I still remember the first time a junior engineer asked me why their perfectly good ACL rules were dropping legitimate return traffic. They had built what they thought was a tight, secure ruleset, and it was. So tight that it was blocking the response packets from connections their own servers initiated. That was their introduction to the difference between stateless and stateful firewalls, and it is a lesson that sticks with you.
This distinction is one of the most fundamental concepts in network security, and yet I see it misunderstood constantly, even by people who should know better. So let me walk through exactly how each type works, where each one belongs in your architecture, and why getting this wrong can either leave you wide open or break your applications entirely.
What a Firewall Actually Does at the Packet Level
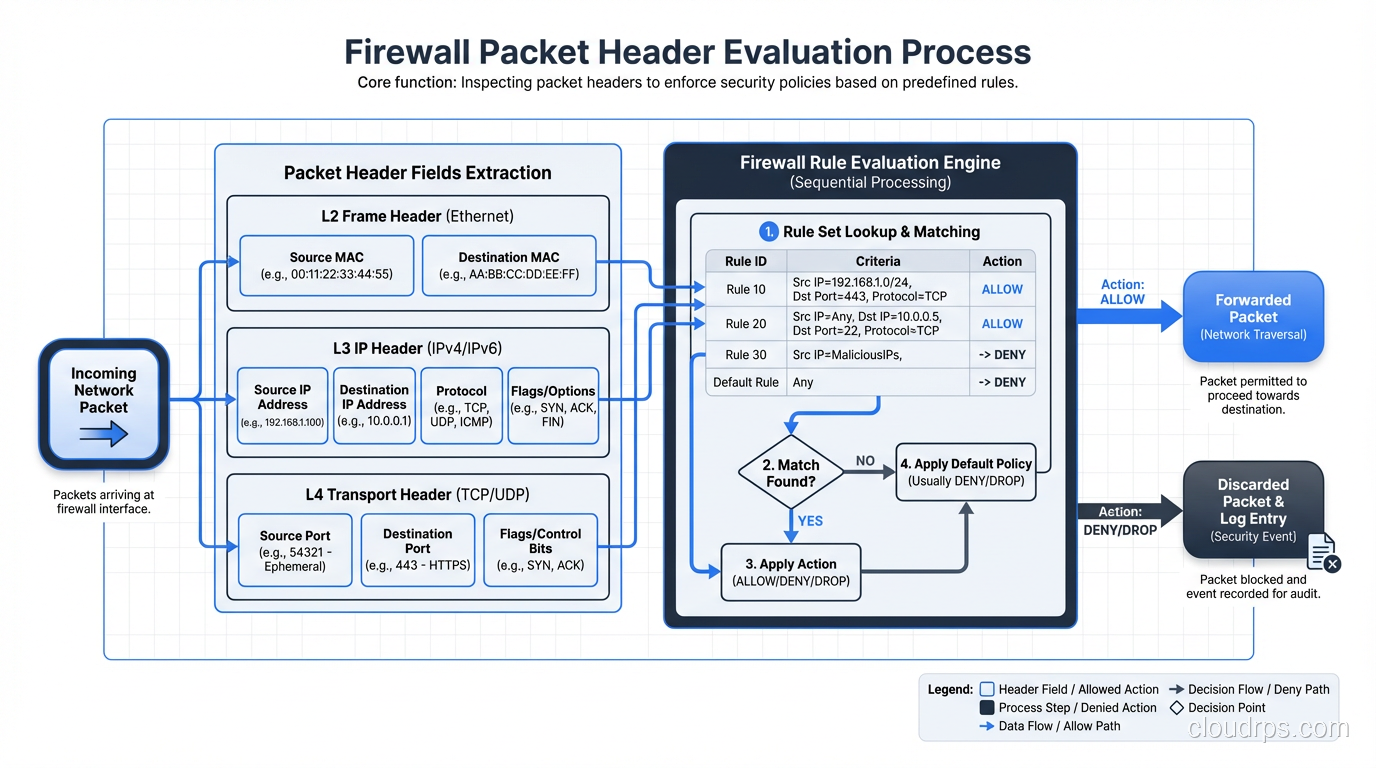
Before we get into stateless versus stateful, we need to be precise about what a firewall is doing. At its core, a firewall examines network traffic and makes a decision: allow, deny, or drop. That decision is based on rules you define. The critical difference between firewall types is what information they use to make that decision.
