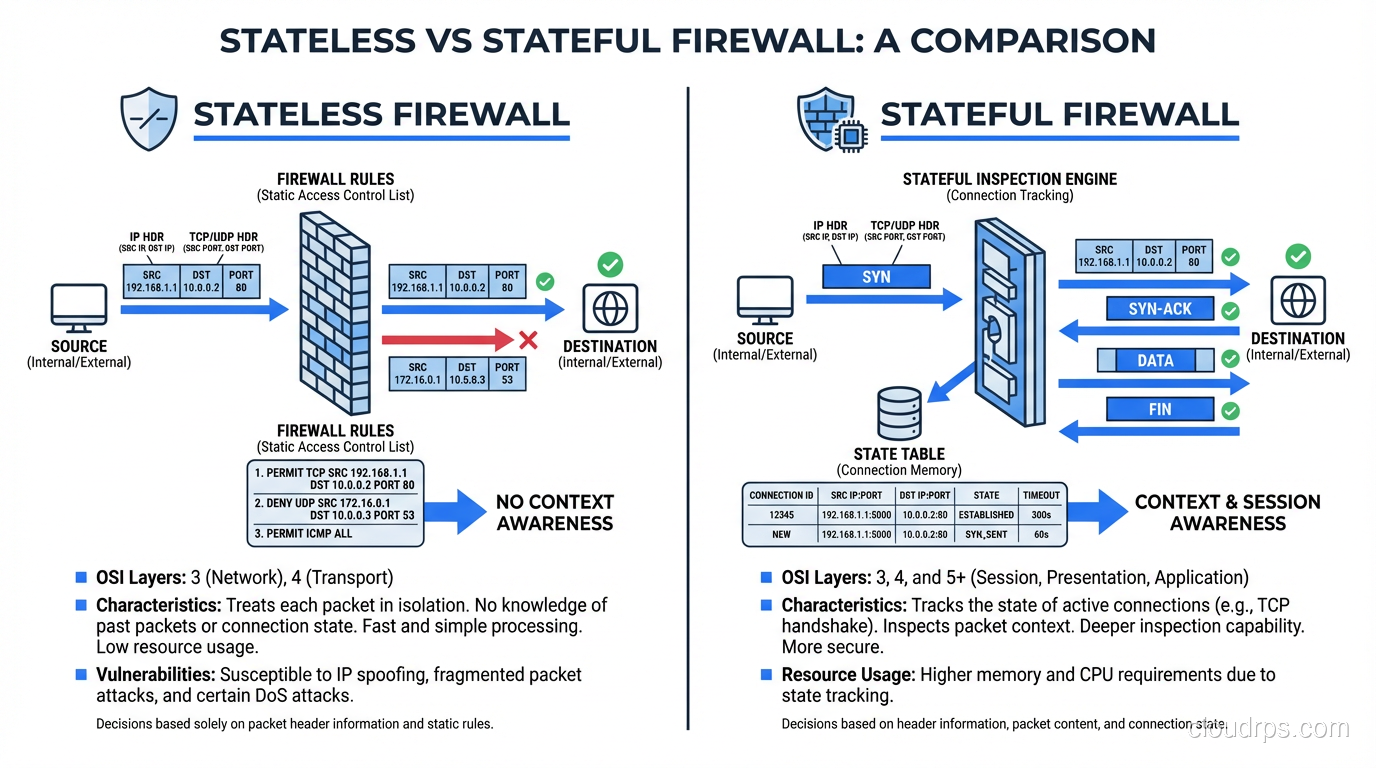
Learn the real differences between stateless and stateful firewalls, how each inspects traffic, and when to deploy them in production network architectures.
