Early in my career, I made the mistake of thinking encryption was a single tool. You “encrypt stuff” and it is secure. That naive view lasted about three months, until I had to figure out how to securely distribute encryption keys to forty branch offices across six countries without any of them being intercepted. That is when I truly understood why we have two fundamentally different approaches to encryption and why you almost always need both.
Symmetric and asymmetric encryption are not competing technologies. They are complementary tools that solve different problems, and every modern security protocol (TLS, SSH, VPNs, encrypted email) uses them together. Let me explain exactly how each one works, where each one excels, and how they combine in the systems you rely on every day.
Symmetric Encryption: One Key to Rule Them All
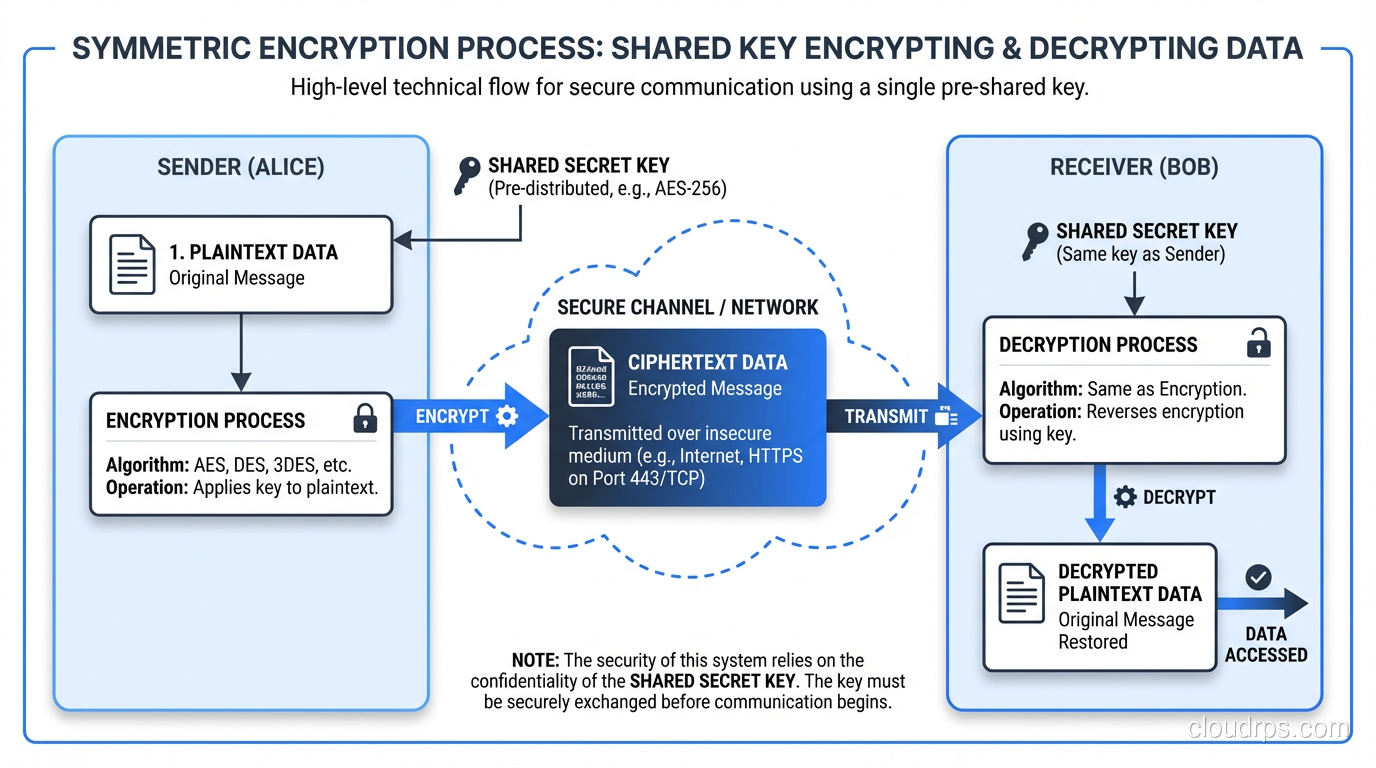
Symmetric encryption is the older and simpler of the two approaches. The same key is used to encrypt and decrypt. If I encrypt a file with the key K, you need that exact same key K to decrypt it. Simple concept, profound implications.
