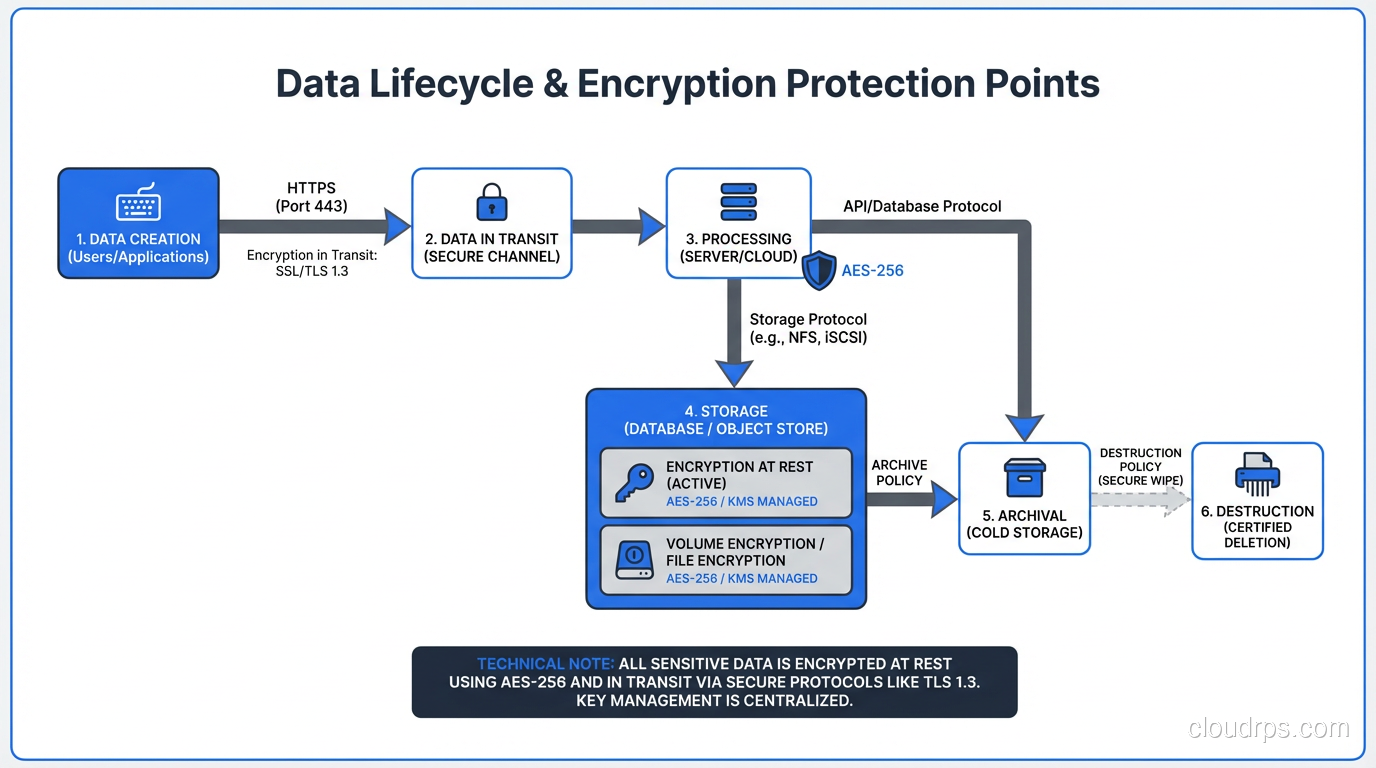
Encryption at Rest vs In Transit: A Complete Guide to Data Protection
Comprehensive guide to encryption at rest and in transit covering implementation, key management, TLS configuration, performance impact, and compliance requirements.
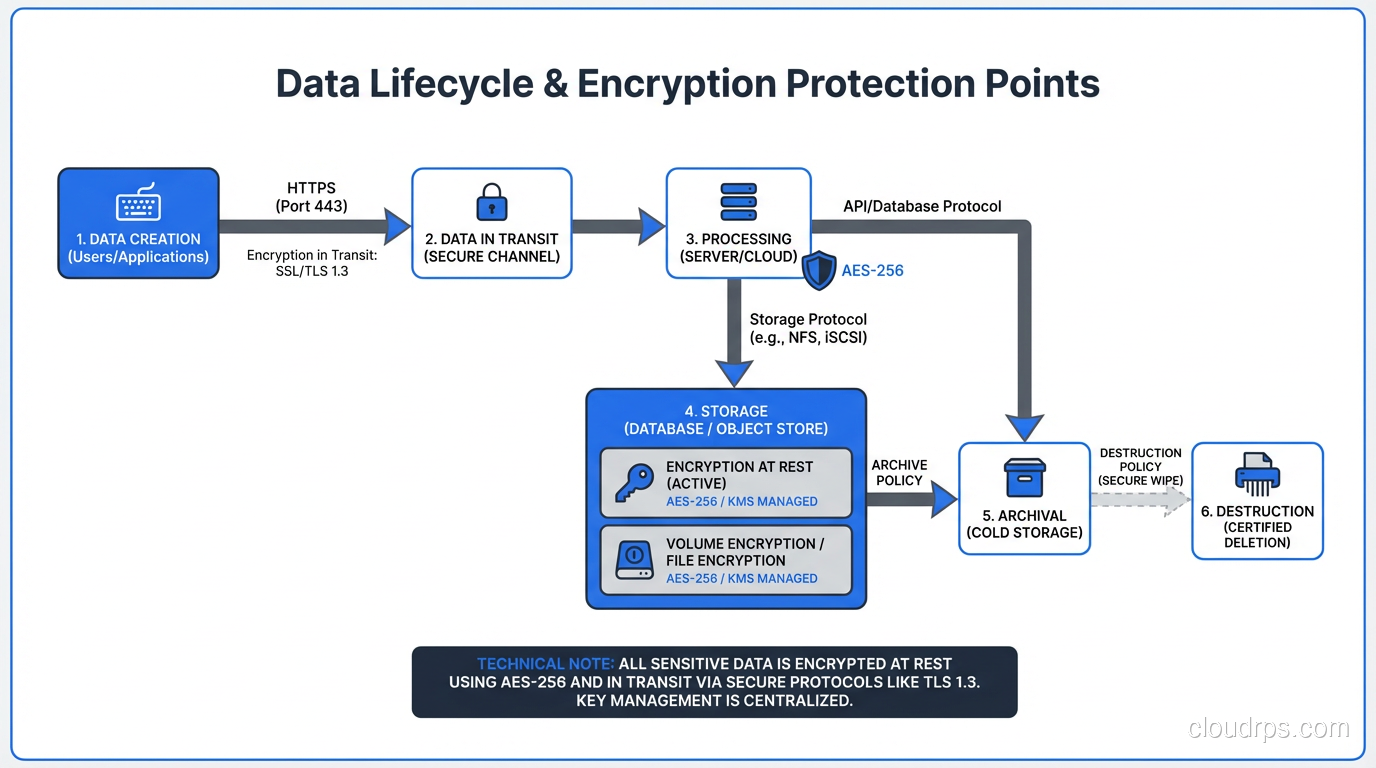
Comprehensive guide to encryption at rest and in transit covering implementation, key management, TLS configuration, performance impact, and compliance requirements.