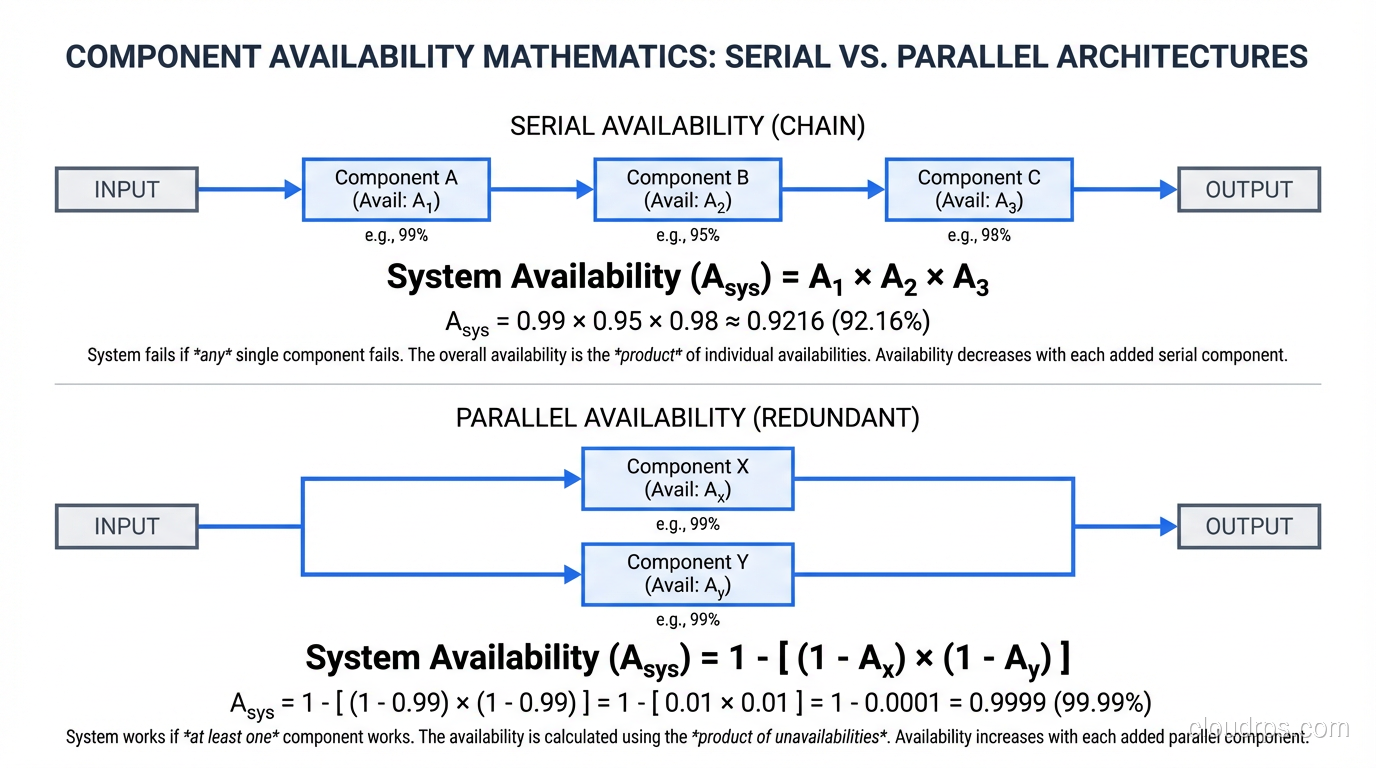
A principal architect with decades of uptime experience explains high availability architecture: the patterns, the math, and the real-world lessons from keeping systems running.
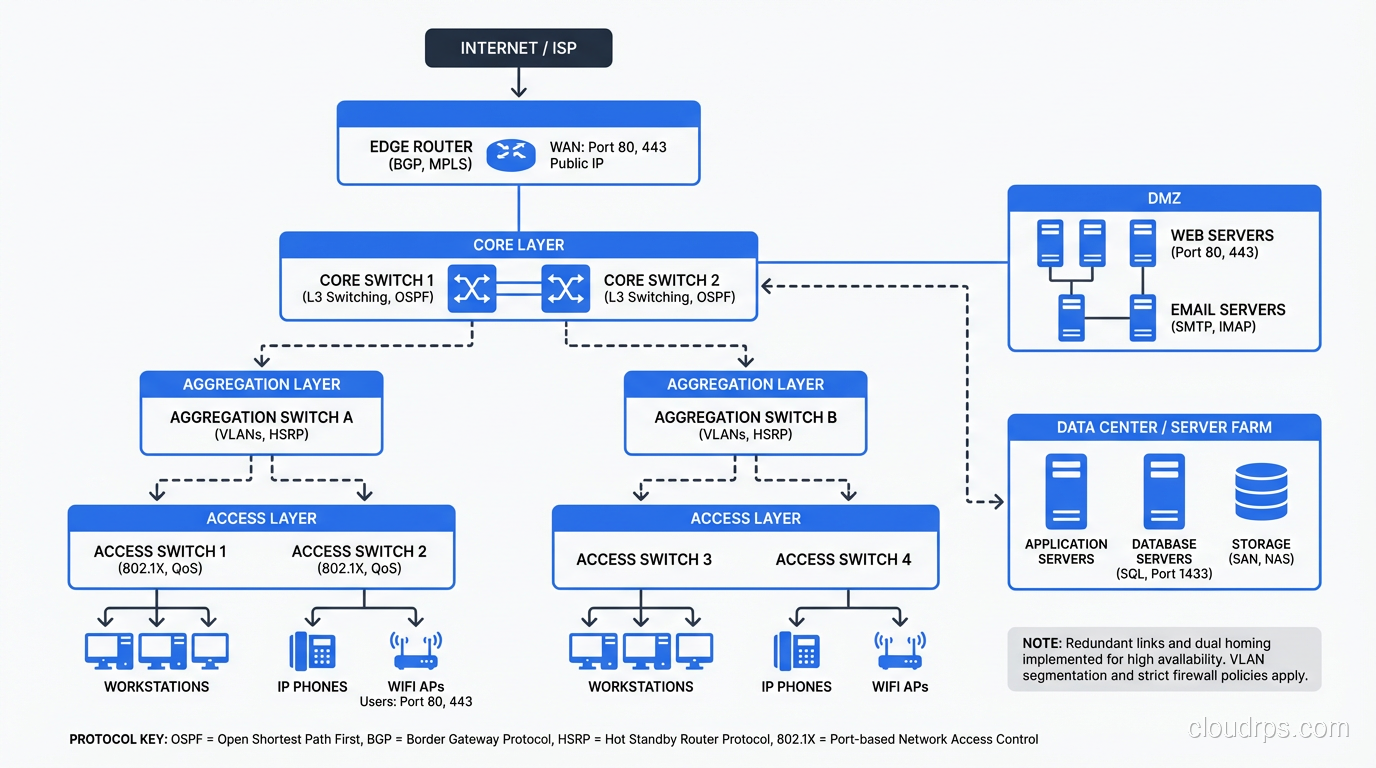