How It Works Under the Hood
Modern symmetric encryption algorithms work as either block ciphers or stream ciphers.
Block ciphers (like AES) divide the plaintext into fixed-size blocks (typically 128 bits) and encrypt each block. Because most data is longer than one block, you need a mode of operation that defines how blocks relate to each other. This is where things like CBC (Cipher Block Chaining), GCM (Galois/Counter Mode), and CTR (Counter) mode come in.
Stream ciphers (like ChaCha20) generate a pseudorandom keystream from the key and XOR it with the plaintext one byte at a time. They are conceptually simpler and often faster in software implementations.
The dominant symmetric algorithm today is AES (Advanced Encryption Standard) with either 128-bit or 256-bit keys. AES-256 is what governments and financial institutions use. It has survived over two decades of cryptanalysis with no practical attacks against the full algorithm. When I am designing a system and someone asks “what encryption should we use,” the answer for symmetric encryption is almost always AES-256-GCM.
The Key Distribution Problem
Here is the fundamental limitation of symmetric encryption: how do you get the key to the other party securely?
If I want to send you an encrypted message, we both need the same key. But if I send you the key over the network, anyone intercepting that transmission now has the key. I could call you on the phone and read it out, but that does not scale to millions of HTTPS connections per second.
This is called the key distribution problem, and it is the reason asymmetric encryption was invented. But before we get there, let me be clear: symmetric encryption’s strengths are enormous.
Why Symmetric Encryption Dominates for Bulk Data