Every packet that crosses a network carries header information: source IP, destination IP, source port, destination port, protocol, and various flags. That is the raw material a firewall works with. The question is whether the firewall looks at each packet in isolation or whether it understands the broader conversation that packet belongs to.
How Stateless Firewalls Work
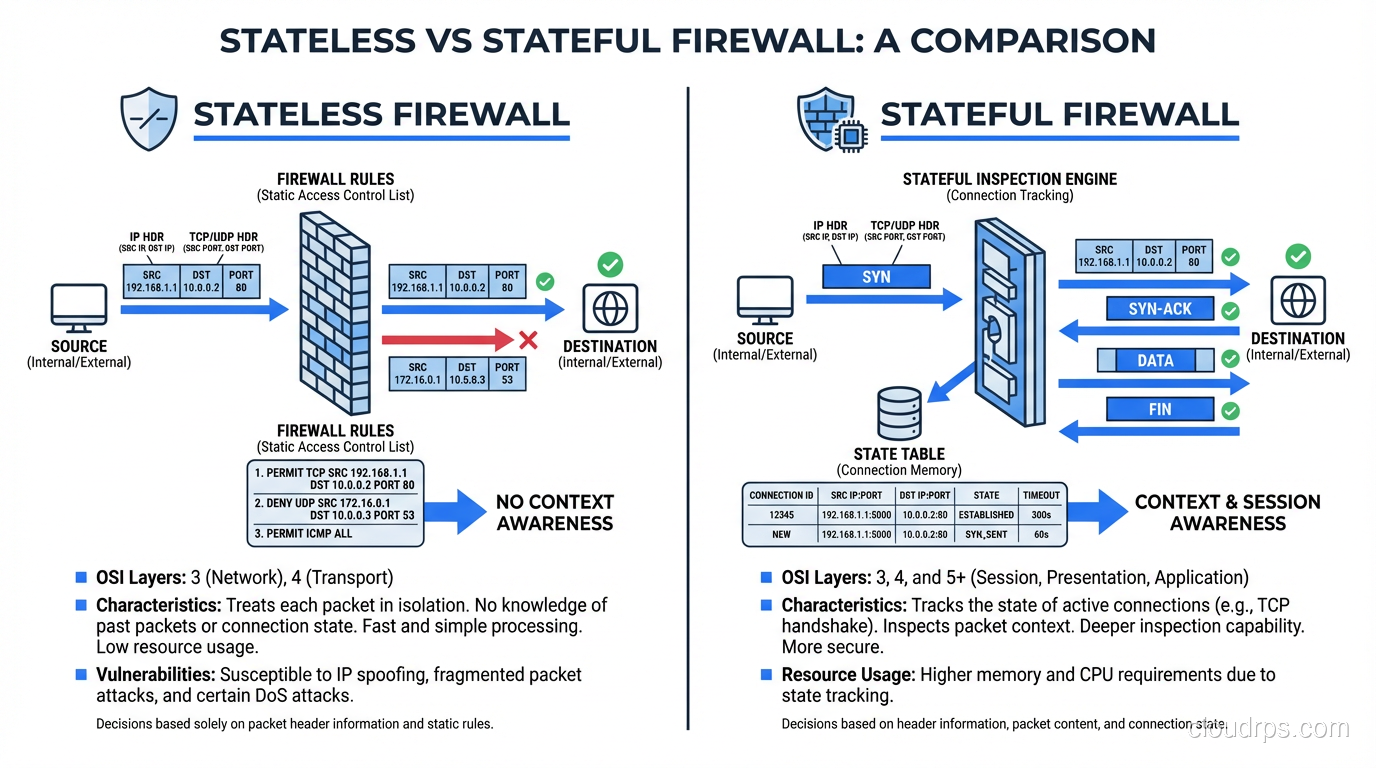
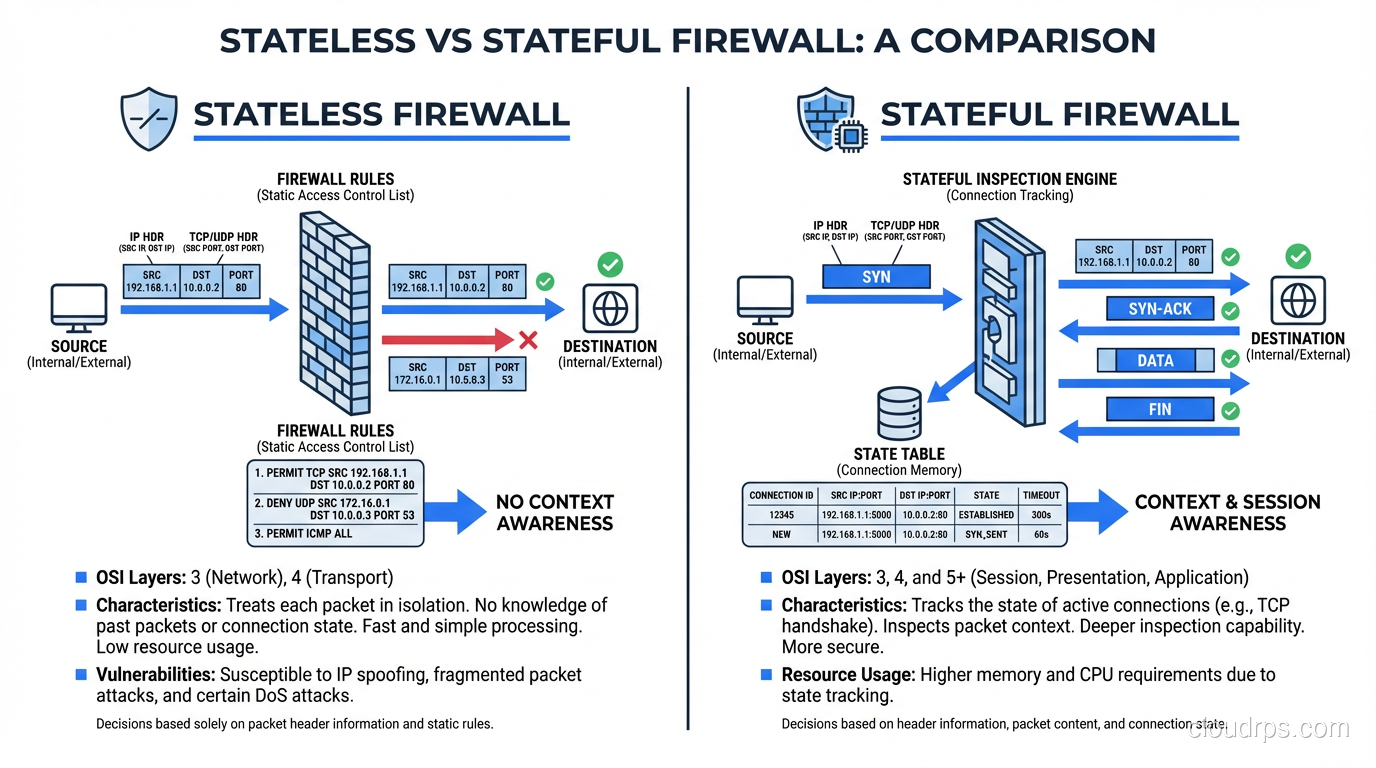
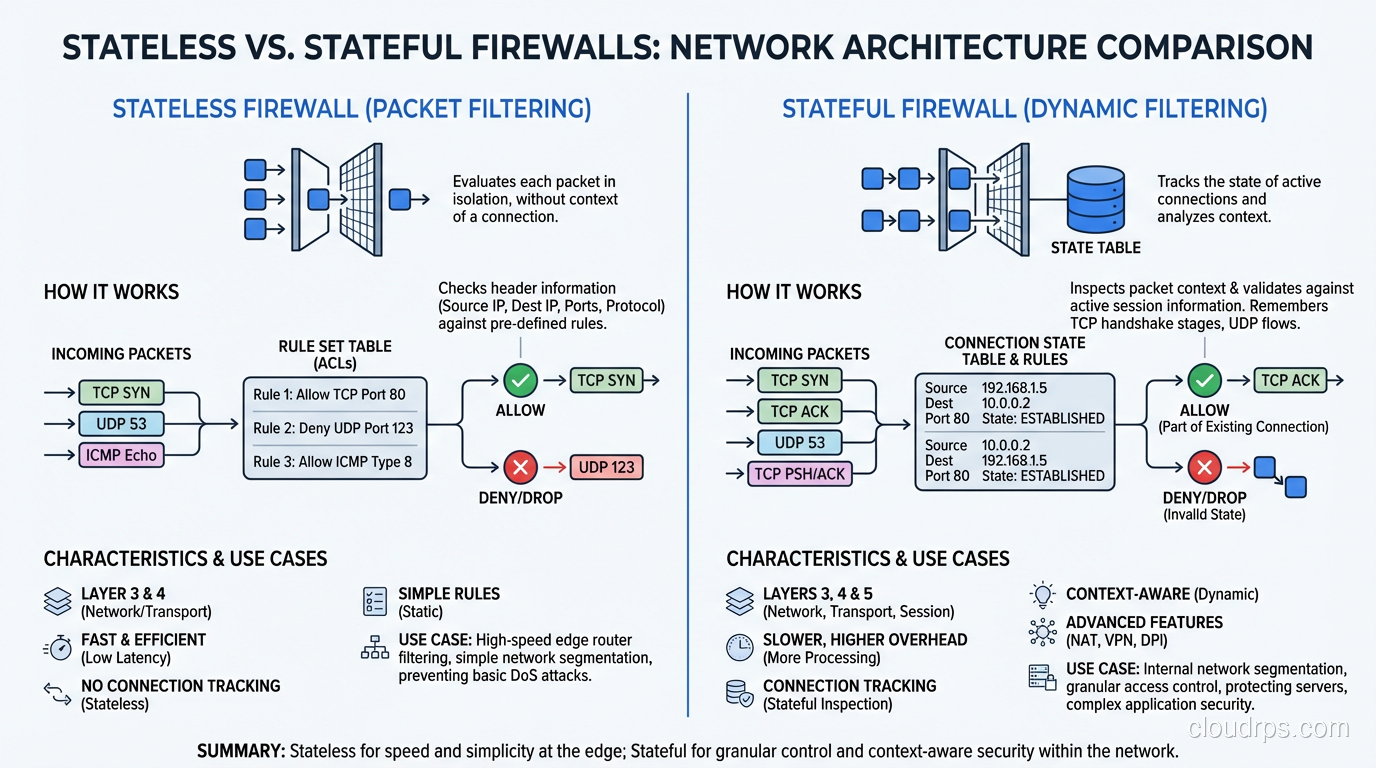
A stateless firewall (sometimes called a packet-filtering firewall) evaluates each packet independently. It has no memory of previous packets. Every single packet that arrives gets compared against a ruleset, and a decision is made based solely on the header information in that specific packet.
Think of it like a bouncer at a door who checks every person’s ID every single time, even if they just walked out thirty seconds ago. There is no recognition, no context, no memory.
The Rule Matching Process
A stateless firewall typically processes rules in order, top to bottom. For each incoming packet, it checks:
- Source IP address (or range)
- Destination IP address (or range)
- Protocol (TCP, UDP, ICMP, etc.)
- Source port
- Destination port
- TCP flags (SYN, ACK, FIN, etc.)
The first rule that matches determines the action. If no rule matches, a default action applies, usually deny.
Here is where things get tricky. Because a stateless firewall has no concept of a “connection,” you need explicit rules for both directions of traffic. If you want your web server to accept HTTP requests and send responses, you need a rule allowing inbound traffic to port 80 and a separate rule allowing outbound traffic from port 80. Miss that second rule and your server accepts connections but can never respond.
Where Stateless Firewalls Work Well
Stateless firewalls are fast. Blazingly fast. Because there is no connection table to maintain, no state to track, the processing overhead per packet is minimal. This makes them ideal for:
- High-throughput edge filtering:When you need to drop obviously bad traffic before it hits your more sophisticated (and more expensive) security layers.