Understand the fundamental differences between routers and switches, how each operates at different network layers, and when to use which in modern network design.
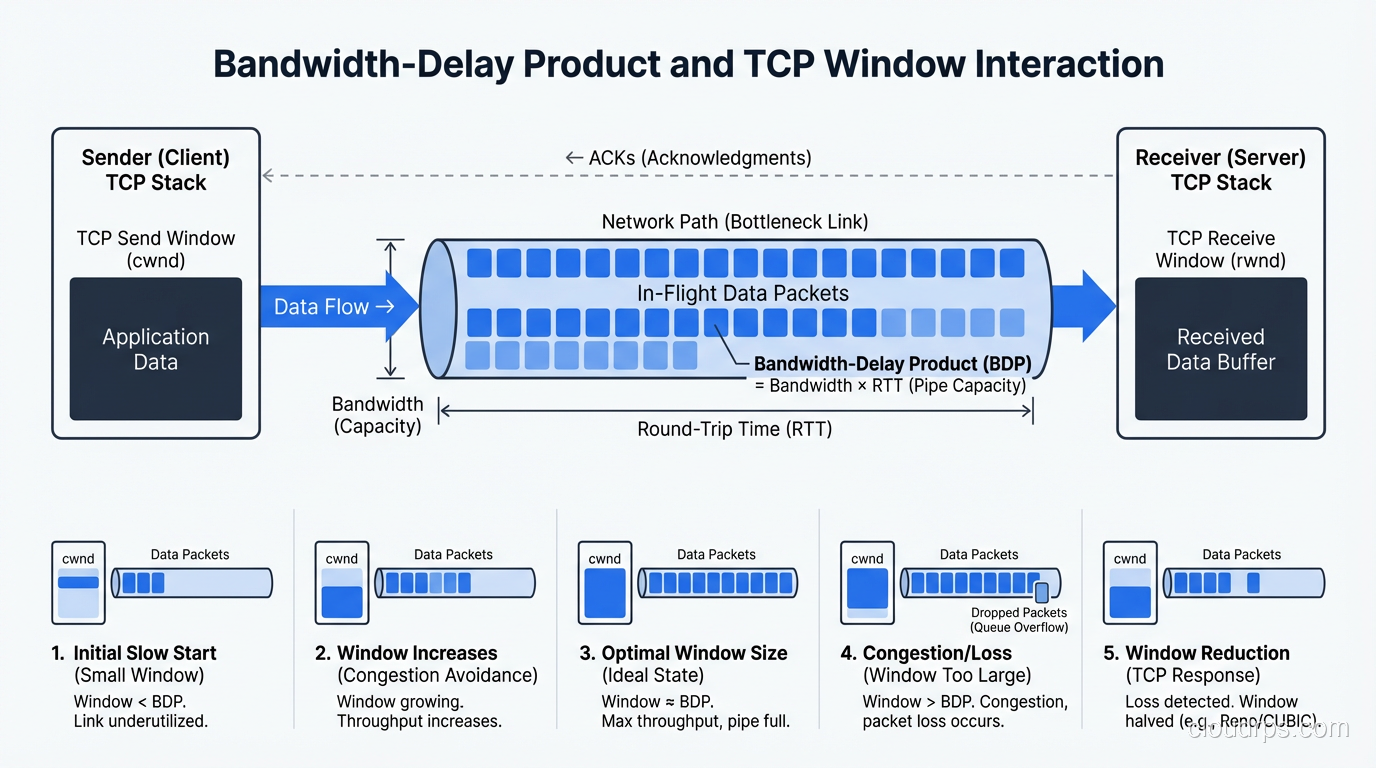
Understand the critical difference between latency and bandwidth, why both matter for performance, and how