Symmetric encryption is fast. On modern hardware with AES-NI instructions (hardware acceleration built into Intel and AMD processors since roughly 2010), AES can encrypt data at speeds exceeding 10 Gbps on a single core. That is fast enough to encrypt every packet on a busy network link without breaking a sweat.
It is also efficient in terms of ciphertext size. The encrypted output is essentially the same size as the input (plus a small IV and authentication tag for authenticated modes). There is no significant expansion.
These properties make symmetric encryption the right choice for:
- Encrypting data at rest (disk encryption, database encryption, file encryption)
- Encrypting data in transit (the bulk data encryption in TLS, SSH, VPN tunnels)
- Encrypting backups, archives, and large datasets
When we talk about encryption at rest and in transit, the actual encryption happening is almost always symmetric.
Asymmetric Encryption: The Two-Key Revolution
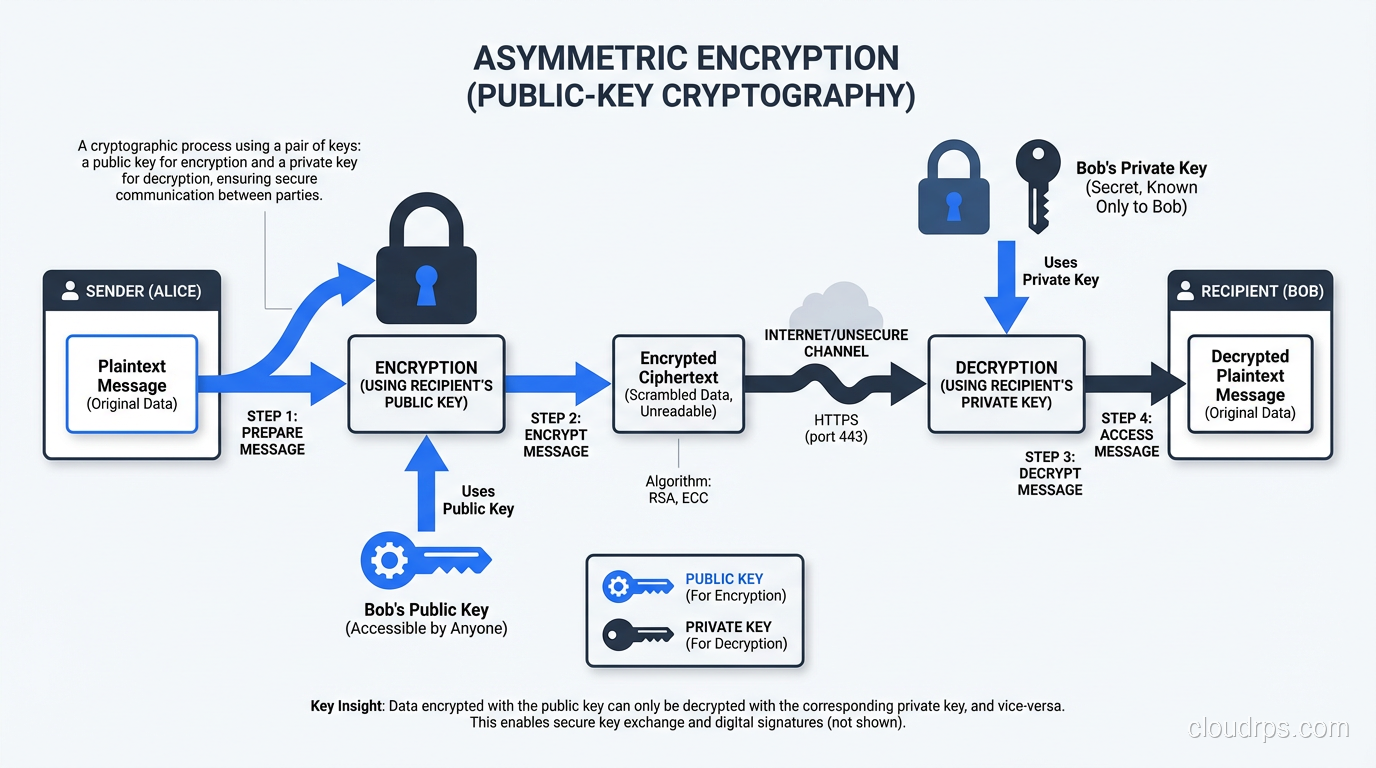
Asymmetric encryption (also called public-key cryptography) uses a mathematically linked pair of keys: a public key and a private key. Data encrypted with the public key can only be decrypted with the private key, and vice versa.
This was a genuine revolution when Diffie, Hellman, Merkle, Rivest, Shamir, and Adleman developed the concept and first practical implementations in the 1970s. It solved the key distribution problem in one elegant stroke: you publish your public key to the world, and anyone can use it to encrypt a message that only you can decrypt.
The Math Behind It
Without getting into a number theory textbook, asymmetric encryption relies on mathematical problems that are easy to compute in one direction but computationally infeasible to reverse.
RSA relies on the difficulty of factoring the product of two very large prime numbers. Multiplying two 1024-bit primes together is trivial. Factoring the result back into those primes would take longer than the age of the universe with current technology.
