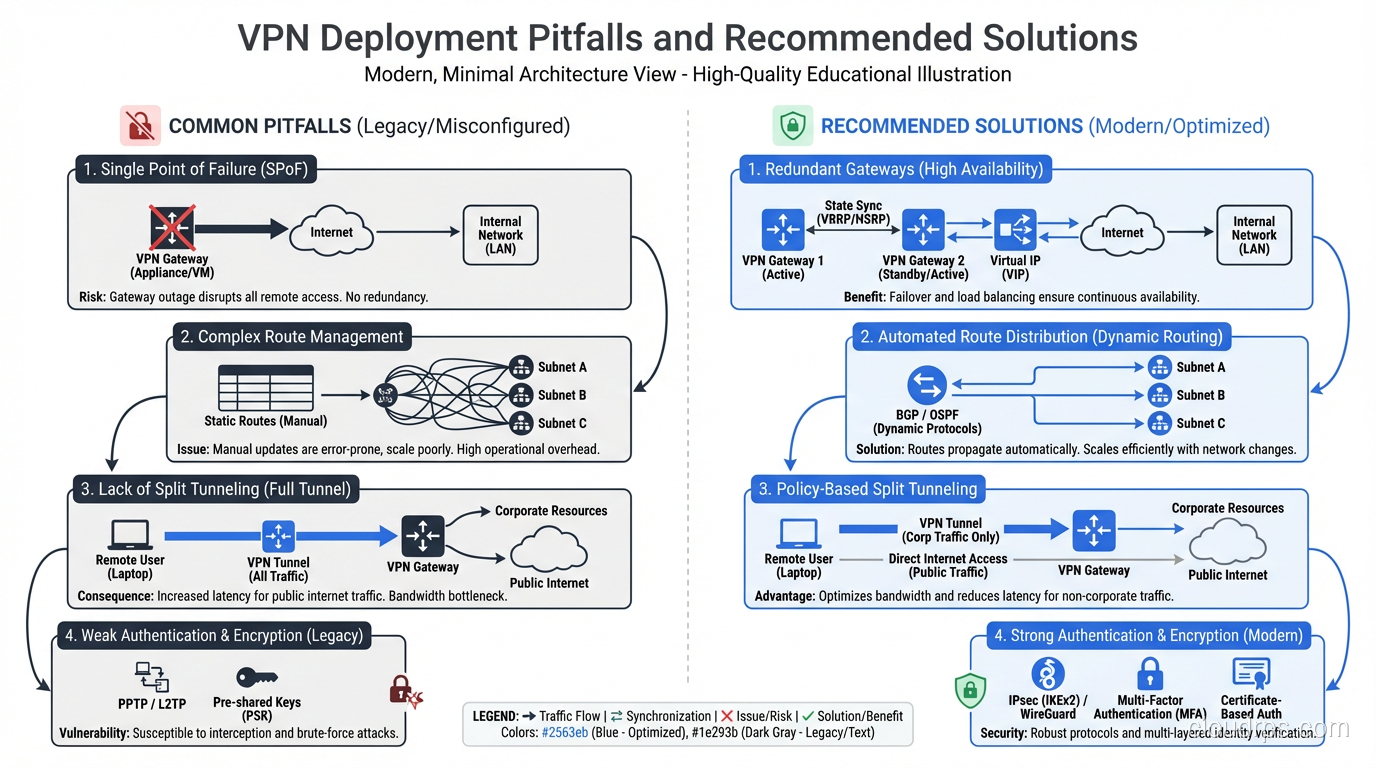
What is a VPN and How Does It Work? Tunneling, Encryption, and Real-World Use
Understand how VPNs work under the hood: tunneling protocols, encryption, split tunneling, and real enterprise use cases beyond just hiding your IP address.
Deep-dive technical articles on cloud architecture, networking, security, databases, and infrastructure. Written by practitioners who build and scale production systems.
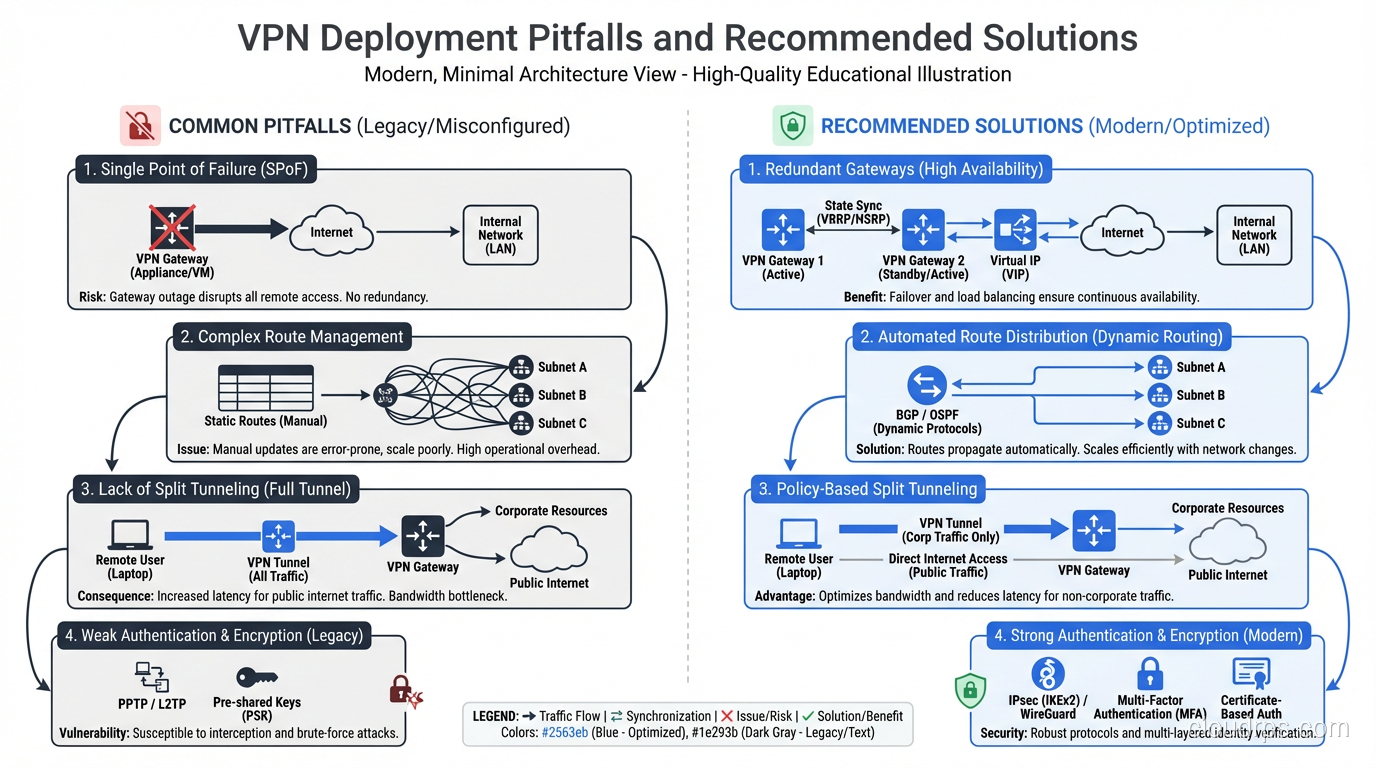
Understand how VPNs work under the hood: tunneling protocols, encryption, split tunneling, and real enterprise use cases beyond just hiding your IP address.