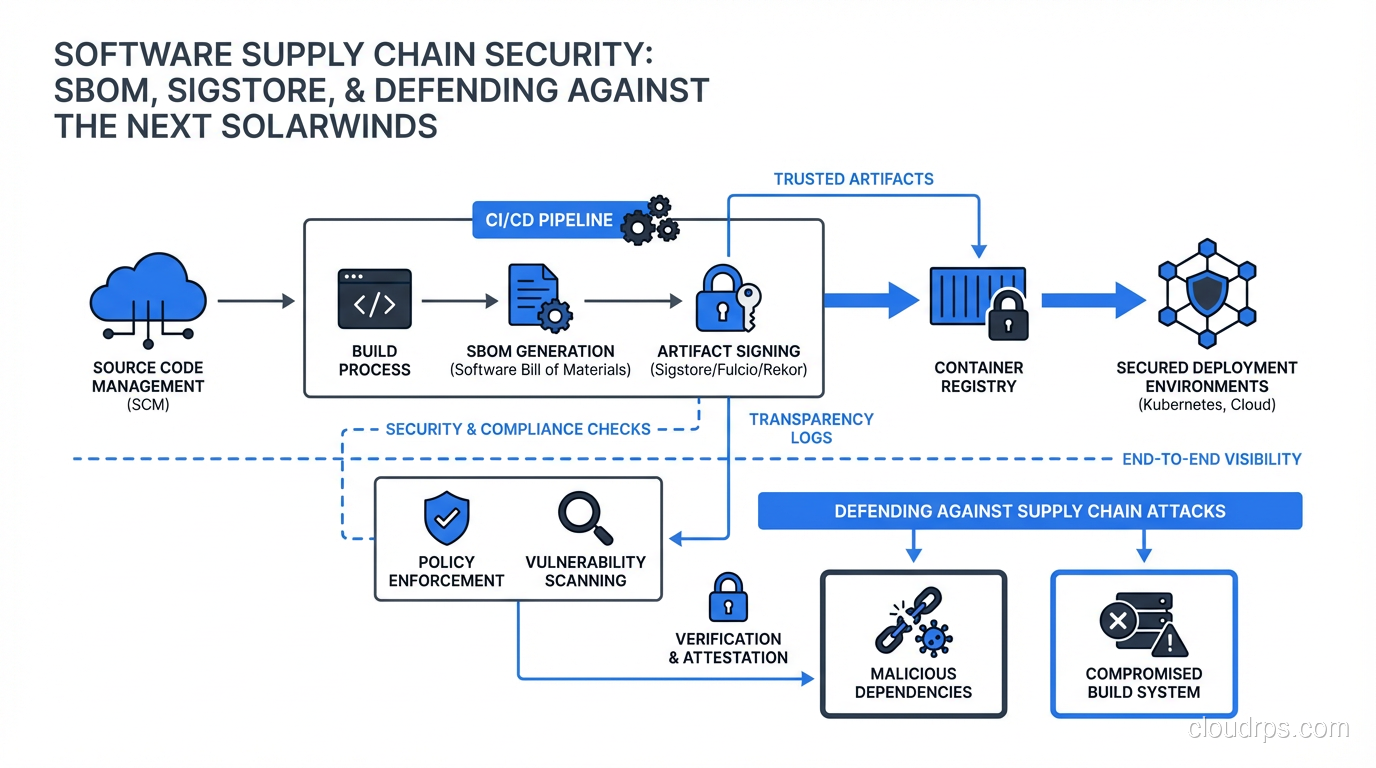
Software supply chain attacks are the new perimeter breach. Here's how SBOMs, Sigstore, and artifact signing work together to defend your build pipeline.
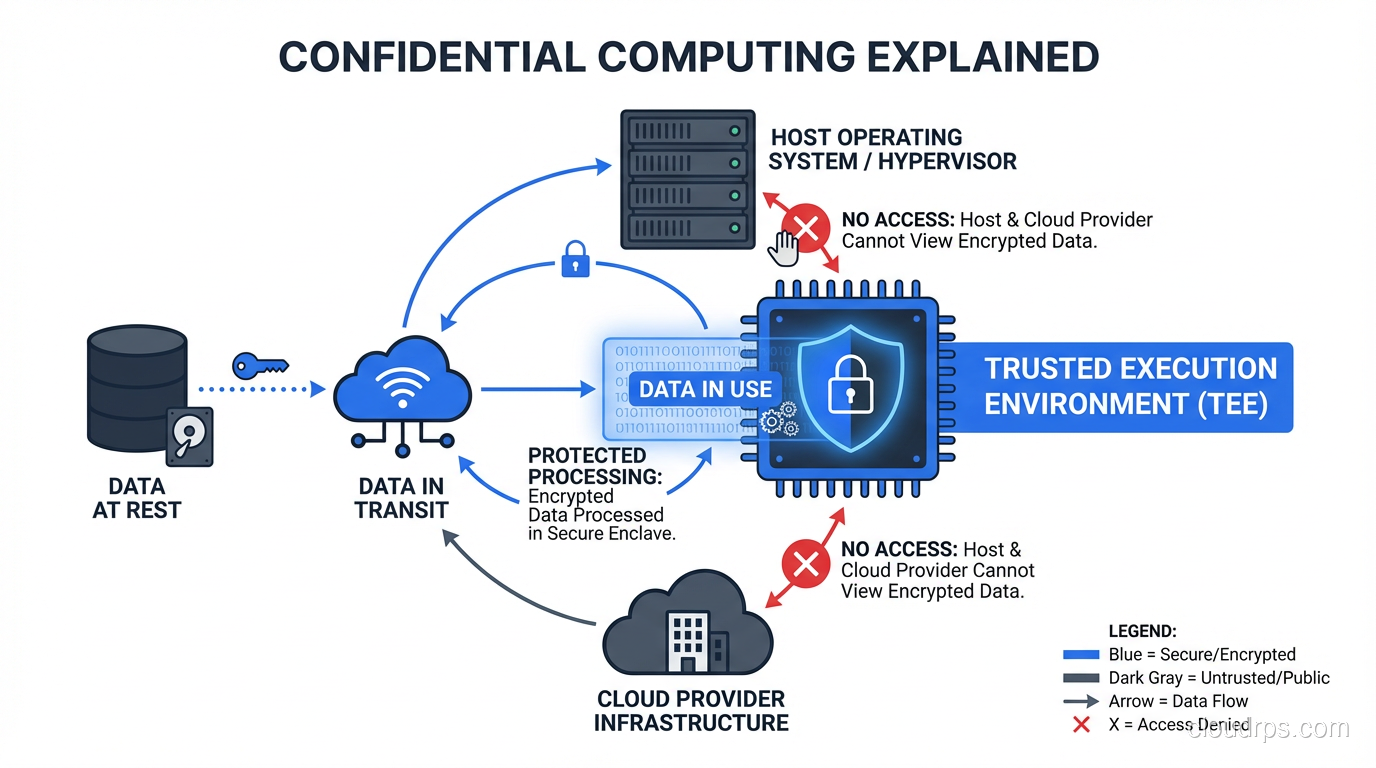
Learn how confidential computing and trusted execution environments (TEEs) protect data while it's being processed, with practical guidance on Intel SGX, AMD SEV, and cloud provider implementations.
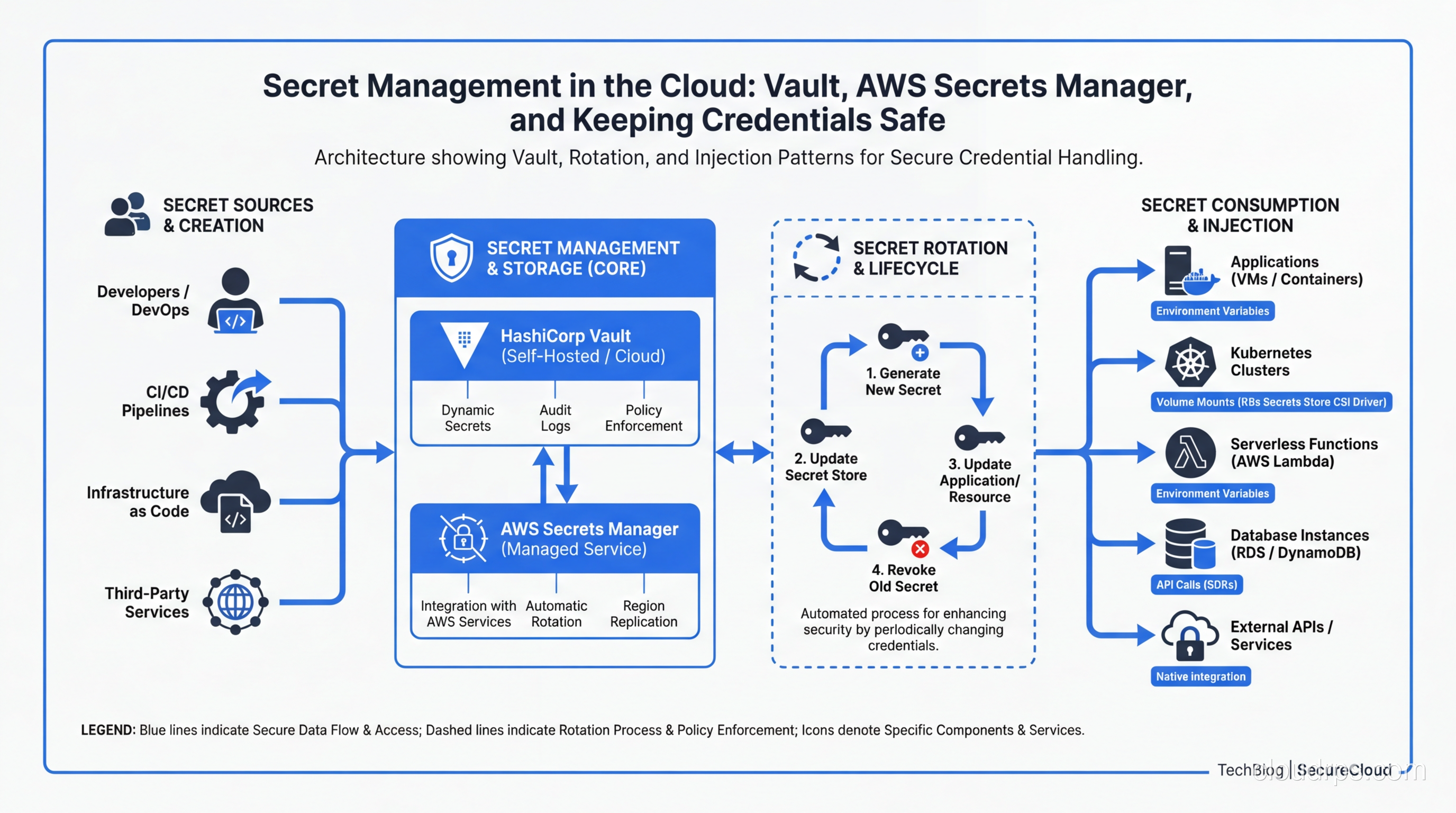
A practical guide to managing secrets in cloud infrastructure: comparing HashiCorp Vault, AWS Secrets Manager, and other tools, with real-world patterns for rotation, injection, and zero-trust secret delivery.