- Simple allow/deny by IP range:Blocking entire netblocks or allowing traffic from known partner networks.
- DDoS mitigation front-lines:When you are dealing with volumetric attacks, you need something that can process millions of packets per second without choking.
AWS Network ACLs are a perfect example of stateless firewalls in the cloud. They evaluate each packet independently, which is why you always need both inbound and outbound rules. If you have worked with security groups and ACLs in AWS, you have seen this distinction firsthand.
How Stateful Firewalls Work
A stateful firewall tracks the state of active network connections. When the first packet of a new connection arrives (say, a TCP SYN), the firewall evaluates it against the ruleset. If the connection is allowed, the firewall creates an entry in its connection table (also called a state table). Every subsequent packet that belongs to that connection is matched against the state table rather than being re-evaluated against the full ruleset.
This is a fundamentally different approach. The firewall understands that a TCP handshake is a multi-packet process. It knows that after a SYN comes a SYN-ACK, then an ACK, and then data flows. It tracks sequence numbers, window sizes, and connection states. It knows when a connection has been properly closed via FIN/FIN-ACK or reset via RST.
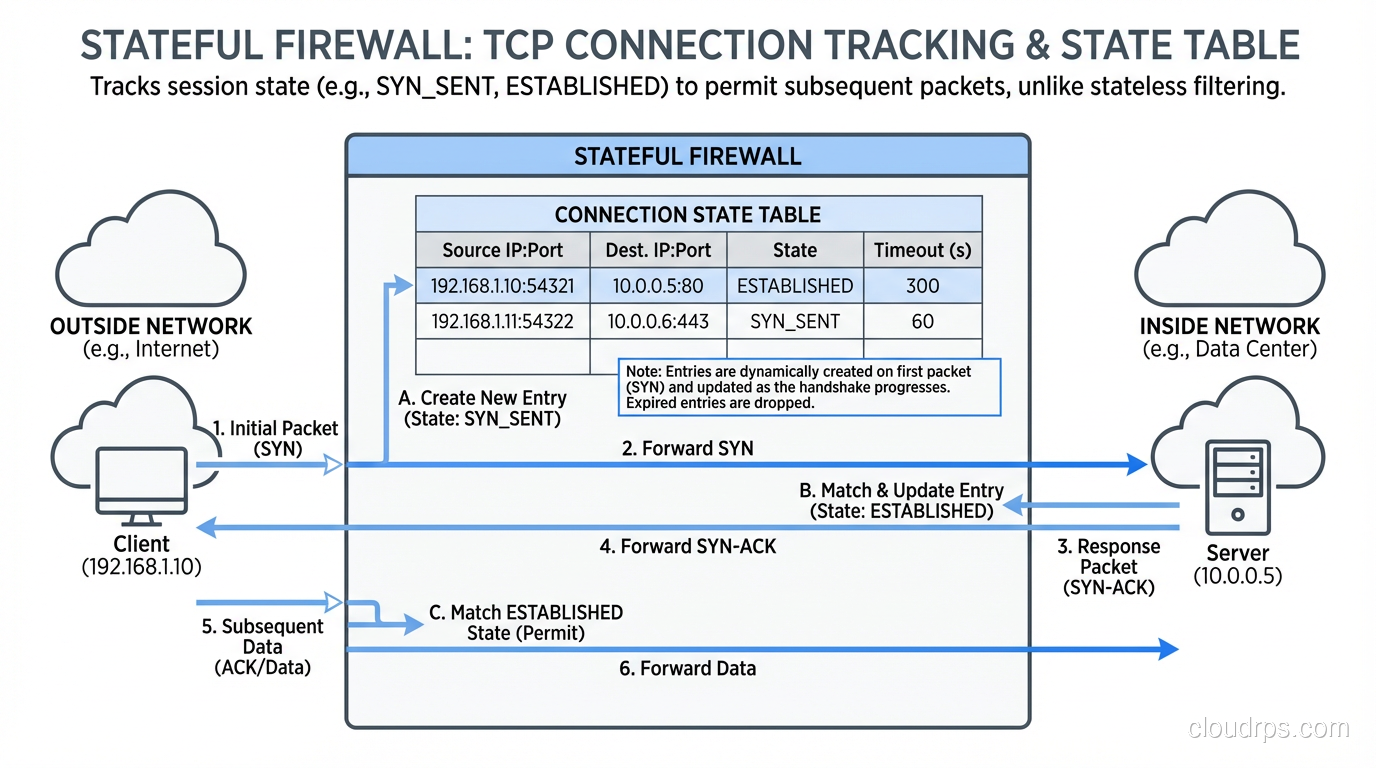
The Connection Table
The state table is the heart of a stateful firewall. Each entry typically contains:
- Source and destination IP addresses
- Source and destination ports
- Protocol
- Connection state (NEW, ESTABLISHED, RELATED, INVALID)
- Timeout values
- Sequence number tracking (for TCP)
When a packet arrives, the firewall first checks the state table. If the packet matches an existing tracked connection, it is allowed through without hitting the full ruleset. This is both a performance optimization and a security feature, since return traffic is automatically allowed without you having to write explicit rules for it.