to optimize each in real-world cloud and network architectures.
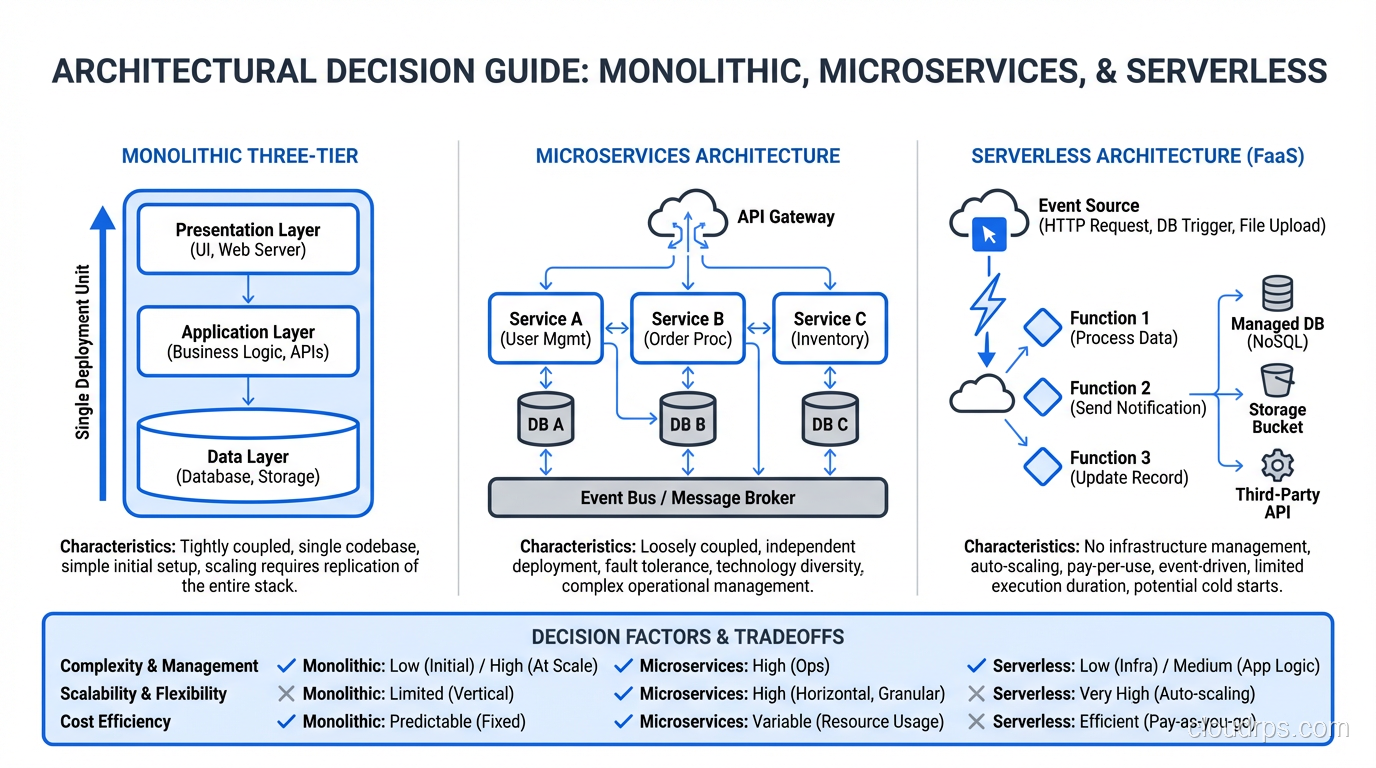
A principal architect explains three-tier architecture from real-world experience: how it works, how to scale each tier, and how modern variants like microservices evolved from it.