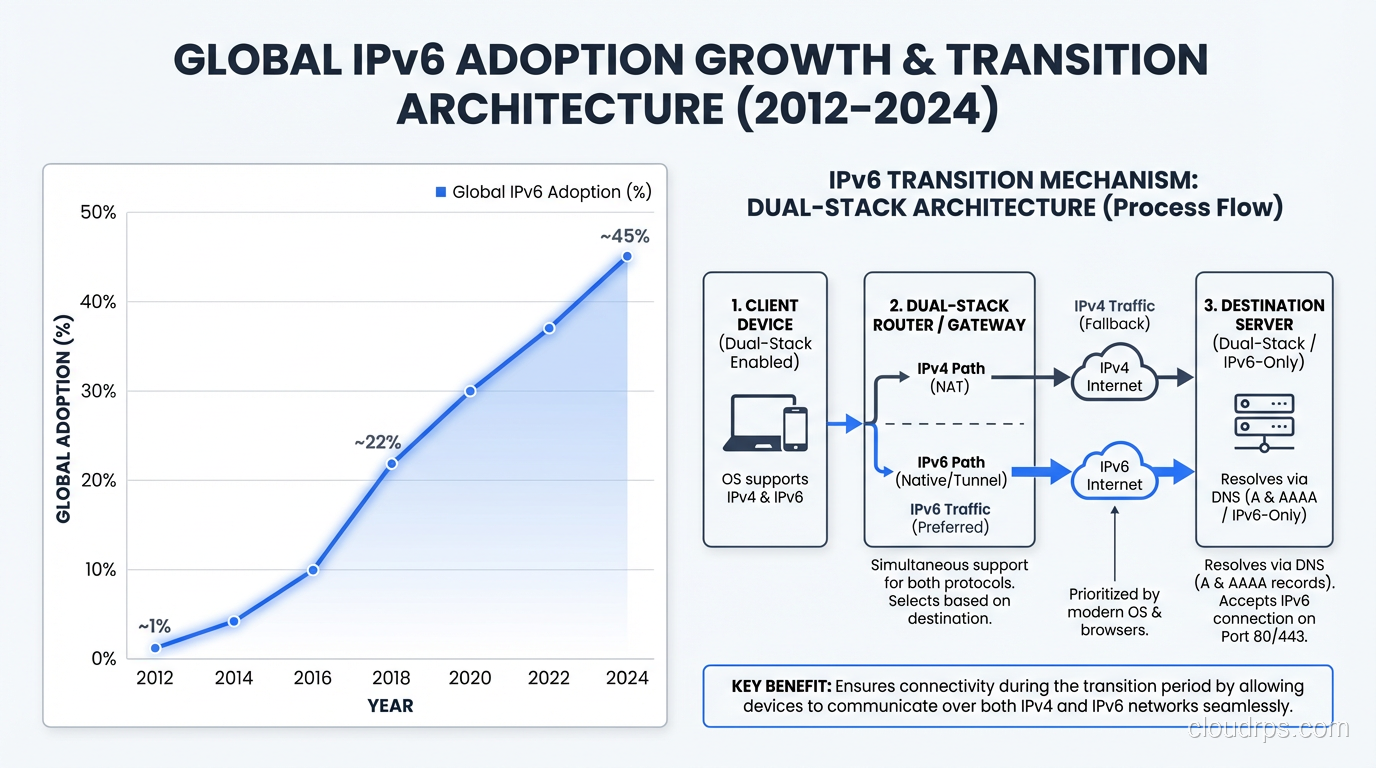
IPv4 addresses have run out. Learn why IPv6 exists, how the exhaustion crisis unfolded, what NAT workarounds cost us, and why the transition matters now.