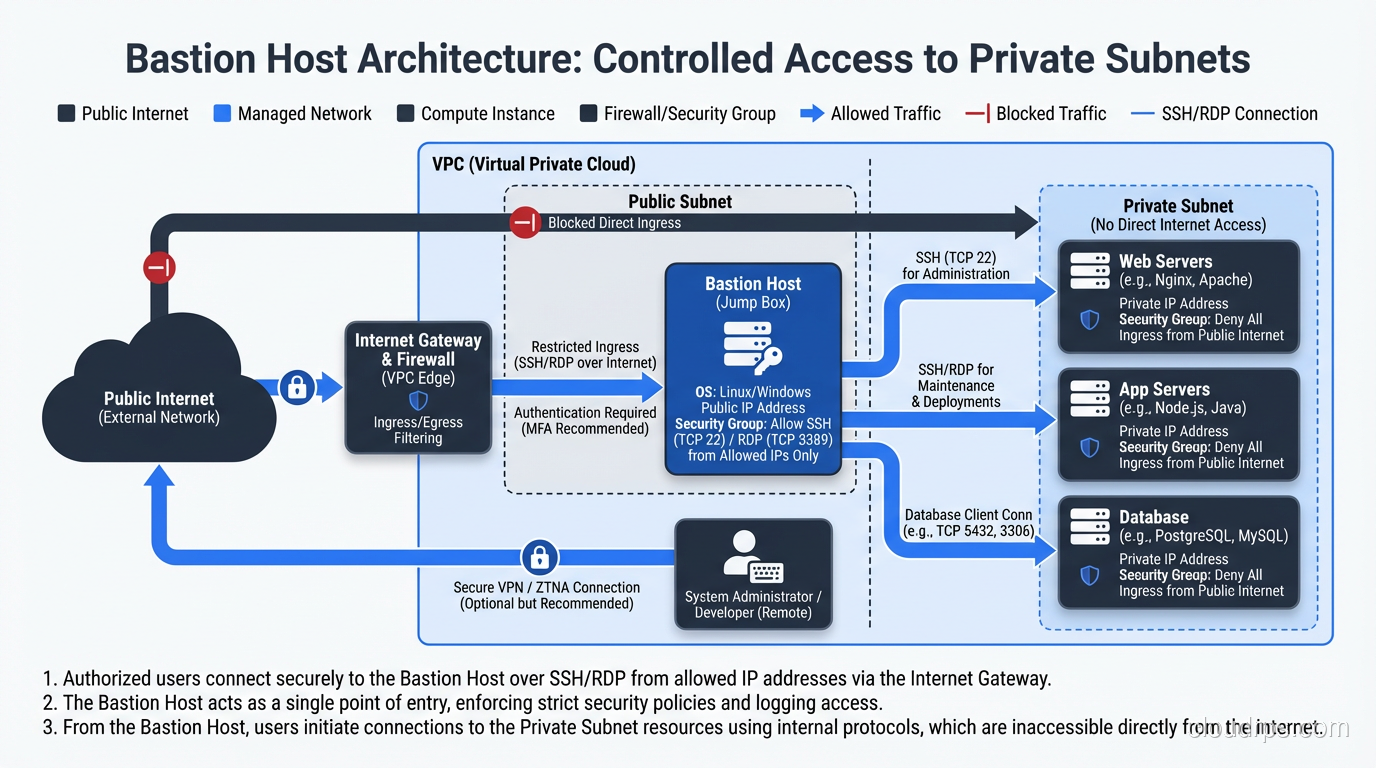
Bastion hosts and jump boxes explained by a principal architect. Learn secure access patterns, hardening practices, and modern alternatives for private infrastructure.
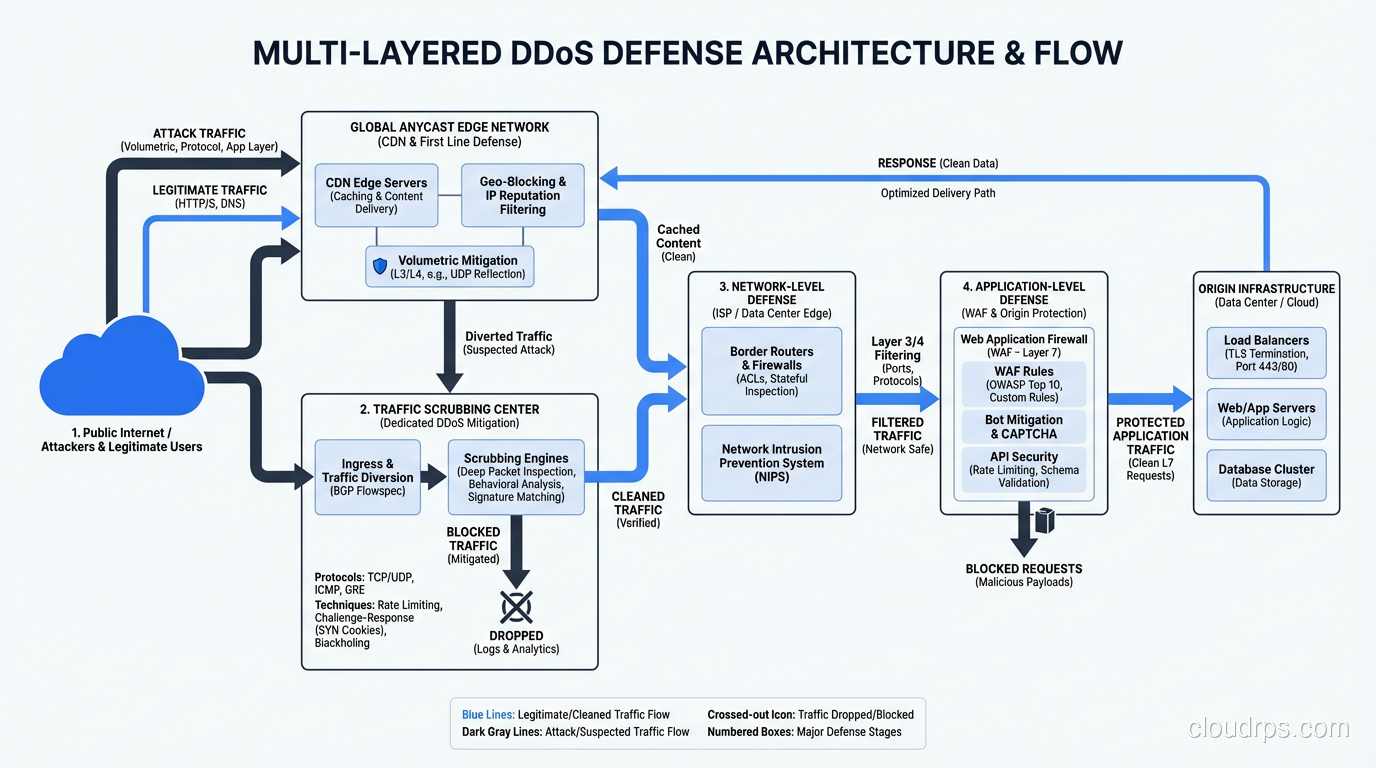
DDoS attacks explained by a veteran architect who has fought them in production. Learn attack types, mitigation strategies, and how to build resilient infrastructure.
