I spent the first fifteen years of my career building perimeter-based security. Firewalls, DMZs, VPNs, hardened border routers. The castle-and-moat approach that defined enterprise security for decades. I was good at it. And then I watched it fail catastrophically.
It was 2014. A client I had helped architect a “best-in-class” perimeter defense for suffered a breach. The attacker got in through a phishing email, nothing exotic, just a well-crafted message that convinced someone in accounting to click a link. Once inside the perimeter, the attacker moved laterally across the flat internal network like they owned the place. Because from the network’s perspective, they did. Everything inside the castle walls was trusted.
That was my come-to-Jesus moment with Zero Trust. Not the marketing buzzword it has become, but the fundamental architectural shift in how we think about security. Let me walk you through what Zero Trust actually means, how to implement it, and where most organizations get it wrong.
What Zero Trust Actually Means
Zero Trust is not a product you buy. It is not a single technology. It is an architectural philosophy built on one foundational premise: never trust, always verify.
In the traditional perimeter model, anything inside the network boundary is implicitly trusted. If you are on the corporate network, whether physically in the office or connected via VPN, you are considered a trusted entity with broad access to internal resources.
Zero Trust eliminates that implicit trust entirely. Every access request is authenticated, authorized, and encrypted regardless of where it originates. A request from a workstation sitting in the CEO’s office gets the same scrutiny as a request from a coffee shop in another country. Location is not identity. Network position is not authorization.
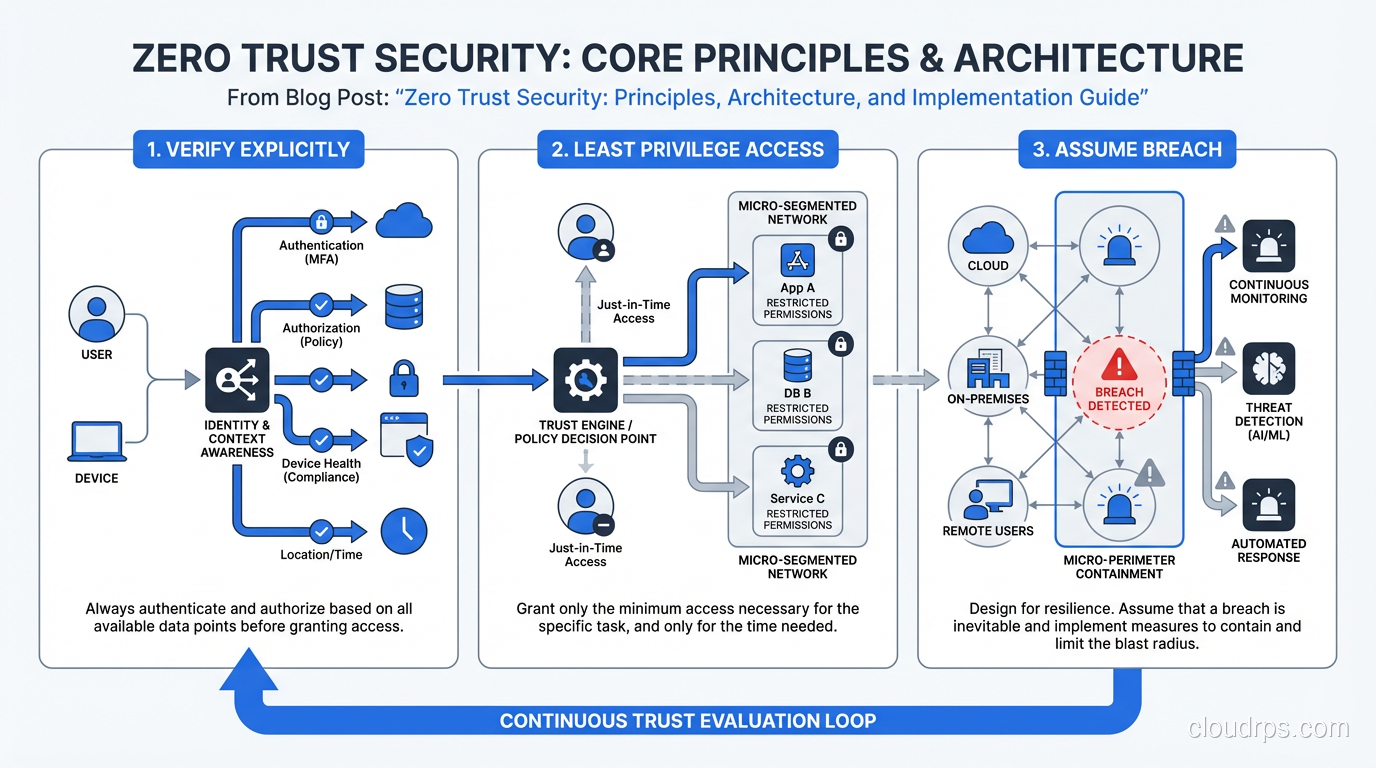
The core principles, as articulated by NIST SP 800-207 and refined by years of real-world implementation, are:
- Verify explicitly: Always authenticate and authorize based on all available data points: identity, device health, location, service requesting, data classification, and anomalies.