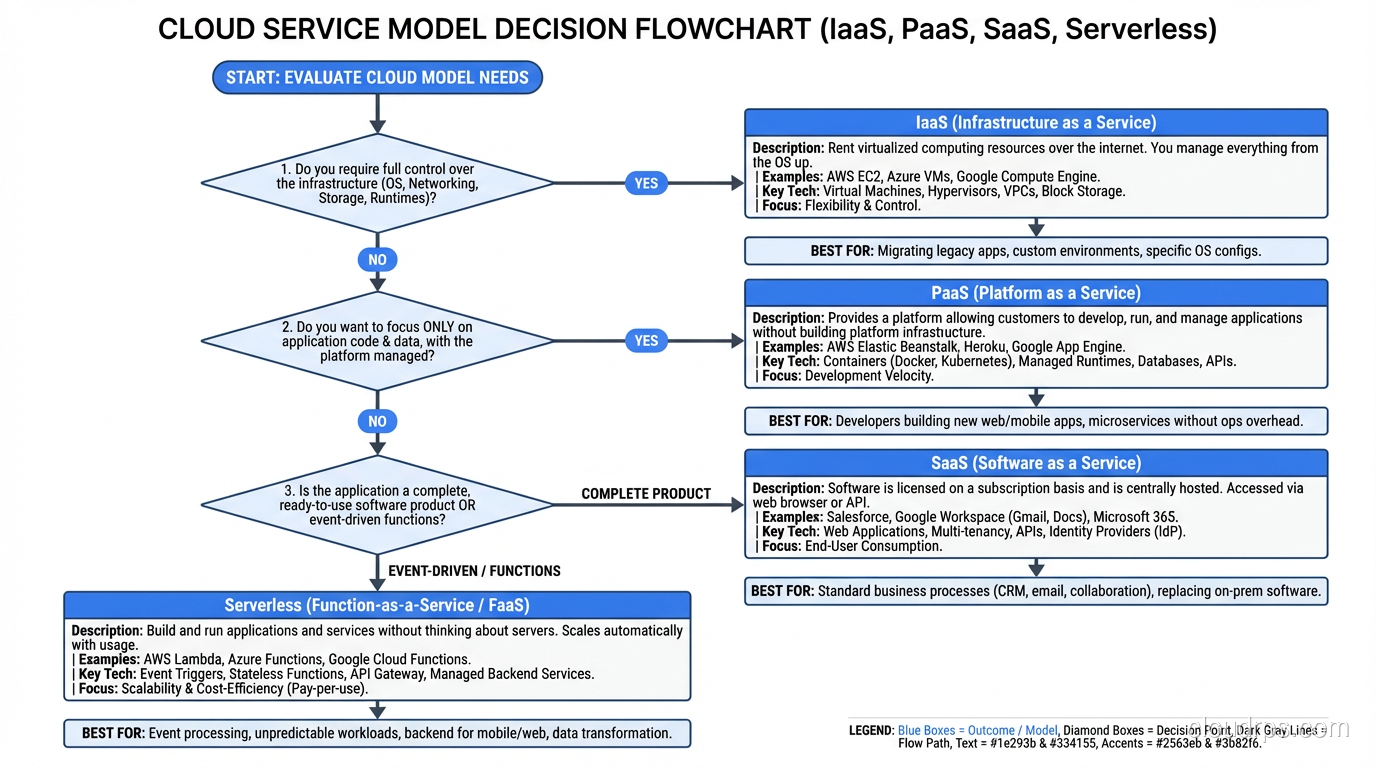
A principal cloud architect breaks down IaaS, PaaS, and SaaS with real-world examples, explaining when each model fits and the trade-offs most guides skip.
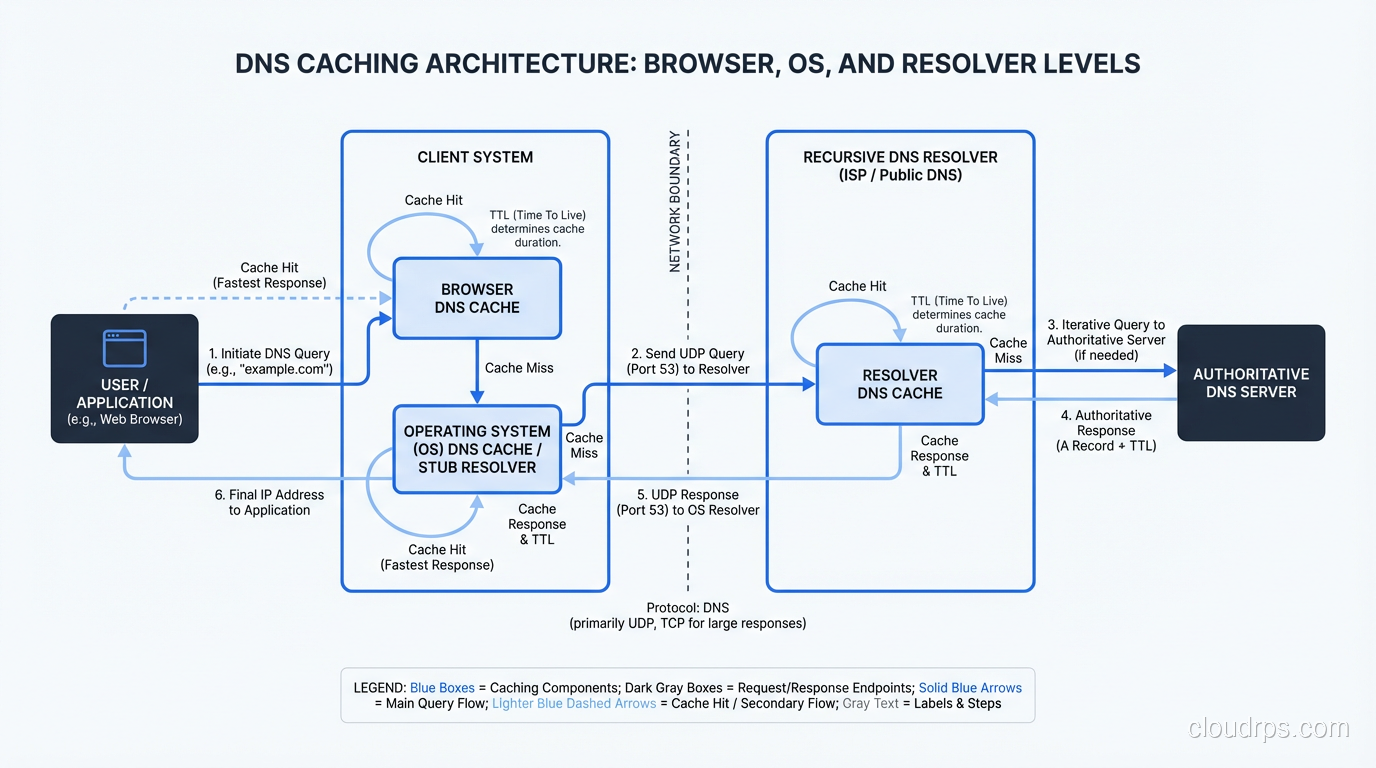
Learn exactly how DNS resolution works from browser to authoritative nameserver. Recursive resolvers, caching, TTLs, and what happens when lookups fail.