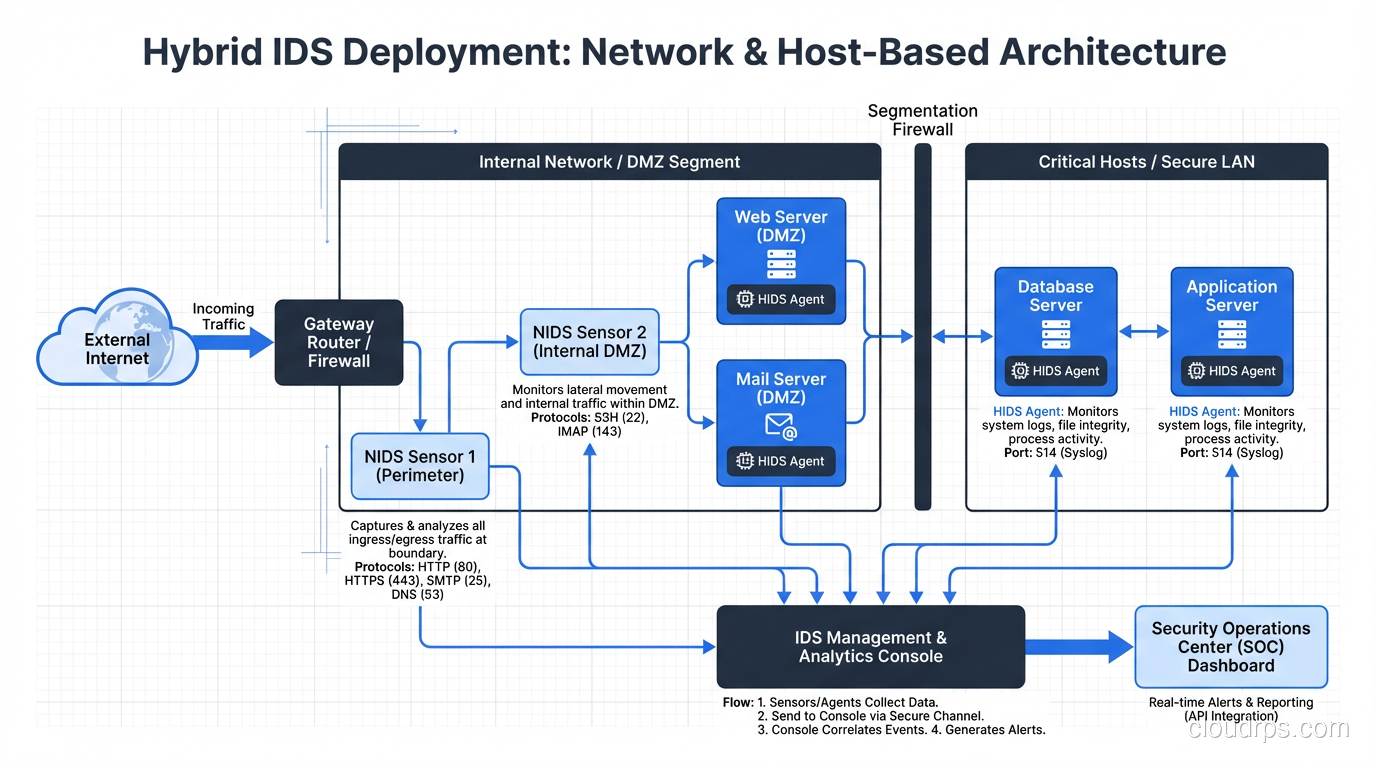
IDS vs IPS explained by a principal architect. Learn how intrusion detection and prevention systems work, when to use each, and how to deploy them in modern networks.
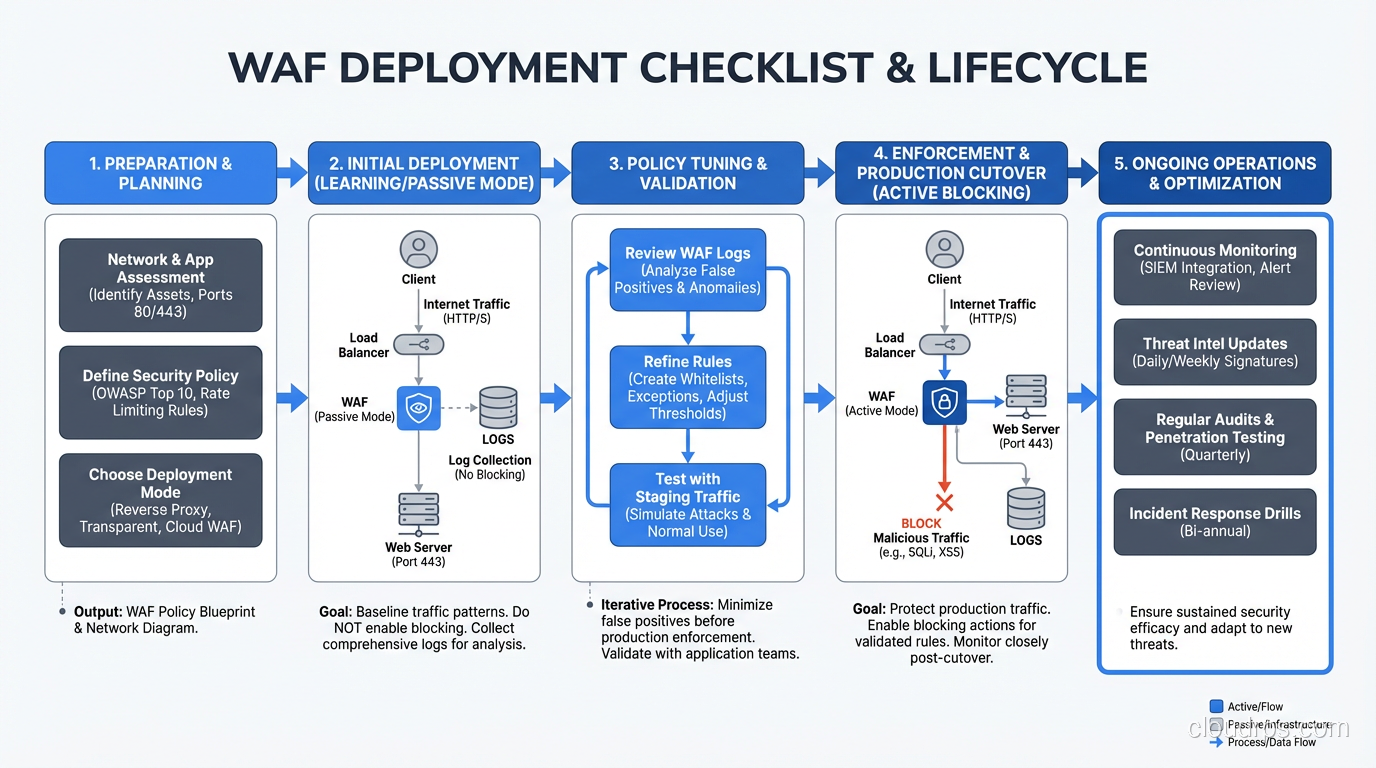
Learn how Web Application Firewalls work at the protocol level. A veteran architect explains WAF deployment models, rule engines, and real-world tuning strategies.