- Use least-privilege access: Limit access to the minimum necessary for the task at hand, with just-in-time and just-enough-access policies.
- Assume breach: Minimize blast radius, segment access, verify end-to-end encryption, and use analytics to detect threats and improve defenses. For the most sensitive workloads, confidential computing with trusted execution environments takes this principle further by protecting data even from compromised operating systems or hypervisors.
Why the Perimeter Model Failed
The perimeter model was not stupid. It was designed for a world that no longer exists. When your applications ran in your data center, your users worked in your buildings, and your data lived on your servers, a strong perimeter made sense. Guard the gates, and you protect the kingdom.
Several tectonic shifts destroyed that model:
Cloud adoption blew holes in the perimeter. Your applications now run in AWS, Azure, GCP, and a dozen SaaS platforms. There is no single perimeter to defend because your resources are everywhere.
Remote and hybrid work means your users are everywhere too. The VPN was supposed to solve this by extending the perimeter to remote workers, but in practice it gave remote users the same broad internal access, creating a tunnel straight into your network from devices you do not fully control.
Sophisticated attackers realized that getting past the perimeter was the hard part. Once inside, most networks offered minimal resistance to lateral movement. Advanced Persistent Threats (APTs) would spend months quietly moving through flat internal networks, escalating privileges and exfiltrating data.
Supply chain attacks introduced trusted-but-compromised code into the heart of the perimeter. SolarWinds was the textbook case. The attack came through a trusted vendor’s legitimate update mechanism. The perimeter was never breached; the threat was invited in through the front door.
The Zero Trust Architecture
Implementing Zero Trust requires rethinking your architecture across multiple dimensions. It is not a single project; it is a transformation that touches identity, network, applications, data, and operations.
Identity as the New Perimeter
In a Zero Trust architecture, identity replaces the network boundary as the primary security control plane. Every access decision starts with a verified identity.
This goes beyond just usernames and passwords. Strong identity in Zero Trust means:
- Multi-factor authentication for every user, every time, without exceptions for “internal” users
- Device identity and health verification: Is the device managed? Is the OS patched? Is the endpoint protection running?
- Service identity: Workloads and applications also need verified identities, typically through certificates or tokens
- Continuous validation: Identity is not verified once at login; it is re-evaluated continuously throughout the session
Understanding the distinction between authentication and authorization is absolutely critical here. Authentication proves who you are. Authorization determines what you can do. Zero Trust demands excellence at both.
Microsegmentation
If you are assuming breach (principle three), then you need to limit what an attacker can reach once they compromise a single resource. Microsegmentation divides your network into small, isolated segments with strictly controlled communication between them.
In practice, this means:
- Workload-level segmentation: Each application tier or microservice can only communicate with specifically authorized peers
- Default deny: No traffic flows unless explicitly permitted by policy
- East-west traffic inspection: Traffic between internal services is inspected with the same rigor as north-south traffic crossing the perimeter
This is a massive shift from the flat networks I used to see in enterprise environments. I recall one financial institution where every server on a /16 network could talk to every other server. An attacker who compromised a single development workstation could reach the production database servers directly. With microsegmentation, that path simply would not exist.