Elliptic Curve Cryptography (ECC) relies on the difficulty of the elliptic curve discrete logarithm problem. ECC achieves equivalent security to RSA with much smaller key sizes. A 256-bit ECC key provides roughly the same security as a 3072-bit RSA key.
Diffie-Hellman key exchange (including its elliptic curve variant, ECDHE) is not encryption per se, but it is the most widely used asymmetric algorithm on the internet. It allows two parties to establish a shared secret over an insecure channel. This shared secret then becomes the key for symmetric encryption.
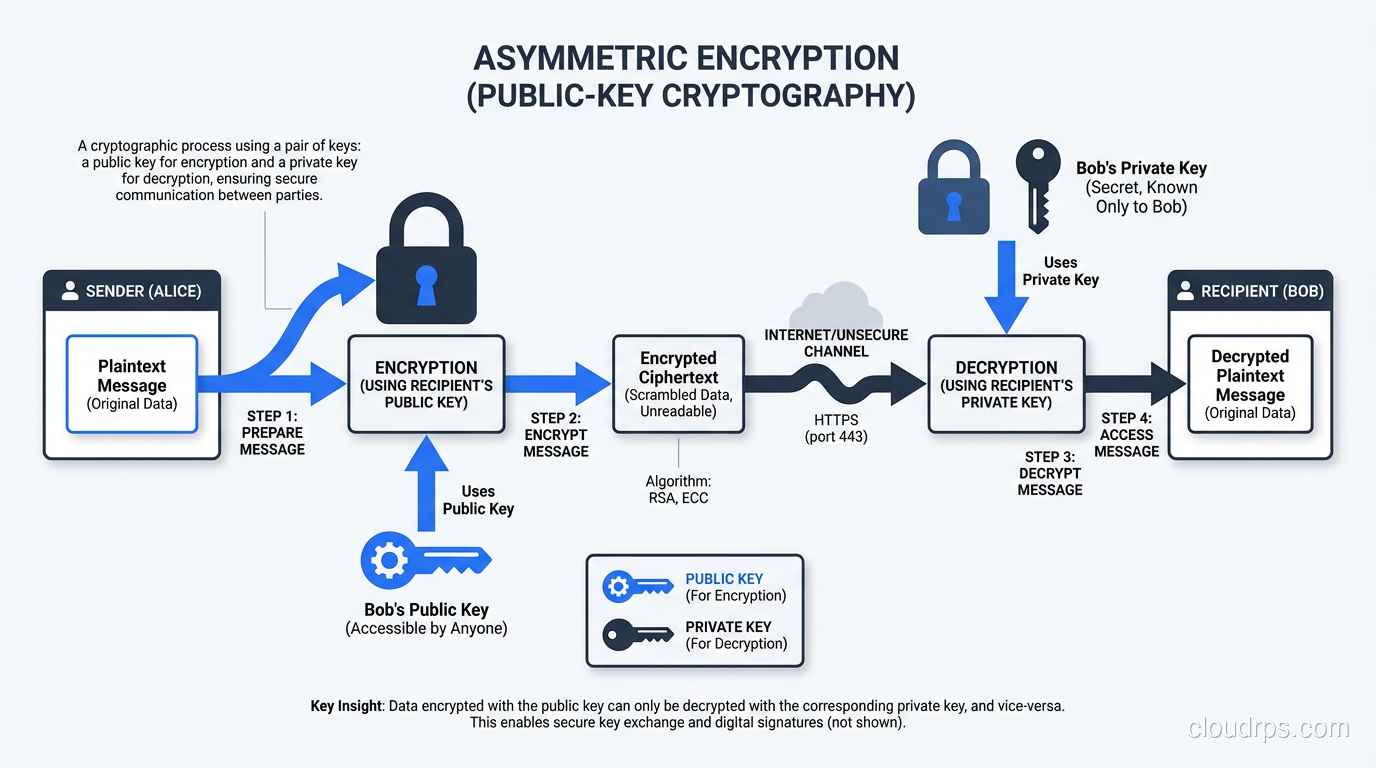
Why Asymmetric Encryption Is Slow
Asymmetric operations are orders of magnitude slower than symmetric ones. RSA-2048 encryption might process a few thousand operations per second on the same hardware that does billions of AES operations. ECC is faster than RSA but still nowhere near symmetric speeds.
This is not a design flaw; it is an inherent consequence of the mathematical operations involved. You are doing modular exponentiation with thousands-of-bit numbers (RSA) or point multiplication on elliptic curves (ECC). These are computationally expensive operations.
This is why nobody encrypts bulk data with RSA. You would bring your infrastructure to its knees.
What Asymmetric Encryption Does Well
Despite its speed limitations, asymmetric cryptography is essential for:
- Key exchange:Establishing shared secrets over insecure channels (ECDHE in TLS)
- Digital signatures:Proving authenticity and integrity (code signing, certificate validation)
- Authentication:Proving identity without sharing secrets (SSH key authentication)
- Non-repudiation:Providing proof that a specific party signed something
When you connect to a server using SSH, asymmetric cryptography handles the key exchange and authentication. When your browser establishes an HTTPS connection, asymmetric cryptography is what makes the initial handshake secure.
