Security
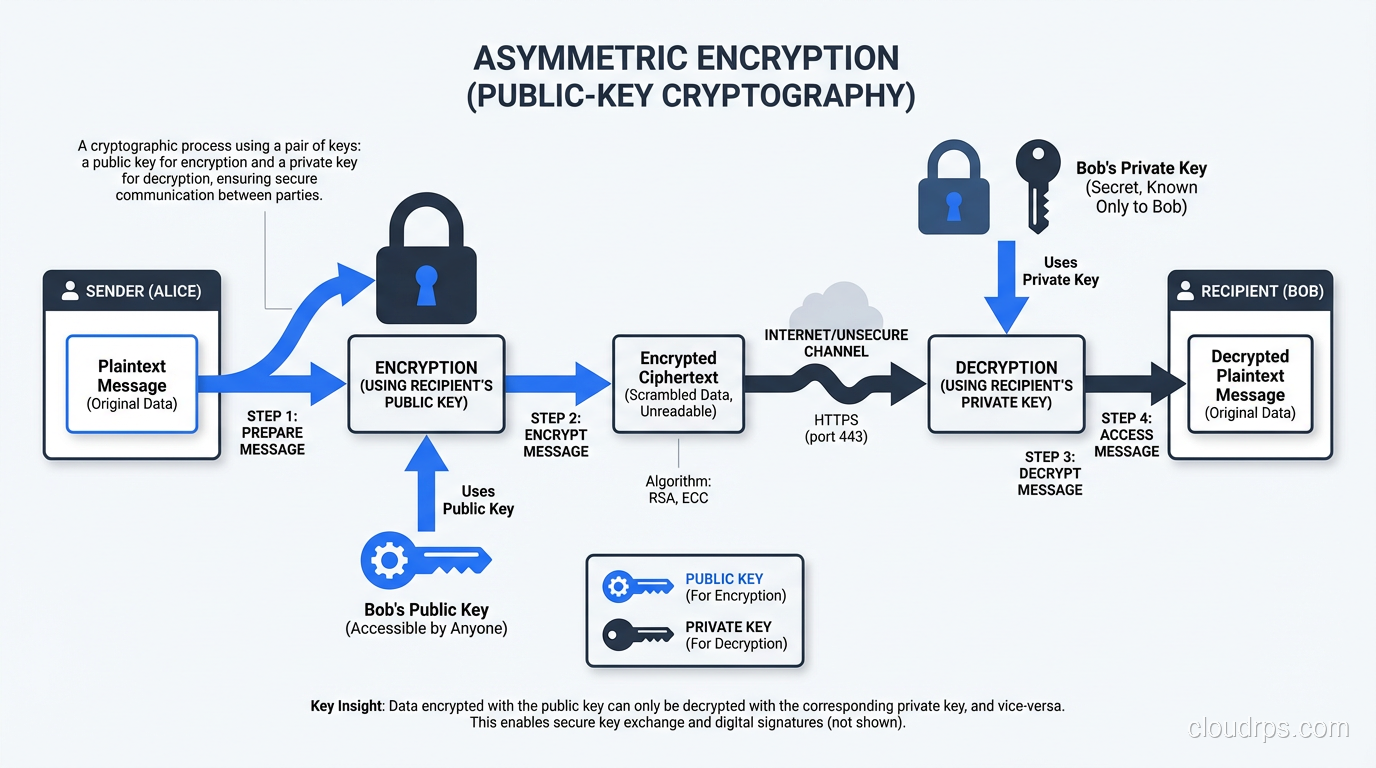
Symmetric vs Asymmetric Encryption: Algorithms, Use Cases, and How They Work Together
Understand the mechanics of symmetric and asymmetric encryption, compare AES vs RSA vs ECC, and learn how TLS combines both for real-world security.
Practical deep dives on infrastructure, security, and scaling. No spam, no fluff.
By subscribing, you agree to receive emails. Unsubscribe anytime.