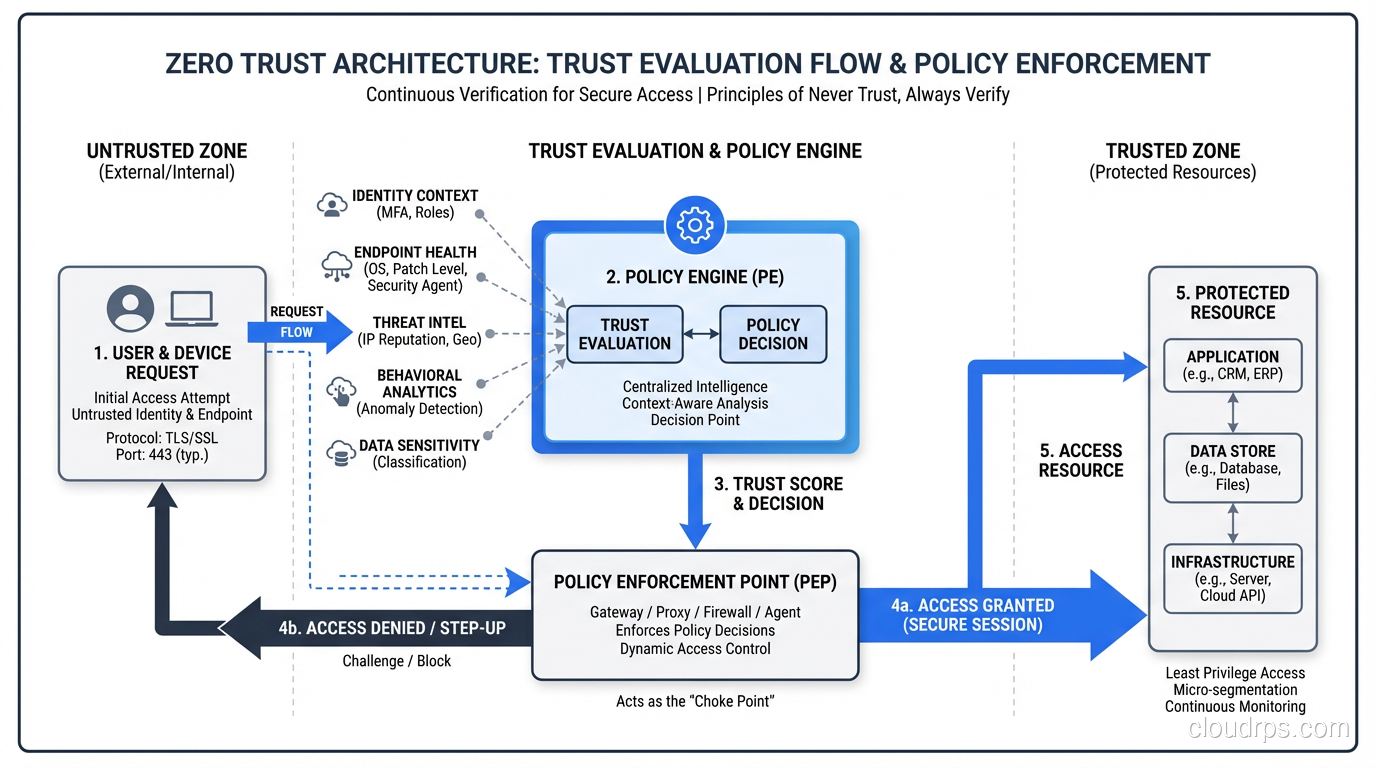
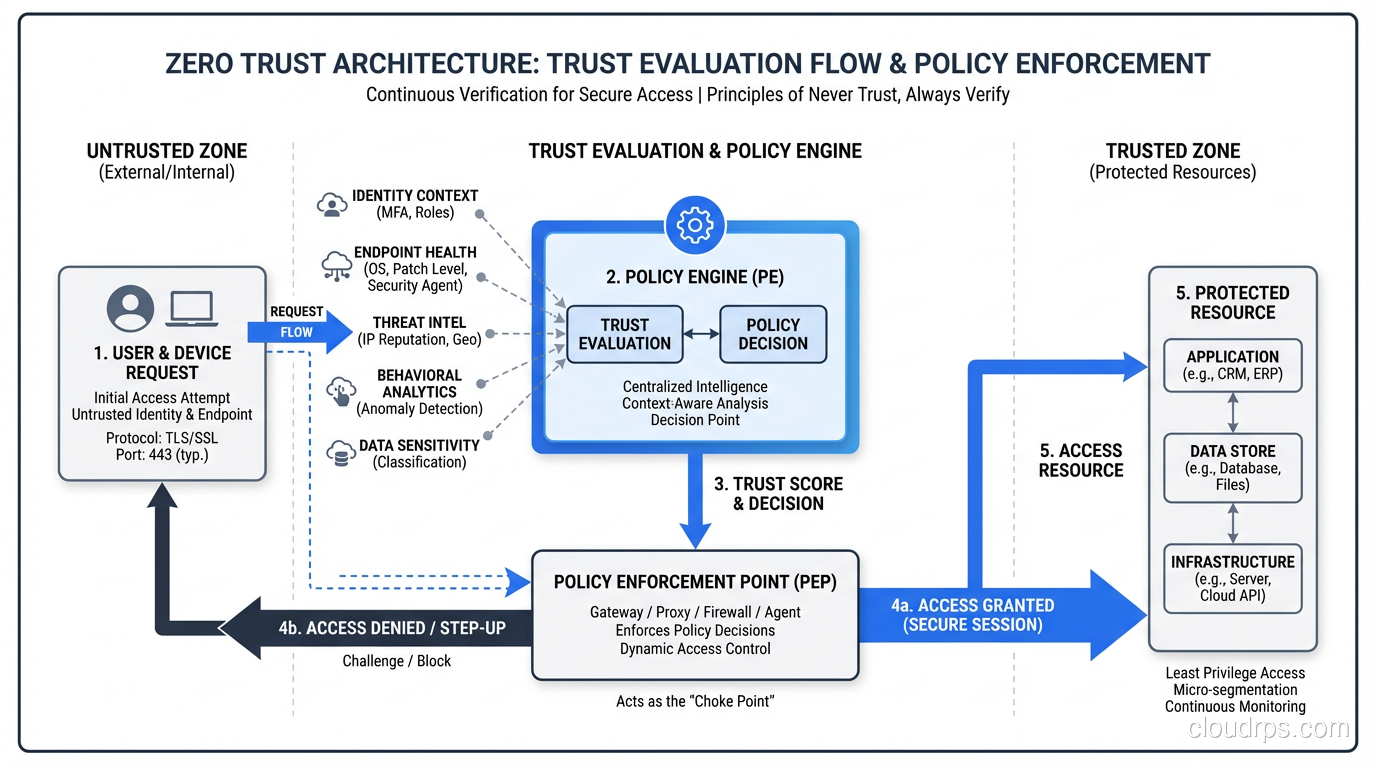
The Policy Engine
At the heart of a Zero Trust architecture is a policy decision point, often called the Policy Engine or Policy Decision Point (PDP). This component evaluates every access request against defined policies, considering:
- Who is requesting access (identity)?
- What device are they using (device posture)?
- What resource are they trying to access?
- What is the context (time, location, risk score)?
- What is the minimum access needed?
The Policy Enforcement Point (PEP), whether a gateway, proxy, or agent, enforces the decision. If the PDP says deny, the PEP blocks the request. If the PDP says allow, the PEP permits it with the specified constraints.