The Hybrid Approach: How Real Systems Work
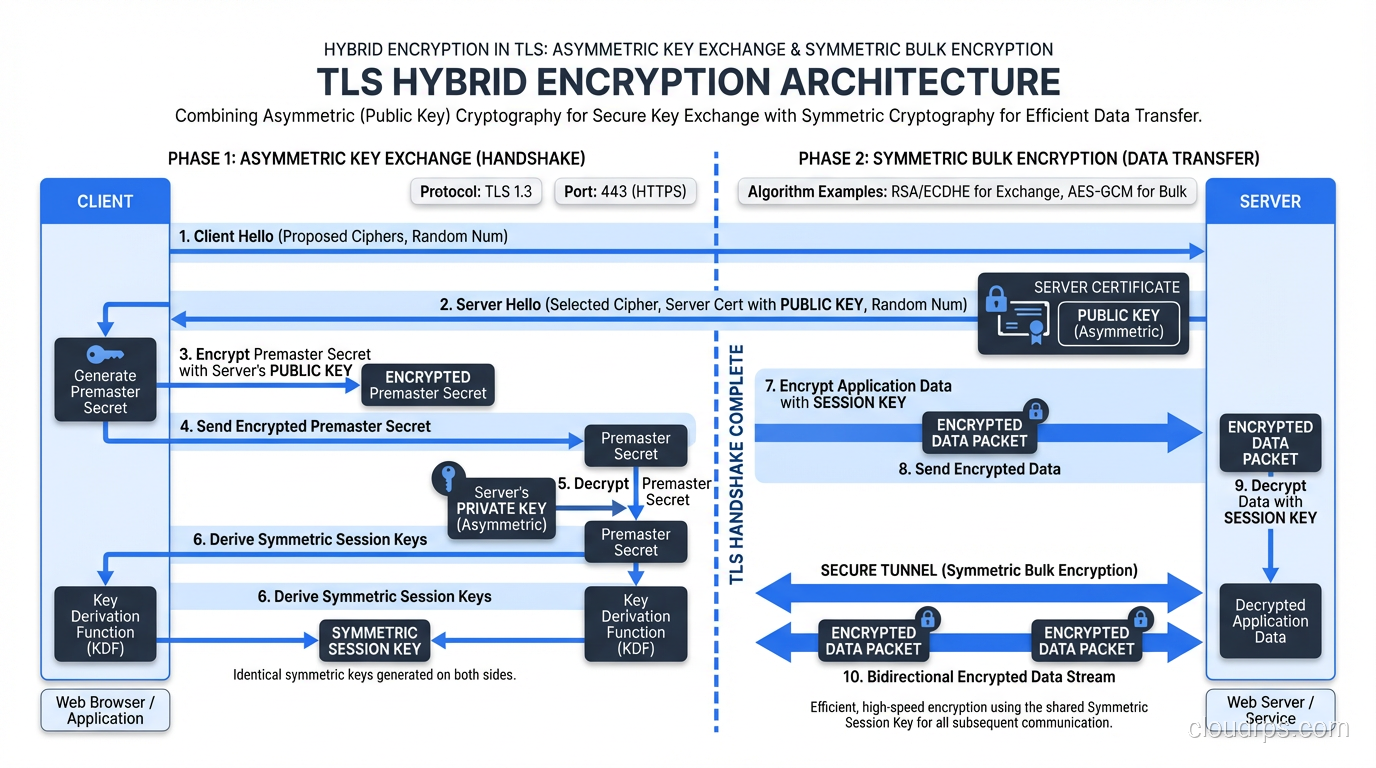
Here is the key insight that ties everything together: virtually every modern security protocol uses both symmetric and asymmetric encryption together. This is called hybrid encryption, and it is the backbone of internet security.
The pattern is always the same:
- Asymmetric encryption establishes a secure channel:Through key exchange or public-key encryption, both parties agree on a shared secret.
- The shared secret becomes a symmetric key:This key is used for the actual data encryption.
- Symmetric encryption handles the bulk data:Fast, efficient, and now secured by the key that was safely exchanged.
TLS: The Perfect Example
When your browser connects to a website over HTTPS, here is what happens:
- The server presents its certificate (containing its public key)
- Client and server perform an ECDHE key exchange, using asymmetric cryptography to establish a shared secret
- Both sides derive symmetric session keys from that shared secret
- All subsequent data is encrypted with AES (or ChaCha20) using those symmetric keys
The asymmetric part takes a few milliseconds and handles maybe a few hundred bytes of key exchange data. The symmetric part handles gigabytes of actual content at wire speed. Each algorithm does what it is best at.
Algorithm Comparison: What to Use When
Let me give you the practical guidance I give to my teams.
Symmetric Algorithms
AES-256-GCM:The default choice. GCM mode provides both encryption and authentication (AEAD, or Authenticated Encryption with Associated Data). Use this unless you have a specific reason not to.
ChaCha20-Poly1305:The alternative when AES hardware acceleration is not available (embedded devices, older mobile processors). Google pushed this hard for Android devices, and it is now widely supported in TLS 1.3.
AES-256-CBC:Still common but being phased out in favor of GCM. CBC does not provide authentication, so you need to add HMAC separately (encrypt-then-MAC). More moving parts means more ways to get it wrong.
Avoid: DES, 3DES, RC4, Blowfish. These are all either broken or deprecated. If you see them in a production system, that is a finding in your security audit.