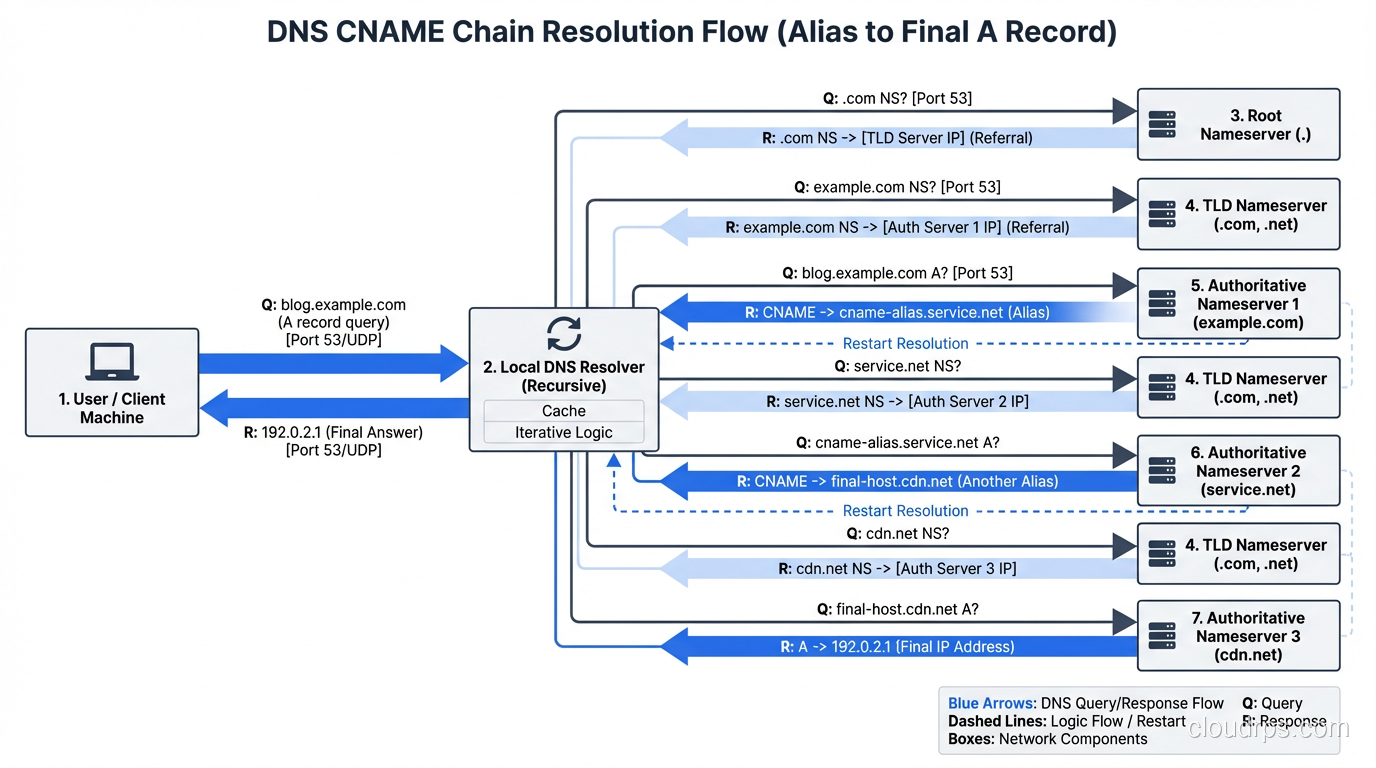
A practical guide to every DNS record type you'll encounter: A, AAAA, CNAME, MX, TXT, NS, SOA, SRV, CAA, PTR with real configuration examples.