Why Stateful Inspection Is More Secure
I have investigated breaches where attackers exploited the limitations of stateless filtering. One common technique: crafting packets with the ACK flag set to bypass stateless rules that only blocked SYN packets. The attacker could send ACK packets to probe internal hosts and map the network, because the stateless firewall saw the ACK flag and assumed it was part of an existing connection.
A stateful firewall stops this cold. It sees an ACK packet that does not match any tracked connection and drops it. There is no connection in the state table, so the packet is invalid. Period.
Stateful inspection also handles protocol-level attacks better. It can detect things like:
- Out-of-sequence packets that do not match the tracked TCP state
- Invalid flag combinations (like SYN+FIN) that are often used in scanning
- Connection hijacking attempts where sequence numbers do not match
This ties directly into the broader conversation about Layer 4 vs Layer 7 security. Stateful firewalls operate primarily at Layer 4, understanding transport-layer connections but not necessarily the application-layer content.
Stateless vs Stateful: A Direct Comparison
Let me lay out the key differences clearly, because this is where I see the most confusion.
Rule Complexity
With stateless firewalls, your rulesets are roughly double the size. Every permitted flow needs rules in both directions. With stateful firewalls, you write a rule for the initiating direction, and return traffic is handled automatically.
I once audited a network where the team had over 400 stateless ACL rules. When we migrated to stateful policies, we got it down to about 90 rules that were actually clearer and more secure. Fewer rules means fewer mistakes, and in security, mistakes kill you.
Performance Characteristics
Stateless firewalls have consistent, predictable per-packet processing time. There is no table lookup beyond the ruleset, no state to maintain.
Stateful firewalls have higher throughput for established connections (state table lookup is faster than full rule evaluation), but they carry the overhead of maintaining the state table. Under extreme load (think millions of concurrent connections) the state table itself can become a bottleneck or even a target. State table exhaustion is a real attack vector.
Security Posture
Stateful wins here, hands down. The ability to track connections and validate that packets belong to legitimate, tracked sessions eliminates entire classes of attacks. But “more secure” does not always mean “better for every situation.”
When to Use Each Type in Production
This is the practical guidance that actually matters. In my experience designing network architectures for organizations ranging from startups to Fortune 500 companies, here is how I think about placement.
Stateless: The Outer Perimeter
Stateless filtering belongs at the outermost edge of your network where you need to handle massive traffic volumes and your filtering requirements are simple. Think:
- Blocking traffic from known-bad IP ranges or geographies
- Rate limiting at the network edge
- Filtering out protocols you never want to see (why is someone sending GRE packets to your web tier?)
- Cloud provider network ACLs as a coarse first layer
In AWS, this maps perfectly to NACLs at the subnet level. They are your coarse outer filter. You are not doing fine-grained application security here; you are keeping the obvious garbage out.