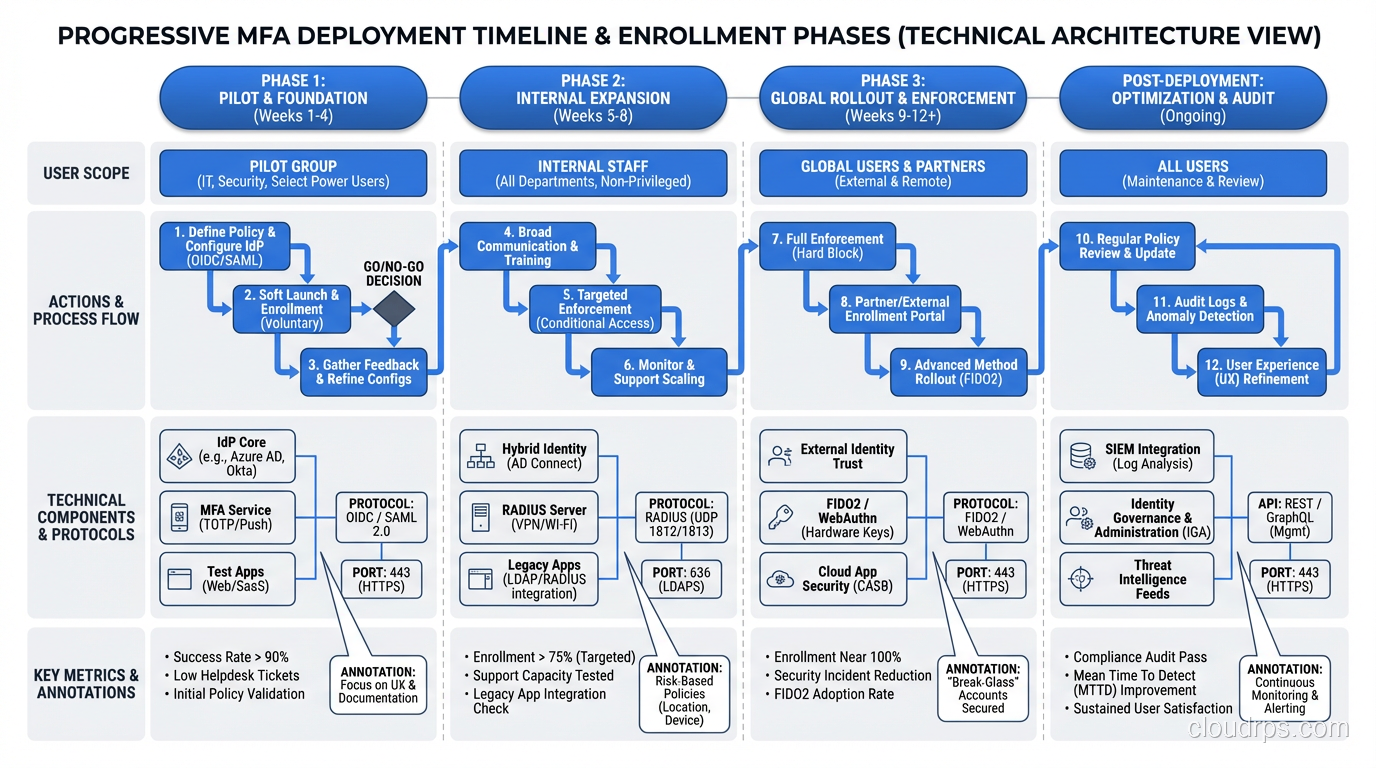
Multi-factor authentication explained by a veteran architect. Learn MFA methods, TOTP vs FIDO2, implementation patterns, and how to deploy MFA without destroying user experience.
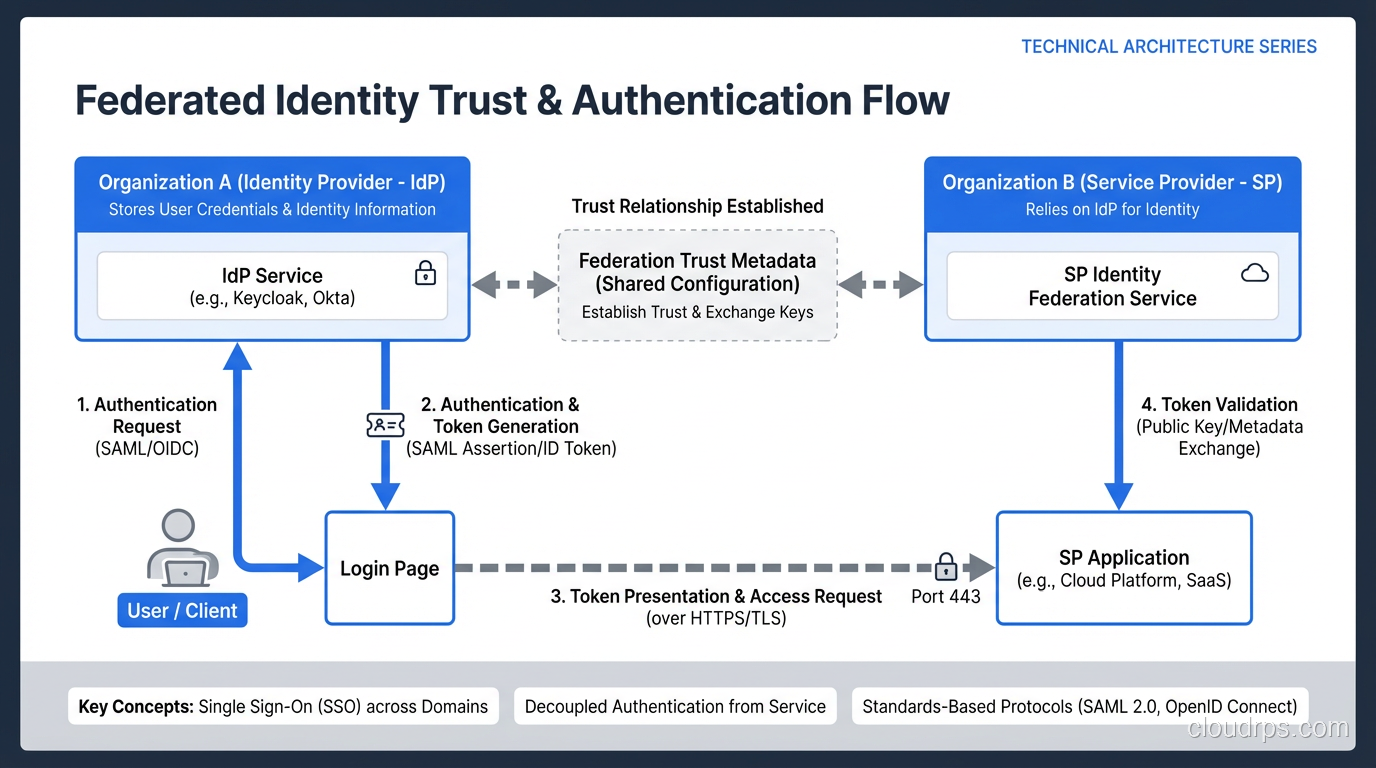
Understand federated identity architecture including SAML, OAuth 2.0, and OpenID Connect. A veteran architect explains when to use each protocol and how they work together.
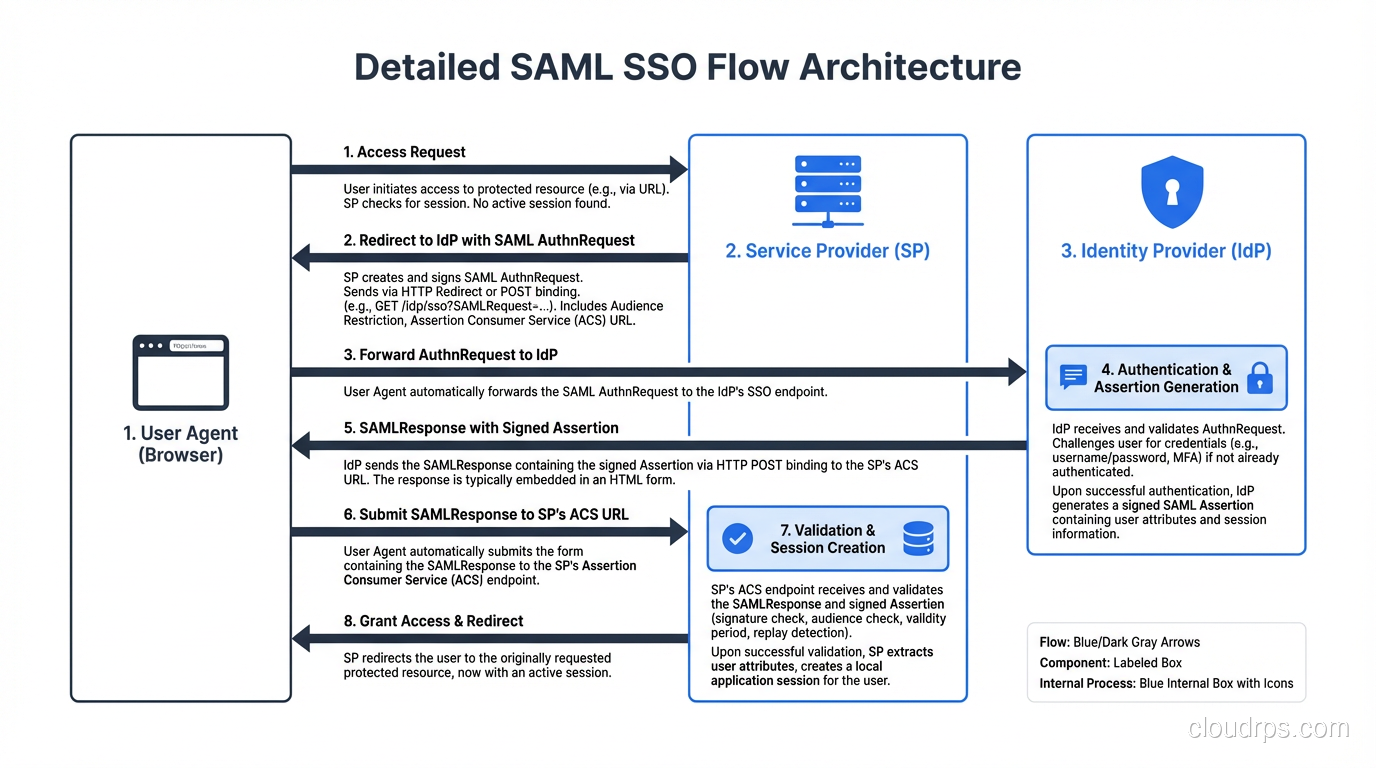
Learn how Single Sign-On works under the hood. A principal architect breaks down SAML, OAuth, OIDC protocols, session management, and SSO implementation patterns.