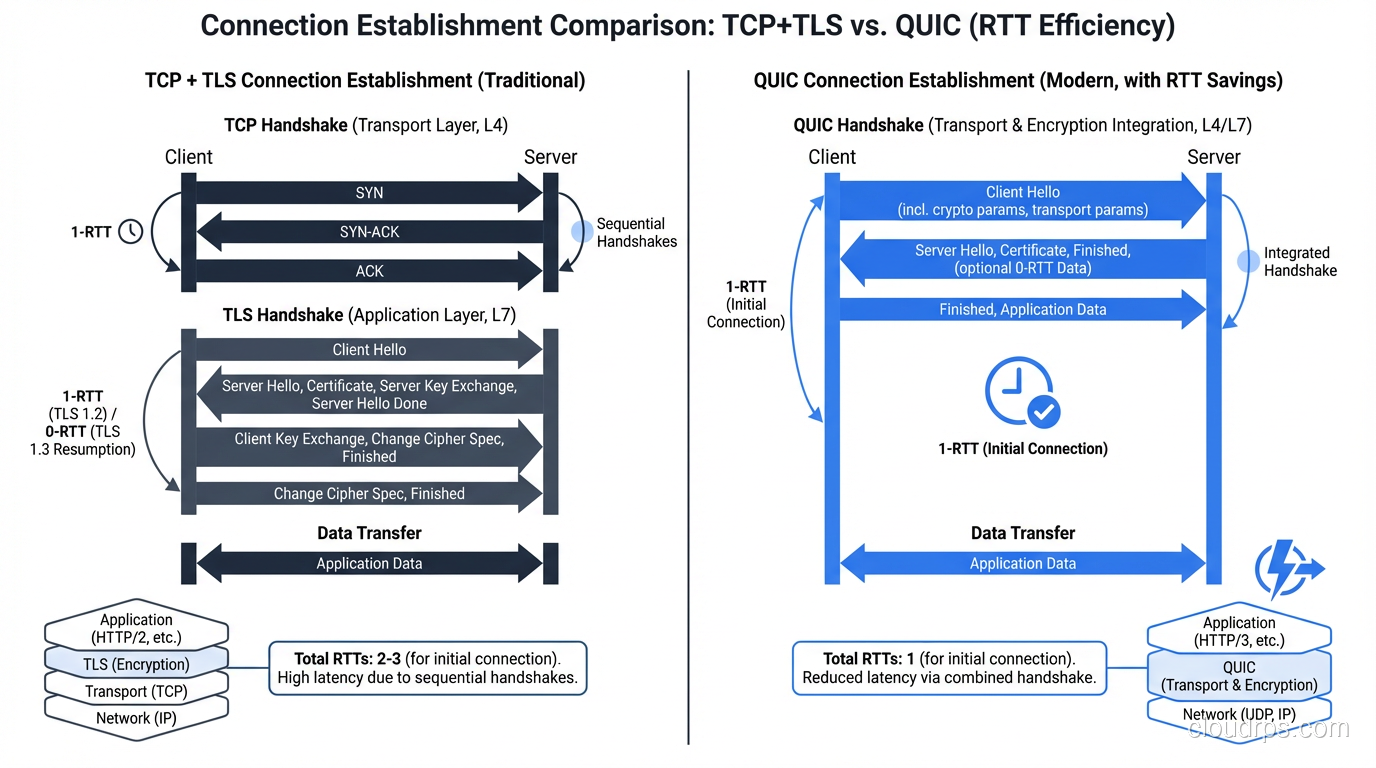
A thorough comparison of TCP and UDP covering reliability, performance, use cases, and when QUIC changes the equation for modern applications.
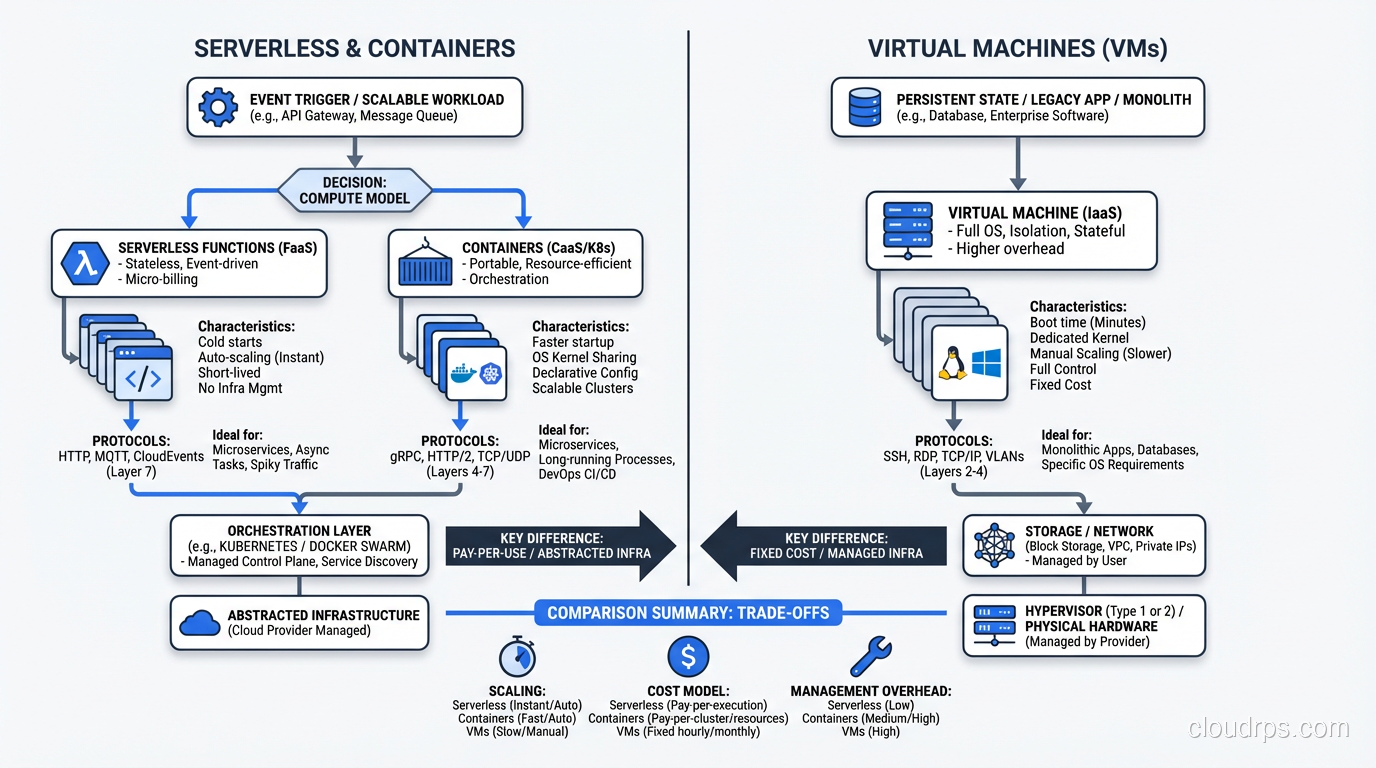
A principal architect with 30 years of infrastructure experience explains what serverless actually means, when it works brilliantly, and when it falls flat.