Stateful: Everything Else
For anything that requires understanding traffic flows, protecting applications, or enforcing security policies between trust zones, you want stateful inspection. This includes:
- Security groups in cloud environments (AWS security groups are stateful by design)
- Host-based firewalls (iptables/nftables with connection tracking, Windows Firewall)
- Next-generation firewalls at network boundaries between trust zones
- Microsegmentation in zero-trust architectures
If you are building a web application firewall strategy, you are already well past stateless filtering. You need stateful inspection as a baseline, and often Layer 7 inspection on top of that.
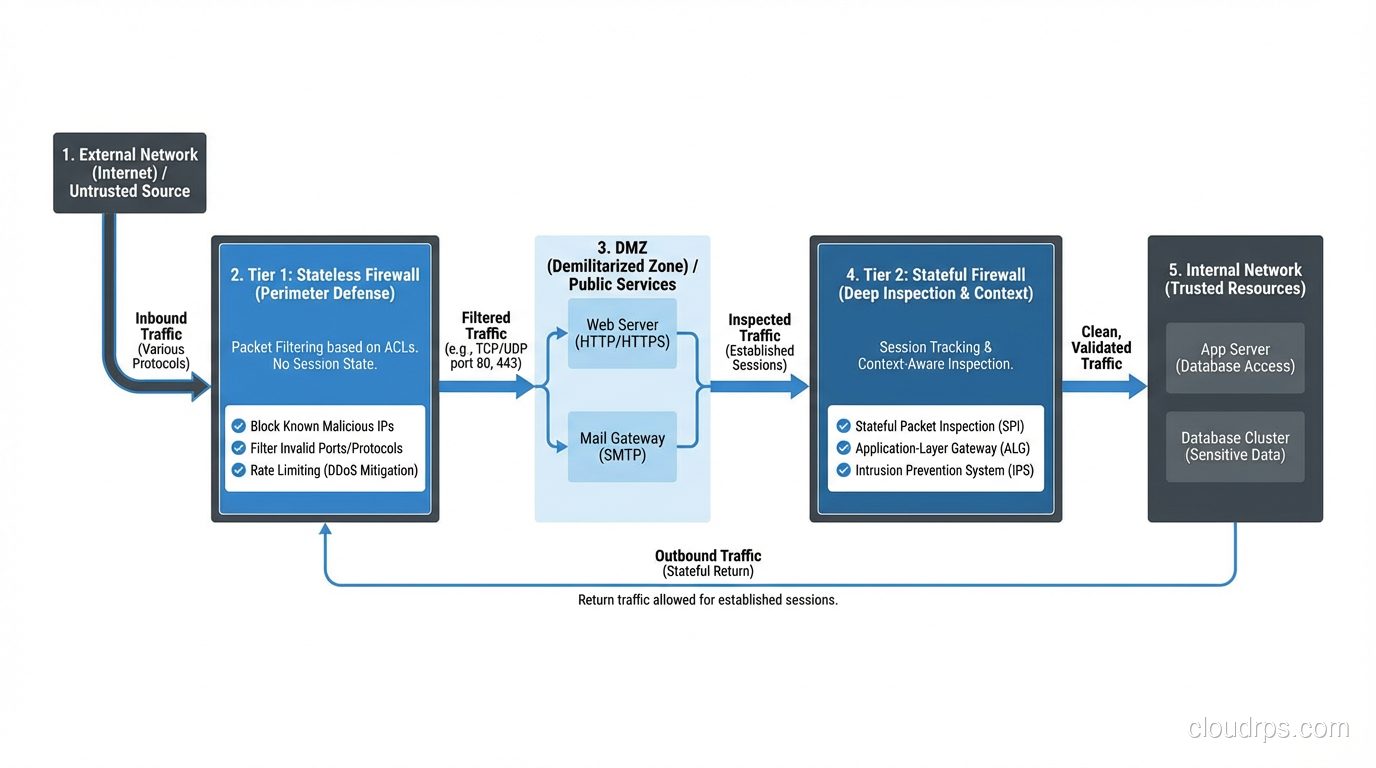
The Layered Approach
In practice, you almost always use both. Here is a typical architecture I have deployed many times:
- Edge router / cloud NACL:Stateless filtering to drop obviously unwanted traffic
- Stateful perimeter firewall:Connection tracking, zone-based policies
- Internal segmentation firewalls:Stateful inspection between application tiers
- Host-based firewalls:Stateful rules on each server
- Application-layer controls:WAFs, API gateways, and application-level security
Each layer handles what it is best at. The stateless layer deals with volume. The stateful layers deal with connection integrity. The application layers deal with content.