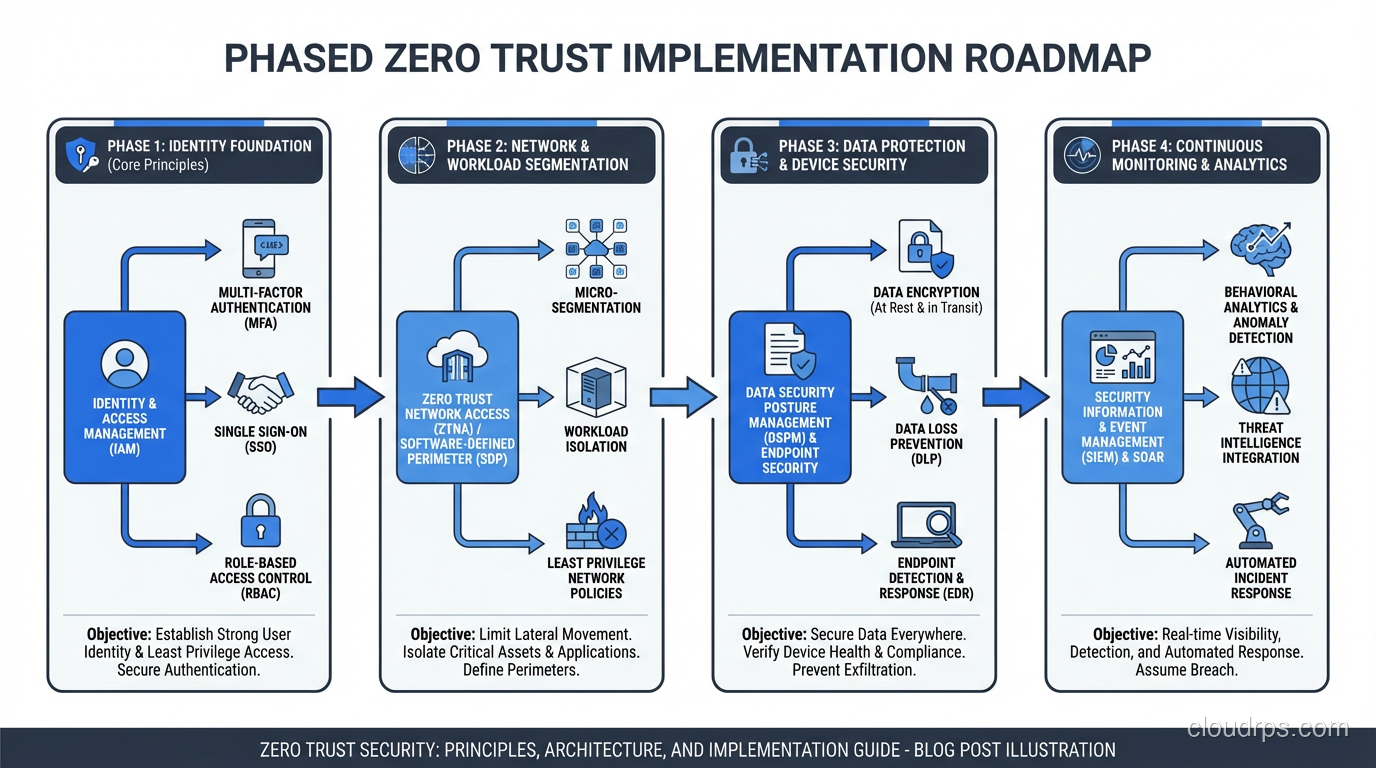
Implementation: Where to Start
Every organization I have helped implement Zero Trust has asked the same question: “Where do we start?” The answer depends on your current state, but here is the framework I use.
Phase 1: Identity Foundation
You cannot do Zero Trust without strong identity. This is always step one.
- Deploy a modern identity provider with single sign-on (SSO) capabilities
- Enforce MFA everywhere, not just for VPN, not just for cloud apps, everywhere
- Implement conditional access policies that evaluate device health and risk signals
- Establish a service identity framework for workload-to-workload communication
If you are still using shared credentials, local accounts on servers, or password-only authentication anywhere in your environment, fix that before worrying about anything else. And those credentials themselves need proper lifecycle management, including rotation, injection, and revocation. I cover this in depth in my guide to secret management in the cloud.
Phase 2: Device Trust
Once you know who is asking, verify what they are asking from.
- Deploy endpoint detection and response (EDR) on all managed devices
- Implement device compliance checks as a condition for access
- Establish policies for unmanaged devices (BYOD), typically more restrictive access through web-based portals rather than native client access
- Use device certificates for machine-level identity
Phase 3: Network Segmentation
With identity and device trust established, start segmenting your network.
- Begin with the highest-value assets: databases containing sensitive data, administrative interfaces, production infrastructure
- Implement microsegmentation around those assets first
- Use software-defined networking and next-generation firewalls to enforce segment boundaries
- Log all cross-segment traffic for baseline analysis
Phase 4: Application-Level Controls
Move security controls closer to the applications themselves.
- Replace VPN-based access with identity-aware proxies (BeyondCorp-style architecture)
- Implement API gateways with authentication and authorization for service-to-service communication
- Deploy intrusion detection and prevention at the application layer
- Encrypt all traffic end-to-end, including internal east-west traffic
Phase 5: Continuous Monitoring and Analytics
Zero Trust is not a set-it-and-forget-it model. Continuous monitoring is essential.