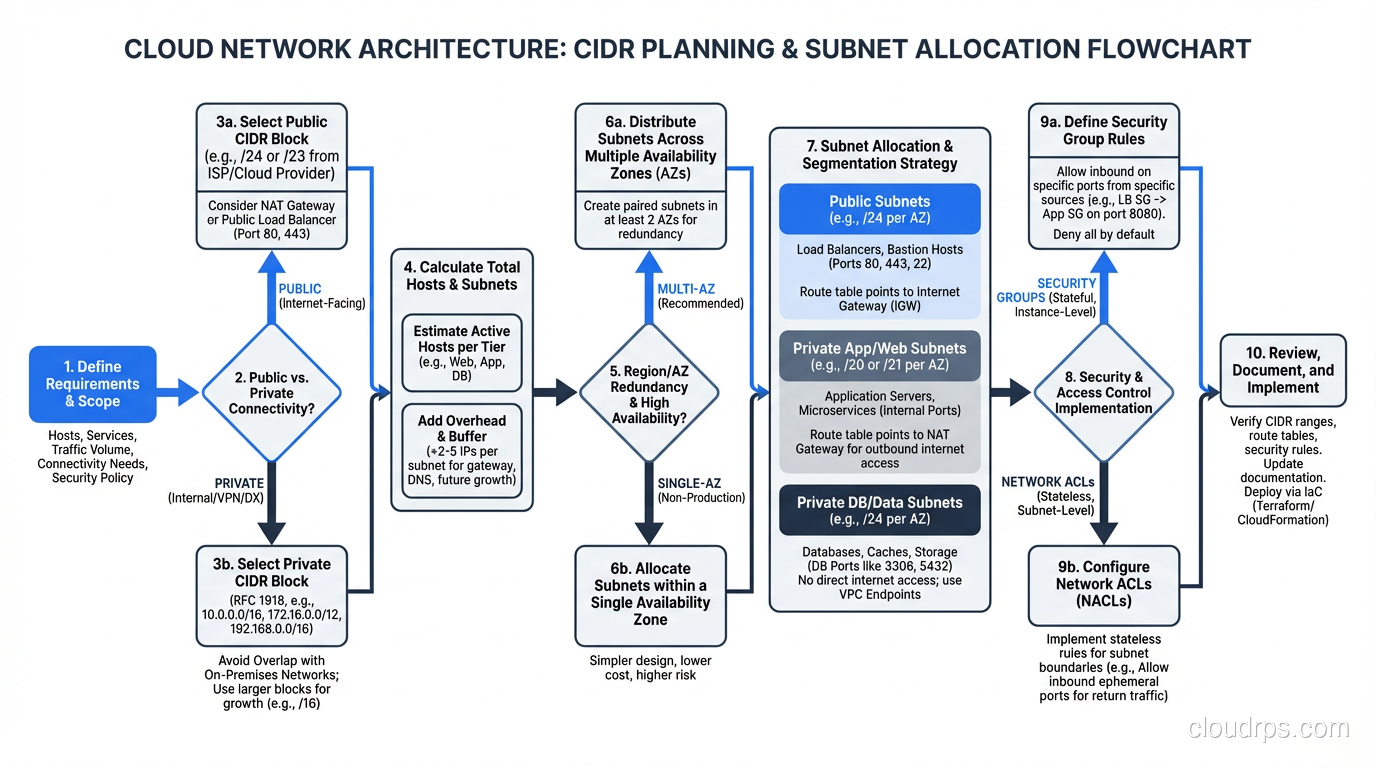
Learn CIDR notation, subnet masks, and how classless addressing replaced the old Class A/B/C system. Practical examples for cloud VPC design and network planning.