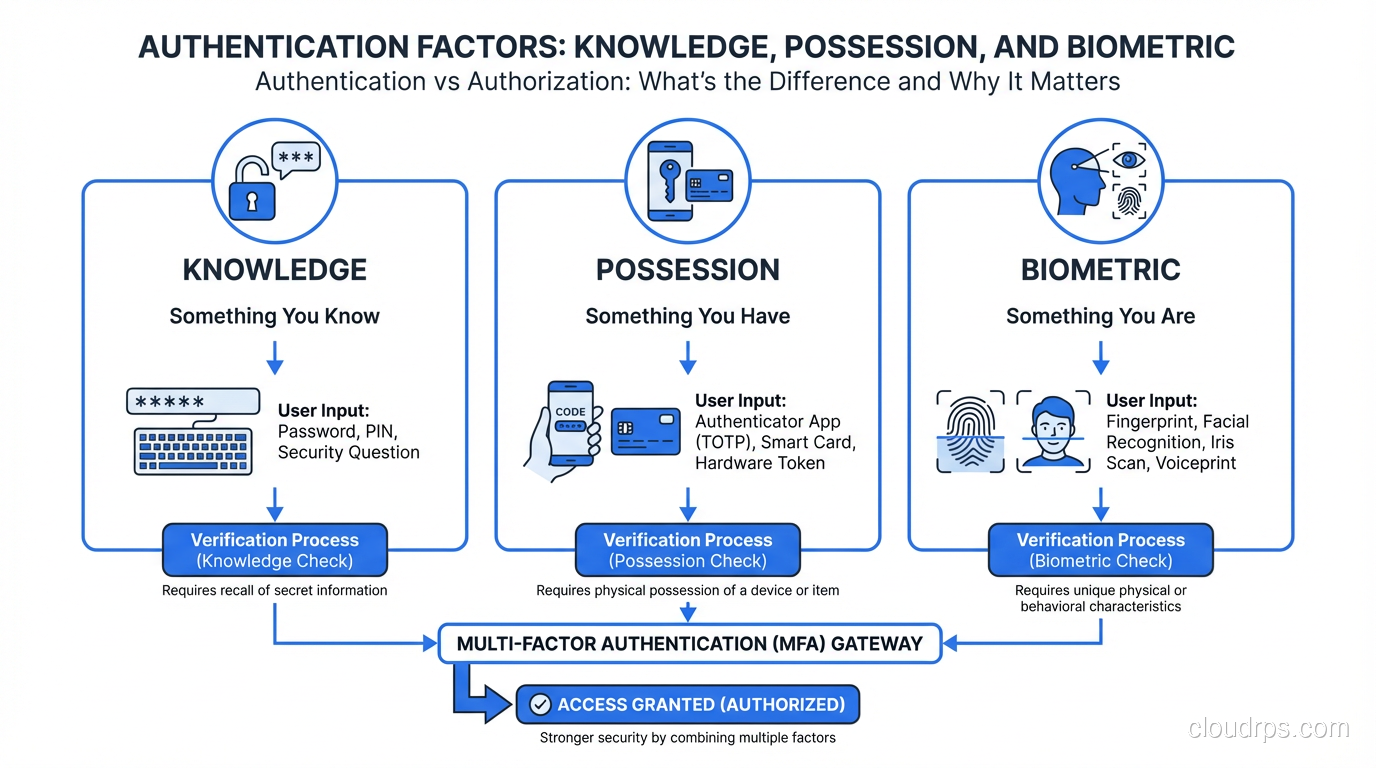
A principal architect breaks down authentication vs authorization, how each works, common protocols like OAuth and SAML, and why confusing them leads to real breaches.
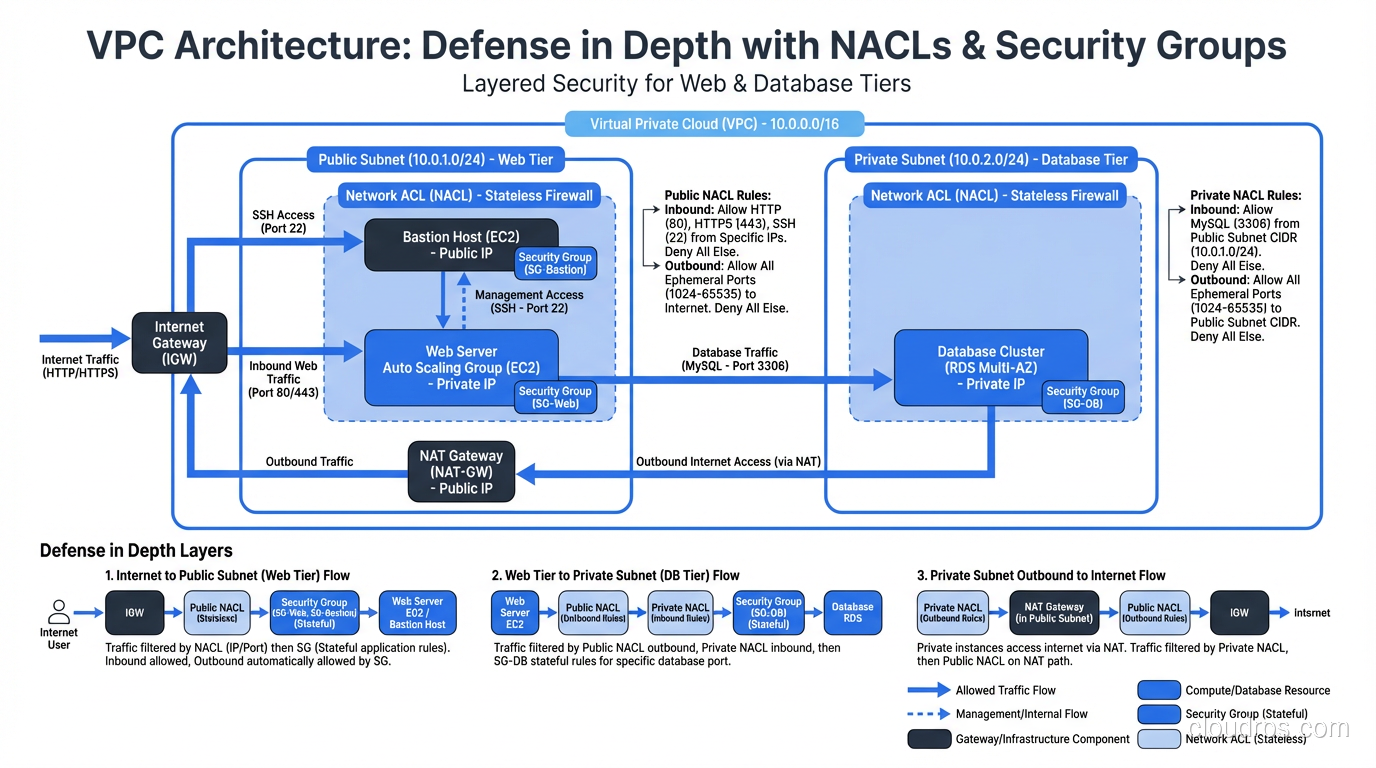
A practitioner's guide to security groups and network ACLs in cloud environments, covering how each works, key differences, and how to layer them for defense in depth.