- Aggregate logs from identity, network, and application layers
- Implement behavioral analytics to detect anomalous access patterns
- Automate response to high-confidence threat indicators
- Continuously refine policies based on observed patterns
Real-World Zero Trust: What It Looks Like
Let me describe what a mature Zero Trust environment actually feels like from the user’s perspective, because this is where a lot of the fear and resistance comes from.
A developer sits down at their laptop in the morning. The laptop is managed and has an EDR agent running. They authenticate with their identity provider using a hardware security key (FIDO2). The identity provider checks the device’s compliance status (OS version, patch level, disk encryption, EDR running). Everything checks out.
They open their browser and navigate to an internal application. The identity-aware proxy intercepts the request, validates the session token, checks the access policy (developer role + managed device + low-risk session = access granted to development environment), and proxies the request to the application.
Later, the developer needs to SSH into a production server to investigate an incident. They request access through a privileged access management (PAM) system. The request is evaluated: their role permits production access for troubleshooting, but only for a limited time window. Access is granted for 60 minutes with full session recording. After 60 minutes, the access is automatically revoked.
At no point did the developer connect to a VPN. At no point were they on a “trusted network.” Every access was individually authenticated, authorized, logged, and time-bounded.
Common Implementation Mistakes
Mistake 1: Trying to Boil the Ocean
I have seen organizations attempt to implement Zero Trust across their entire environment simultaneously. This always fails. You end up with half-implemented controls everywhere and working controls nowhere. Start with your crown jewels, the systems and data that would cause the most damage if compromised, and expand from there.
Mistake 2: Zero Trust Theater
Buying a product labeled “Zero Trust” and calling it done is not Zero Trust. I have encountered vendors who slap a “Zero Trust” label on what is essentially a next-generation firewall. If your implementation is a single product deployment without changes to identity, access policies, and network architecture, you are doing Zero Trust theater.
Mistake 3: Ignoring User Experience
If your Zero Trust implementation makes it harder for people to do their jobs, they will find workarounds. And workarounds are where security dies. The goal is to make security invisible: strong authentication that is not burdensome (hardware keys, biometrics), seamless application access that does not require VPN connections, and just-in-time access that grants permissions quickly when legitimately needed.
Mistake 4: Not Planning for Legacy Systems
Every organization has legacy systems that cannot support modern authentication protocols. Mainframes, old ERP systems, industrial control systems: they are not going away anytime soon. Your Zero Trust architecture needs to account for these. Typically this means placing identity-aware gateways in front of legacy systems that handle the modern authentication and translate it into whatever the legacy system understands.
Zero Trust in Cloud Environments
Cloud environments are actually better suited for Zero Trust than traditional on-premises networks, because the building blocks are already there.
Identity: Cloud providers offer mature IAM systems with support for MFA, conditional access, and fine-grained permissions.
Microsegmentation: Security groups, network policies, and service mesh provide workload-level segmentation out of the box.
Encryption: Cloud providers encrypt data in transit by default between their services and provide straightforward encryption at rest.
Logging: Cloud audit logs capture every API call, every access attempt, every configuration change.
The challenge in cloud is that the default configurations are rarely Zero Trust. Default VPCs have broad internal routing. Default IAM policies are often over-permissioned. Default security groups may be too permissive. You need to actively tighten these defaults.