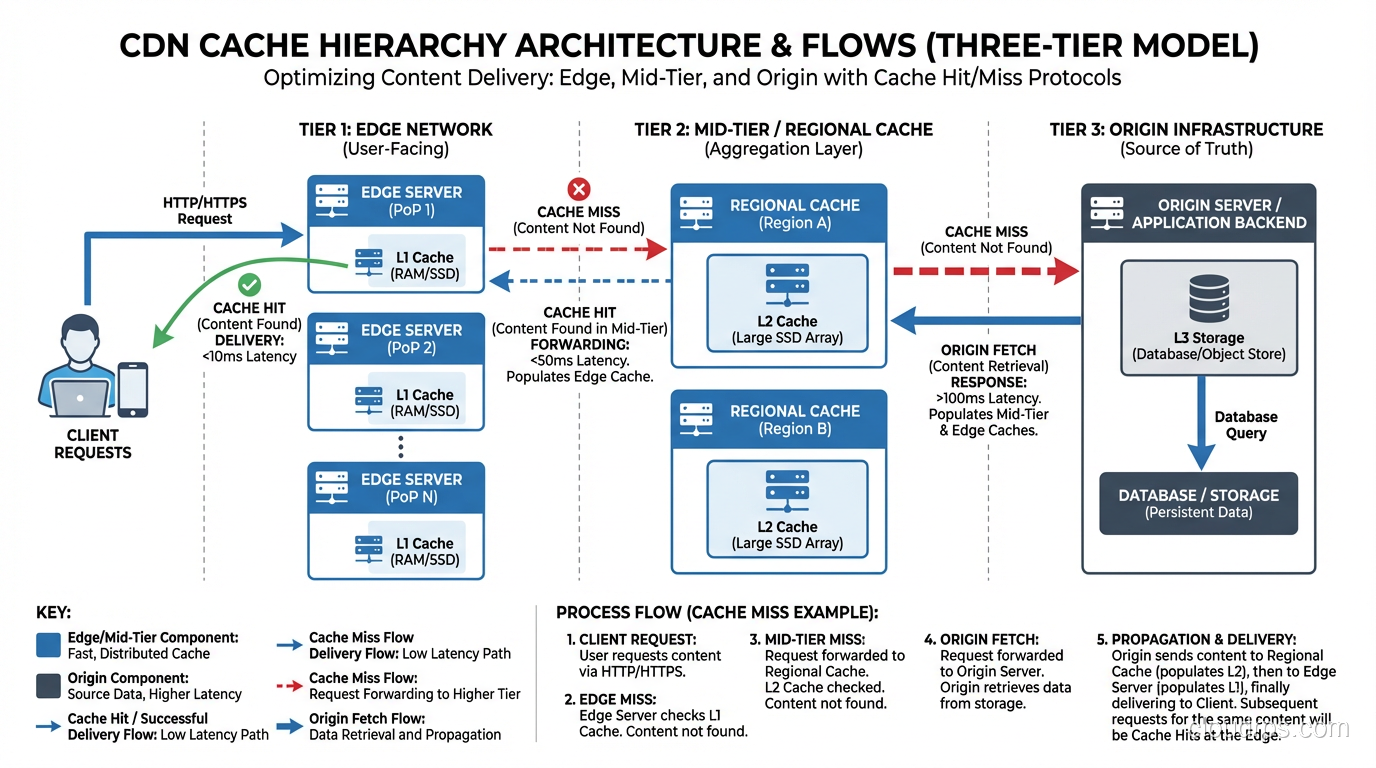
Understand how CDNs cache and deliver content from edge servers, DNS-based routing, cache hierarchies, and when to use (or skip) a CDN.
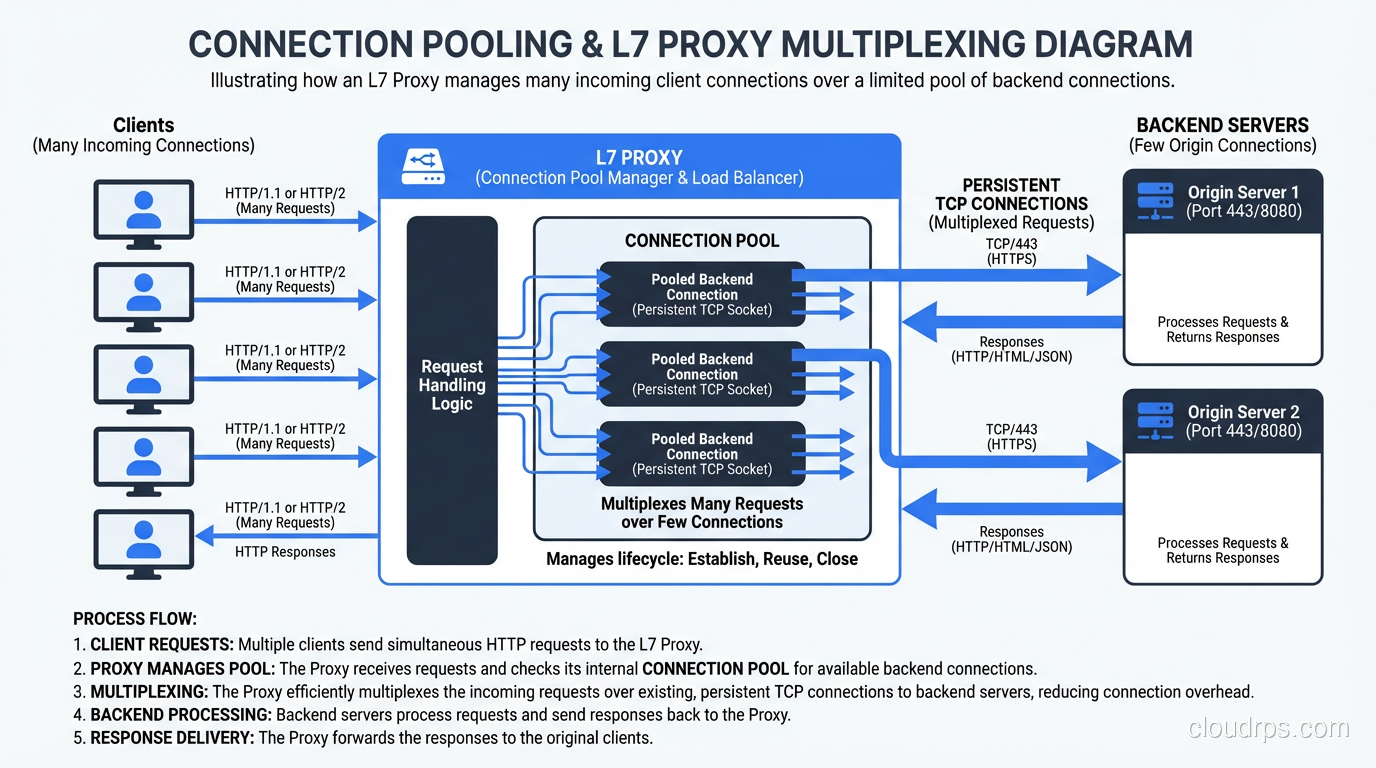
Understand the practical differences between Layer 4 and Layer 7 for load balancers, firewalls, and proxies with real architecture examples.