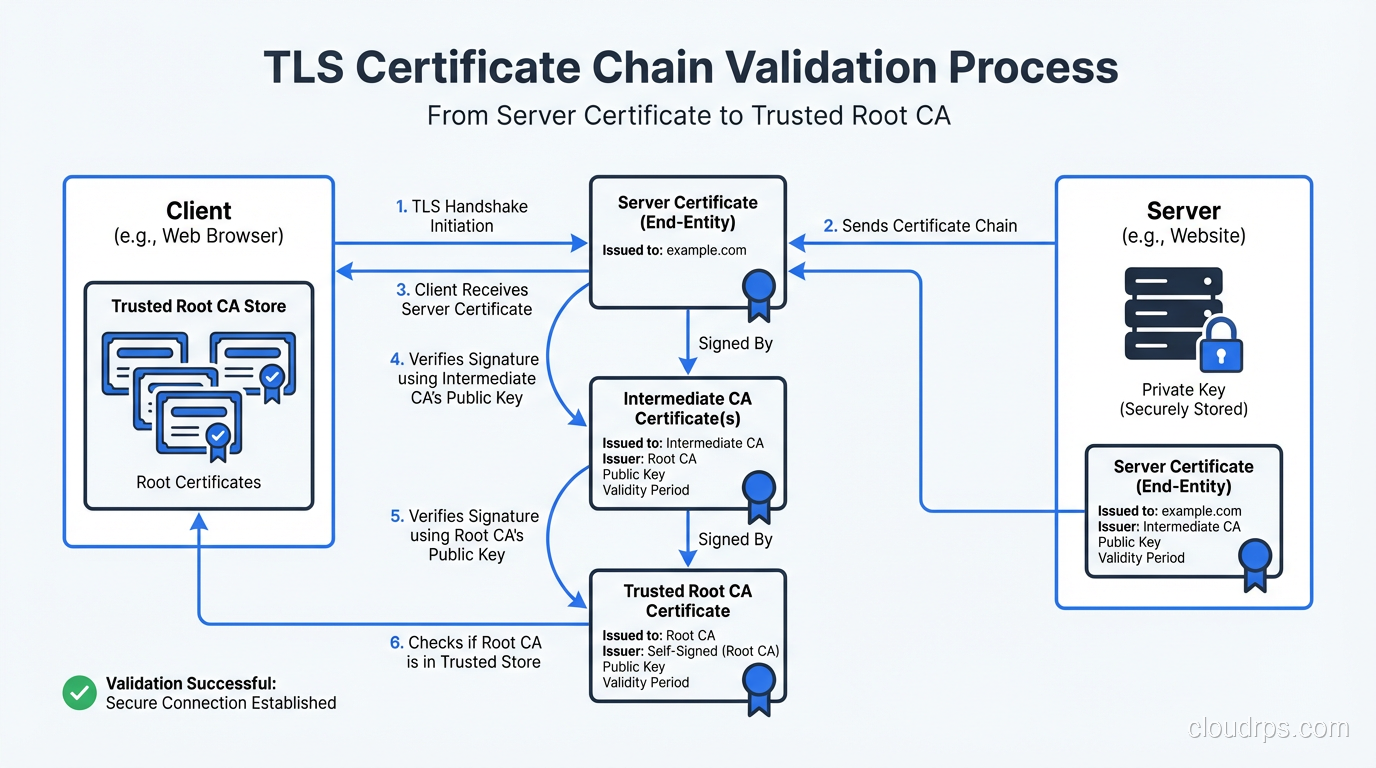
A practitioner's deep dive into how TLS works: the handshake, certificate validation, cipher suites, and what actually happens when your browser connects over HTTPS.
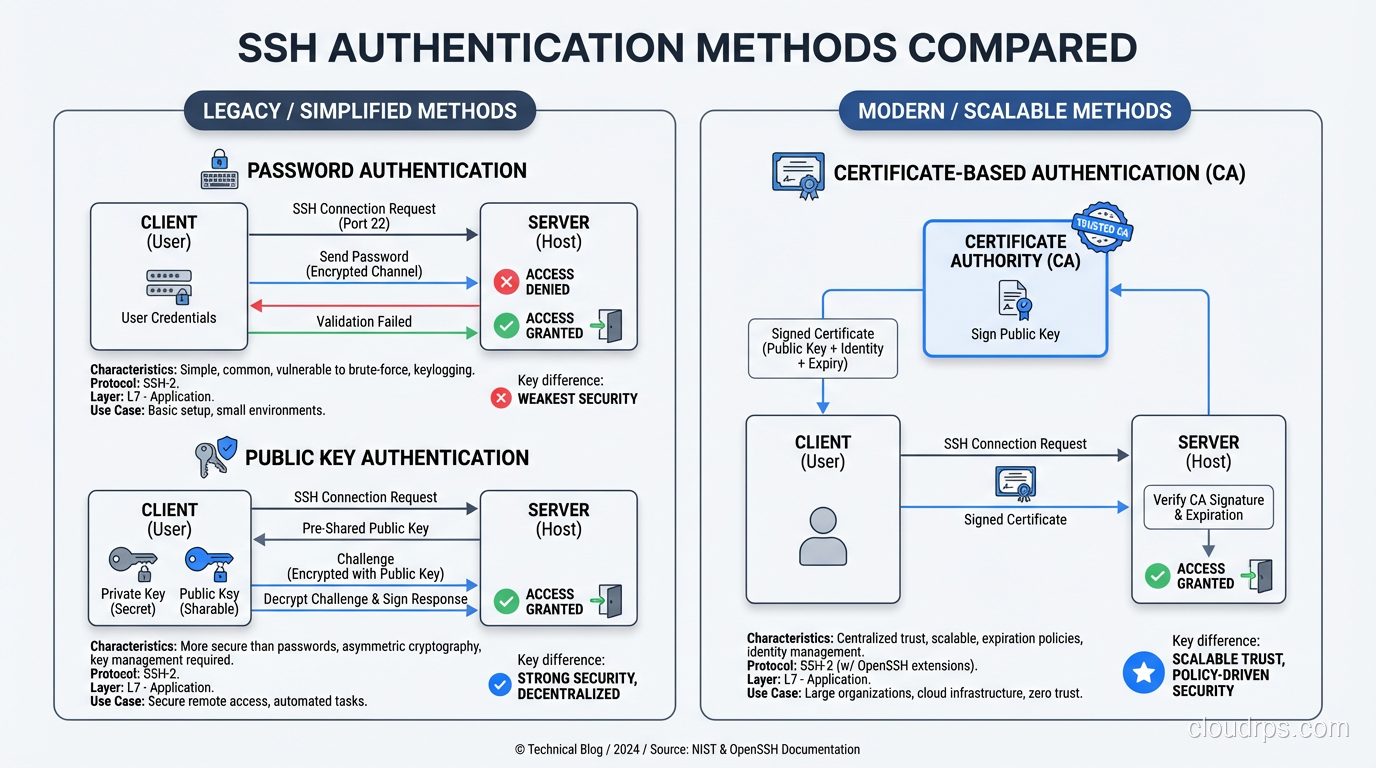
A deep dive into how the SSH protocol actually works: key exchange, host verification, authentication methods, and tunneling explained for practitioners.
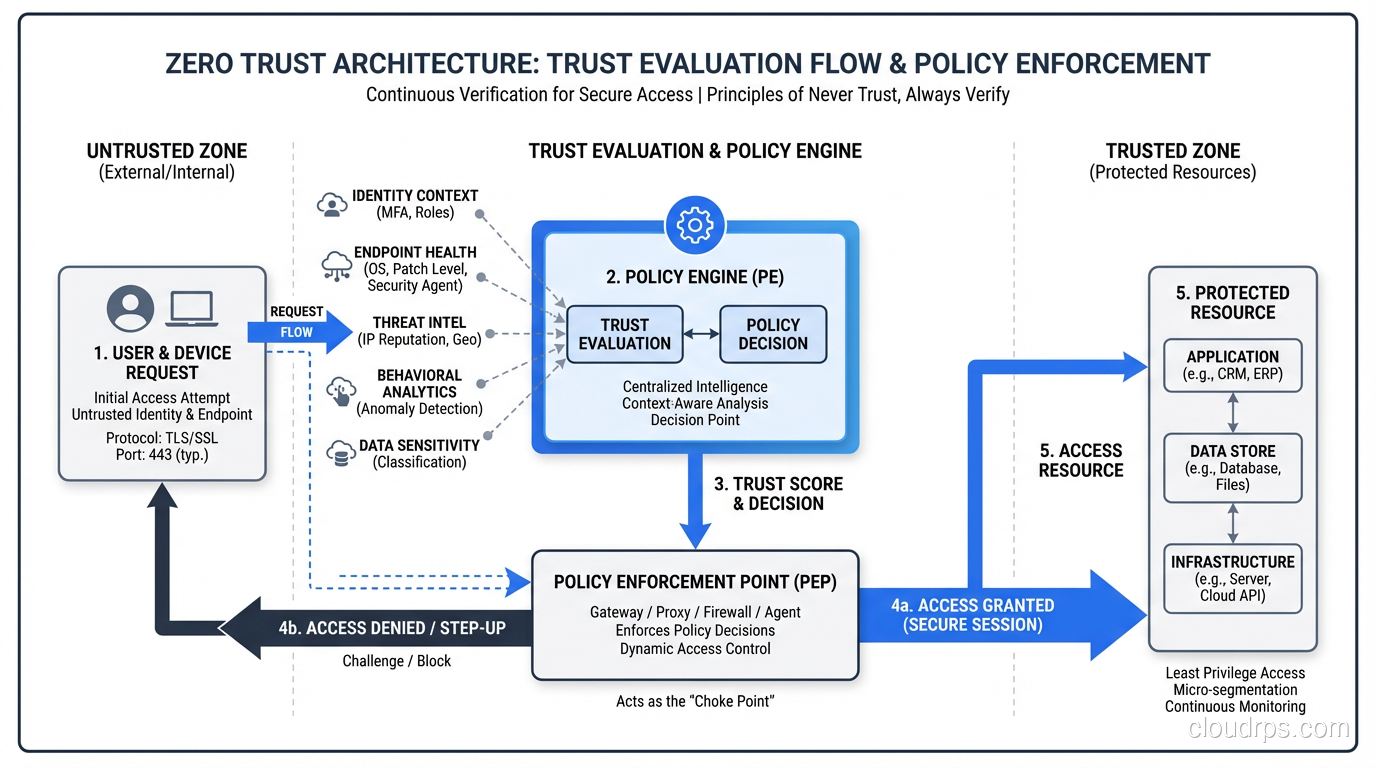
A practical guide to Zero Trust security architecture: core principles, real implementation strategies, and how to move beyond the perimeter model.