Asymmetric Algorithms
ECDHE (Elliptic Curve Diffie-Hellman Ephemeral):The standard for key exchange in TLS 1.3. The “ephemeral” part means new keys are generated for each session, providing forward secrecy.
Ed25519:The current best practice for digital signatures and SSH keys. Fast, secure, and resistant to implementation errors that have plagued other curves.
RSA-2048 or RSA-4096:Still widely used for certificate signing and legacy compatibility, but being gradually replaced by ECC in new deployments. If you are generating new RSA keys today, use 4096-bit minimum.
ECDSA (P-256 or P-384):Used in TLS certificates. Functional but Ed25519 is preferred when you have the choice.
Key Size Equivalence
This is a table I keep in my head and reference constantly:
- AES-128 ≈ RSA-3072 ≈ ECC-256 (128-bit security level)
- AES-256 ≈ RSA-15360 ≈ ECC-512 (256-bit security level)
Notice that RSA key sizes balloon enormously to match higher security levels. This is why ECC is winning: you get equivalent security with keys that are a fraction of the size, which translates directly to faster operations and lower bandwidth consumption.
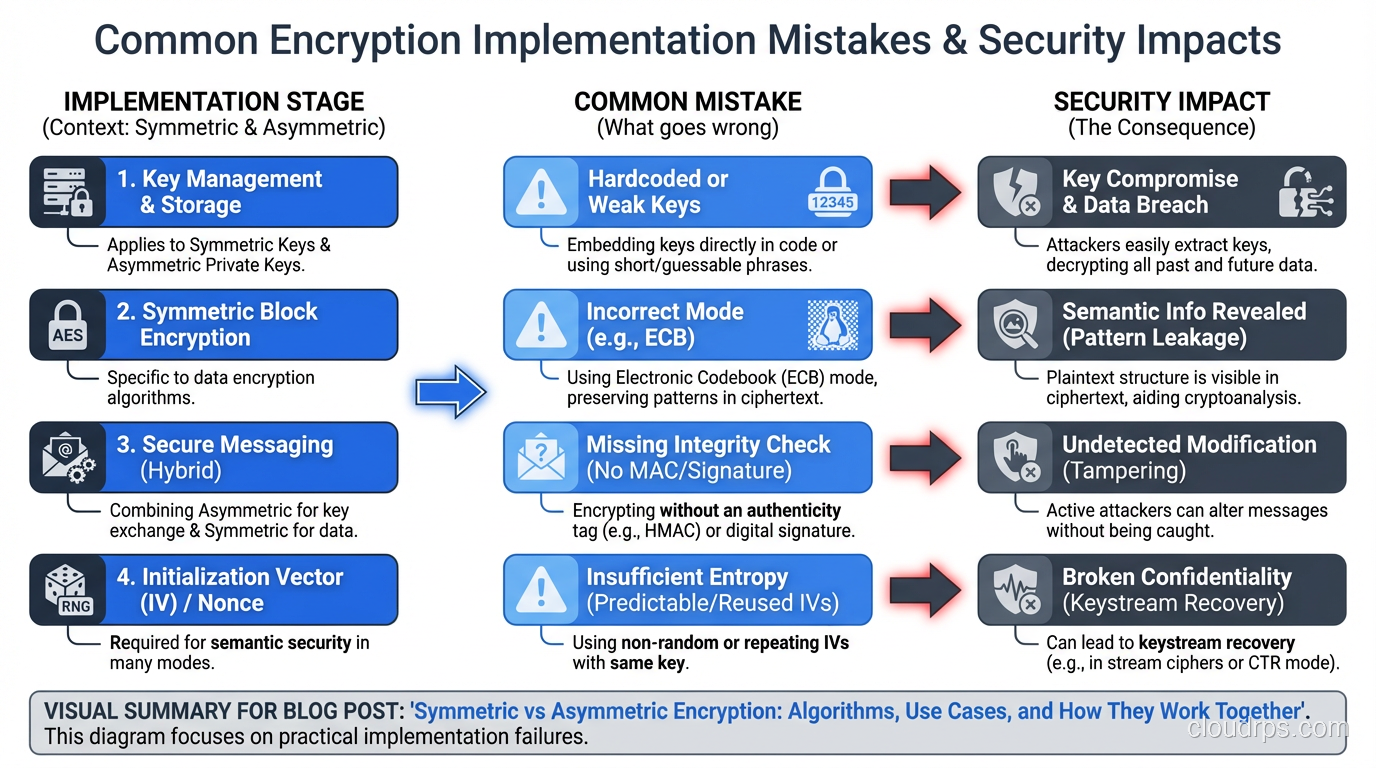
Real-World Implementation Pitfalls
I have reviewed hundreds of encryption implementations over my career, and the same mistakes come up repeatedly.