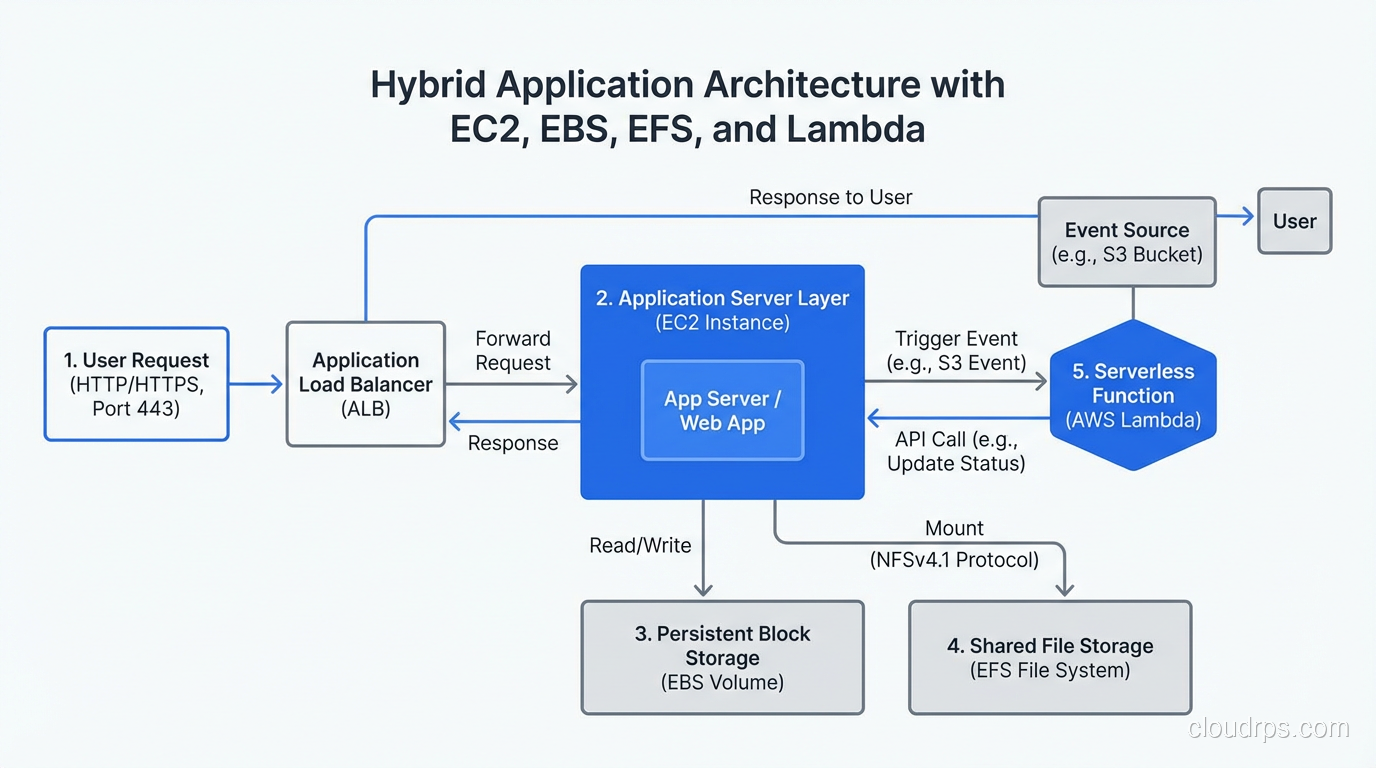
A veteran cloud architect maps AWS compute and storage services to their physical hardware equivalents, explaining what EC2, EBS, EFS, and Lambda really are under the hood.
Master the OSI model's 7 layers with practical examples, real protocols at each layer, and why this framework still matters for troubleshooting.