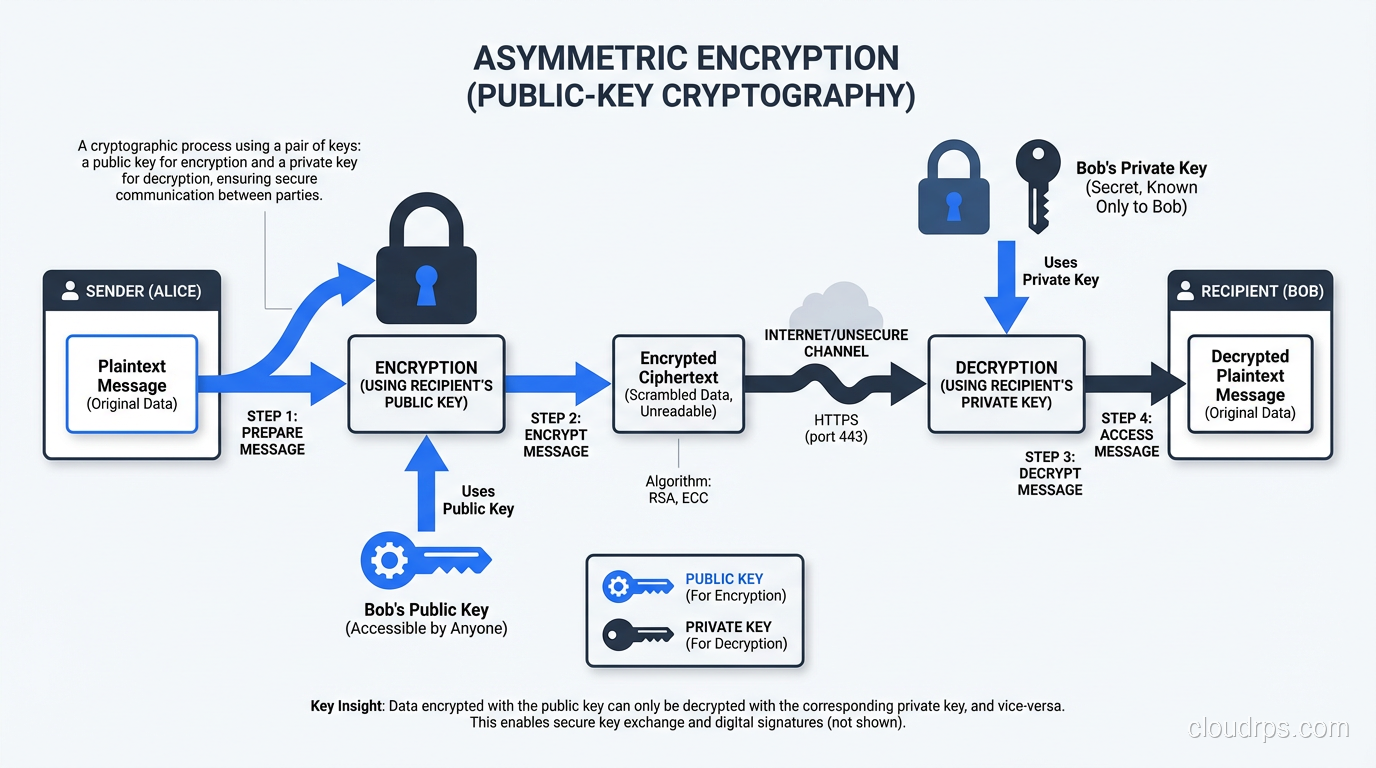
Understand the mechanics of symmetric and asymmetric encryption, compare AES vs RSA vs ECC, and learn how TLS combines both for real-world security.
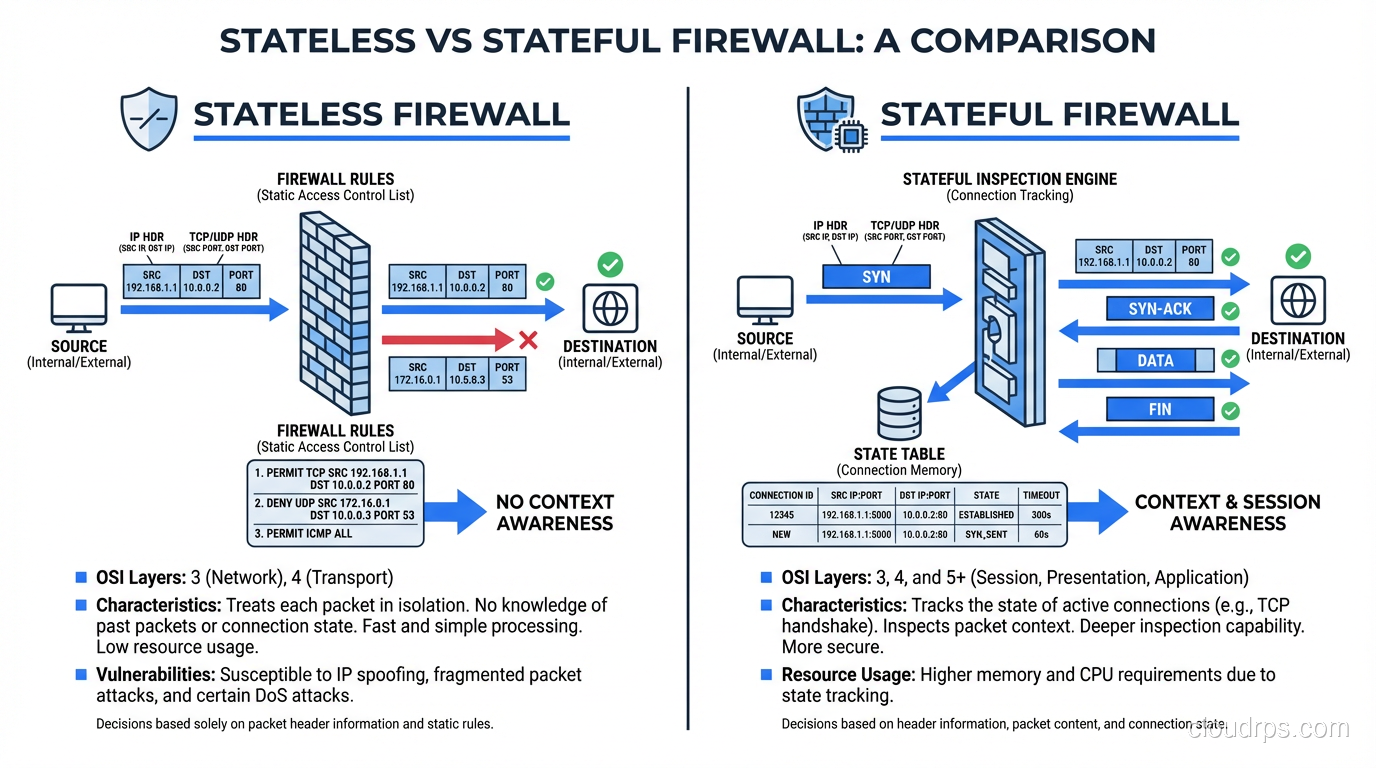
Learn the real differences between stateless and stateful firewalls, how each inspects traffic, and when to deploy them in production network architectures.
Practical deep dives on infrastructure, security, and scaling. No spam, no fluff.
By subscribing, you agree to receive emails. Unsubscribe anytime.