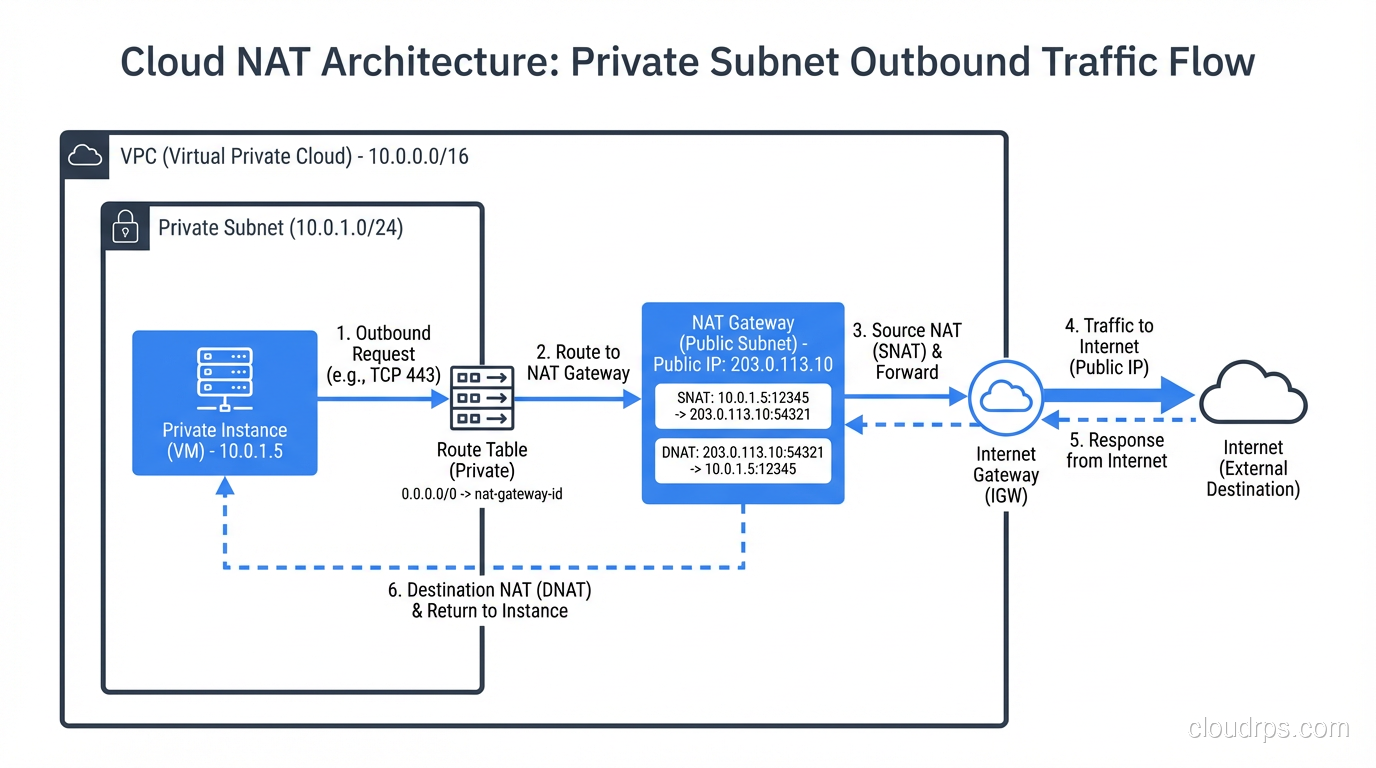
Understand how NAT works, why it exists, and the different types: static NAT, dynamic NAT, PAT, and CGNAT. Real examples from enterprise and cloud networks.
A principal architect breaks down multi-tenancy architecture patterns, isolation models, and the real trade-offs you face when building shared infrastructure for multiple customers.
Practical deep dives on infrastructure, security, and scaling. No spam, no fluff.
By subscribing, you agree to receive emails. Unsubscribe anytime.