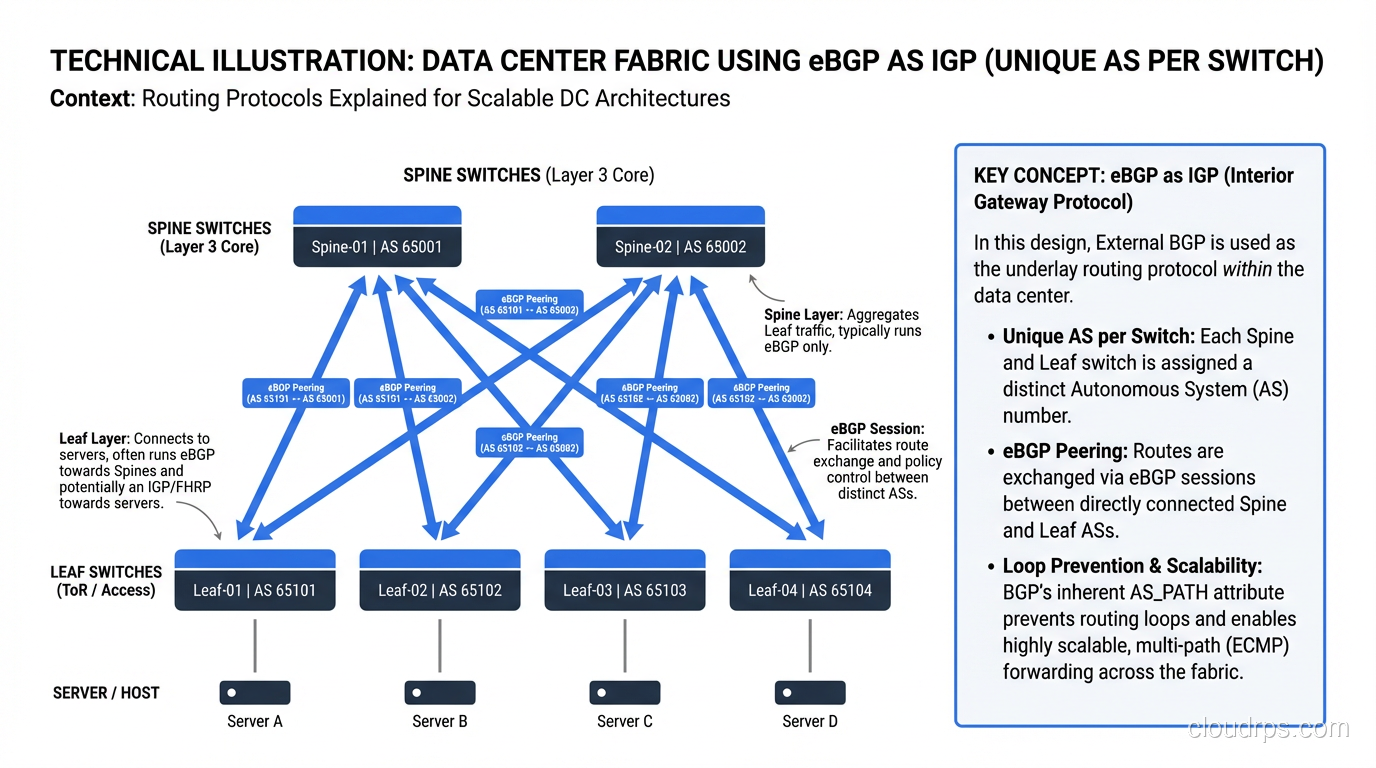
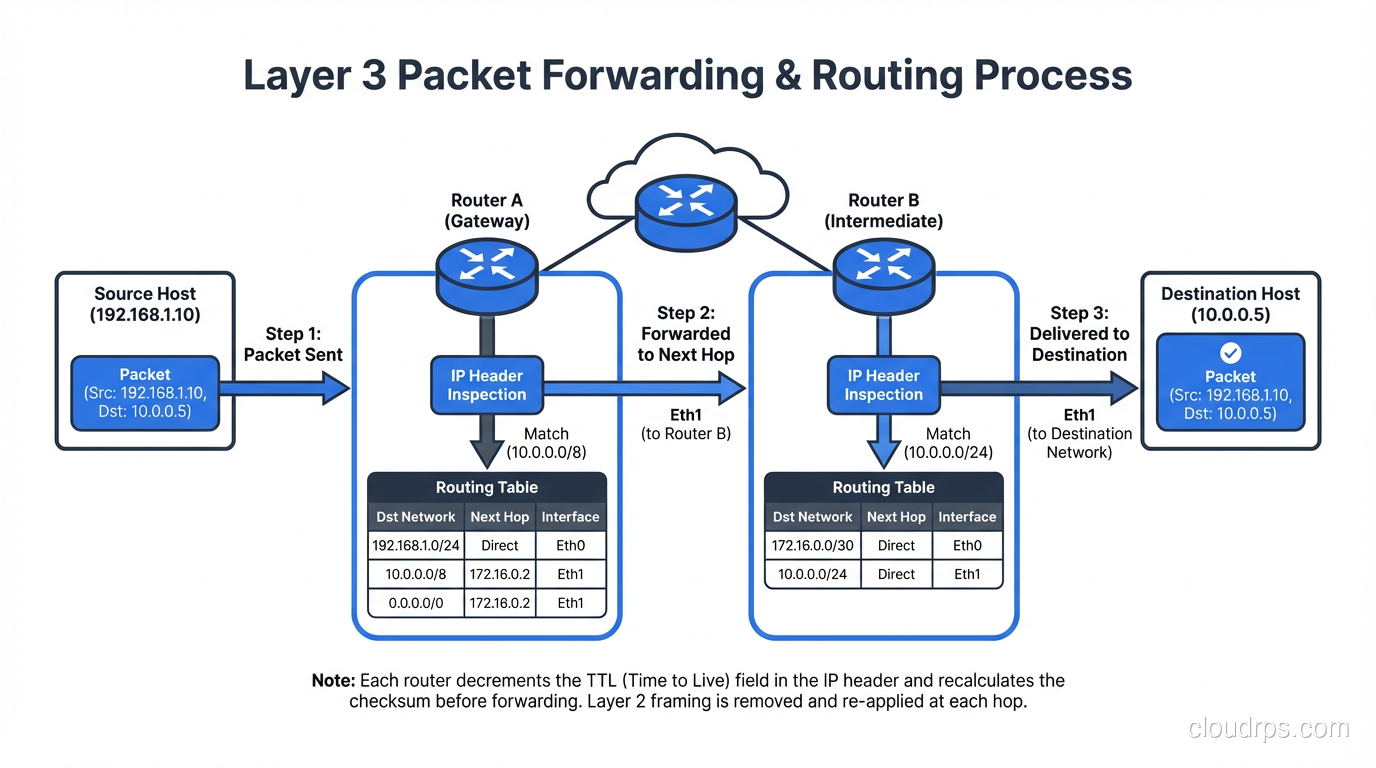
A practical guide to routing protocols: OSPF, BGP, RIP, and EIGRP compared with real-world use cases, configurations, and selection criteria.
Practical deep dives on infrastructure, security, and scaling. No spam, no fluff.
By subscribing, you agree to receive emails. Unsubscribe anytime.