Pitfall 1: Rolling Your Own Crypto
I cannot stress this enough. Do not implement cryptographic algorithms yourself. Use established libraries: OpenSSL, libsodium, the Go standard library crypto packages, or your platform’s native crypto APIs. Every hand-rolled AES implementation I have audited had at least one critical vulnerability, usually related to IV reuse or padding oracle attacks.
Pitfall 2: Static Keys
If you are using the same symmetric key for months or years without rotation, you are accumulating risk. Key rotation is not optional. It limits the blast radius of a key compromise and reduces the amount of data exposed by any single key.
Pitfall 3: Ignoring Forward Secrecy
If your key exchange uses static RSA (the server’s private key directly decrypts the pre-master secret), then compromising the server’s private key retroactively compromises every past session. ECDHE provides forward secrecy, where each session uses ephemeral keys, so compromising the long-term key does not help an attacker who recorded past traffic.
This is why TLS 1.3 mandates forward secrecy and removed static RSA key exchange entirely.
Pitfall 4: Confusing Encryption with Authentication
Encryption ensures confidentiality (nobody can read the data). It does not ensure integrity or authenticity. Without additional measures, an attacker might modify the ciphertext in ways that produce meaningful changes in the plaintext. Always use authenticated encryption (AES-GCM, ChaCha20-Poly1305) or add explicit authentication (HMAC).
Post-Quantum Considerations
I would be negligent not to mention the elephant in the room. Quantum computers, once they reach sufficient scale, will break RSA and ECC. Shor’s algorithm factors large numbers and solves discrete logarithm problems in polynomial time, which is exactly what protects our current asymmetric algorithms.
Symmetric encryption is less affected. Grover’s algorithm effectively halves the security level (AES-256 becomes AES-128 equivalent), which is still considered secure.
NIST finalized its first set of post-quantum cryptographic standards in 2024, including ML-KEM (formerly CRYSTALS-Kyber) for key exchange. If you are designing systems with a 10+ year data sensitivity horizon, you should be evaluating hybrid approaches that combine classical and post-quantum algorithms. This is not theoretical. Google has already deployed post-quantum key exchange in Chrome.
Making the Right Architectural Decisions
When I am designing a security architecture, here is my decision framework:
For data at rest: Symmetric encryption (AES-256-GCM). Key management is the hard part; use your cloud provider’s KMS or a dedicated HSM. Do not store encryption keys alongside encrypted data.
For data in transit: Use TLS 1.3, which handles the hybrid approach for you. Do not try to build your own transport encryption protocol.
For authentication: Asymmetric. SSH keys (Ed25519), client certificates, digital signatures.
For key exchange: ECDHE with forward secrecy. Always.
For signing: Ed25519 for new systems, RSA-4096 or ECDSA P-256 for compatibility with existing infrastructure.
The beauty of modern cryptographic protocols is that they handle the complexity of combining these algorithms for you. TLS 1.3, SSH, and WireGuard all implement hybrid encryption correctly. Your job is to configure them properly and manage keys well, not to reinvent the wheel.
Wrapping Up
Symmetric encryption is fast and efficient but requires a pre-shared key. Asymmetric encryption solves the key distribution problem but is too slow for bulk data. Together, they form the foundation of every secure communication system on the internet.
Understanding this distinction is not academic trivia. It directly affects how you design systems, choose algorithms, configure protocols, and evaluate security claims. The next time a vendor tells you their product uses “military-grade encryption,” you will know the right follow-up questions: what algorithms, what key sizes, how are keys exchanged, and is forward secrecy supported.
If you want to see these concepts in action, read about how TLS actually works or dive into the SSH protocol. Both are masterclasses in combining symmetric and asymmetric cryptography to build something genuinely secure.
Get Cloud Architecture Insights
Practical deep dives on infrastructure, security, and scaling. No spam, no fluff.
By subscribing, you agree to receive emails. Unsubscribe anytime.