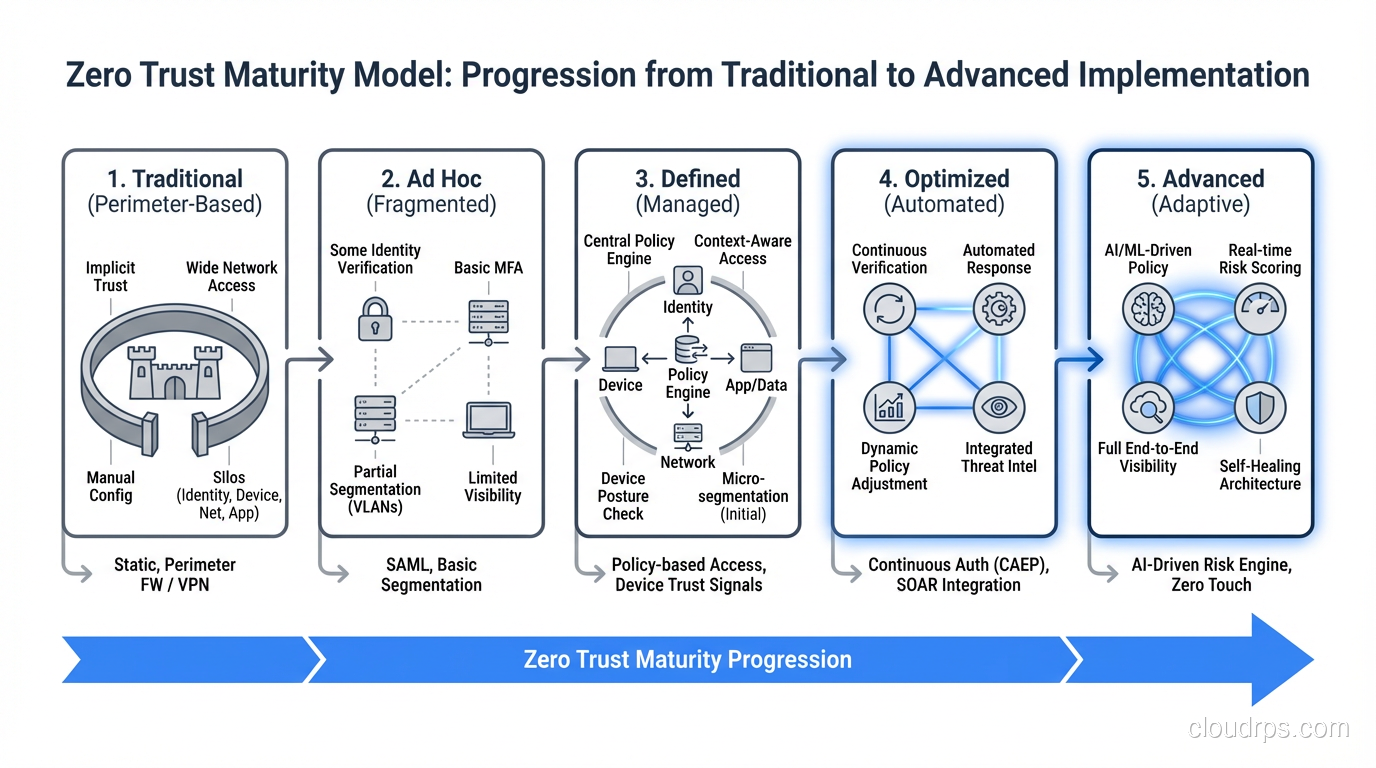
Measuring Zero Trust Maturity
How do you know if your Zero Trust implementation is working? Here are the metrics I track:
- Percentage of access requests evaluated by the policy engine: Target: 100%
- Percentage of users on MFA: Target: 100%, no exceptions
- Percentage of network segments with default-deny policies: Higher is better, but prioritize high-value assets
- Mean time to detect lateral movement: This should decrease as your monitoring improves
- Blast radius of simulated compromises: Run red team exercises and measure how far an attacker gets. Over time, the blast radius should shrink.
- Number of standing privileges vs. just-in-time access: Standing privileges should decrease quarter over quarter
Wrapping Up
Zero Trust is a journey, not a destination. I have been working on Zero Trust implementations since before the term was popularized by Forrester in 2010, when we just called it “least-privilege micro-segmented architecture” (which is admittedly a terrible name). The core ideas are sound and battle-tested.
What has changed is that the tools and platforms have matured to the point where Zero Trust is practical for organizations of all sizes, not just Google-scale companies with custom infrastructure. Cloud-native identity providers, software-defined networking, and identity-aware proxies are all available as managed services.
But tools alone do not make Zero Trust. It requires a cultural shift, from “inside the network means trusted” to “verify everything, every time.” That cultural shift is the hardest part, and it starts at the top.
Start with identity. Get MFA right. Segment your most critical assets. Build out from there. Every step you take toward Zero Trust reduces your attack surface and limits the damage when (not if) an attacker gets past your outer defenses. Because they will.
Get Cloud Architecture Insights
Practical deep dives on infrastructure, security, and scaling. No spam, no fluff.
By subscribing, you agree to receive emails. Unsubscribe anytime.