Common Mistakes I Have Seen
Over thirty years, I have seen these same mistakes repeated across organizations of every size.
Mistake 1: Using Only Stateless Filtering
I once consulted for a company that was “saving money” by relying entirely on router ACLs for their security. They had no stateful inspection anywhere. An attacker walked right through their perimeter using crafted ACK packets and pivoted across their flat internal network. The breach took weeks to detect because their stateless rules were not catching the lateral movement.
Mistake 2: Ignoring State Table Limits
On the opposite end, I have seen stateful firewalls collapse under load because nobody planned for the number of concurrent connections. A SYN flood attack filled the state table, and legitimate users could not establish new connections. If you are running stateful inspection, you need to know your state table limits and have protections like SYN cookies or SYN proxying in place.
Mistake 3: Not Understanding Cloud Provider Defaults
In cloud environments, the stateless/stateful distinction is baked into specific services. AWS NACLs are stateless. AWS Security Groups are stateful. Mixing these up, or not understanding that NACLs need rules in both directions, is one of the most common cloud security misconfigurations I encounter.
State Table Internals: What Actually Happens
For the technically curious, let me walk through what happens when a TCP connection passes through a stateful firewall.
SYN arrives:The firewall checks the ruleset. If allowed, it creates a state table entry marked as NEW and records the source/destination IPs, ports, and the initial sequence number.
SYN-ACK returns:The firewall matches this against the state table entry, verifies it is a valid response to the tracked SYN, and updates the state to SYN_RECV. It records the server’s sequence number.
ACK completes handshake:The firewall verifies the sequence number, updates state to ESTABLISHED, and starts the idle timeout counter.
Data flows:Each packet is matched to the state table. Sequence numbers are validated to be within the expected window. Invalid packets are dropped.
Connection closes:FIN packets trigger state transitions. After both sides have sent FIN and the final ACK is received, the state moves to TIME_WAIT before eventual removal.
For UDP, which is connectionless, stateful firewalls create pseudo-connections based on the source/destination IP and port tuple. They track these with shorter timeouts since there is no explicit connection setup or teardown.
For ICMP, the firewall tracks request/reply pairs. An echo request creates state, and the corresponding echo reply is matched against it.
Performance Considerations in Modern Environments
Modern stateful firewalls have come a long way from the early days when state table lookups could be a real bottleneck. Hardware-accelerated session tracking, FPGA-based packet processing, and kernel-bypass technologies like DPDK mean that modern firewalls can track millions of connections with minimal latency.
That said, in cloud environments you are often dealing with software-defined firewalls where the performance characteristics are different. Cloud provider firewalls (security groups, NACLs) are implemented in the hypervisor or at the VPC level, and their performance is tightly coupled to the instance type and network bandwidth you have provisioned.
If you are designing for scale, understand that every stateful connection consumes memory. A typical state table entry is 200-300 bytes. At a million concurrent connections, that is 200-300 MB of state. Not a problem for modern hardware, but something to plan for in capacity planning.
Wrapping Up
Stateless firewalls are simple, fast, and predictable. They belong at the edges of your network where you need raw throughput and your filtering requirements are straightforward.
Stateful firewalls are smarter, more secure, and essential for any environment where you need to understand and control traffic flows. They belong everywhere you are enforcing security policy between trust zones.
The right answer is almost never one or the other. It is both, layered intelligently, each handling what it does best. Build your security architecture like you would build a physical building: the outer walls keep out the weather, but the interior doors and locks are what actually control access.
If you have gotten this far and you are still thinking about how this applies to your cloud architecture, go read about security groups vs ACLs next. That is where these concepts get very concrete, very fast.
Get Cloud Architecture Insights
Practical deep dives on infrastructure, security, and scaling. No spam, no fluff.
By subscribing, you agree to receive emails. Unsubscribe anytime.