Security
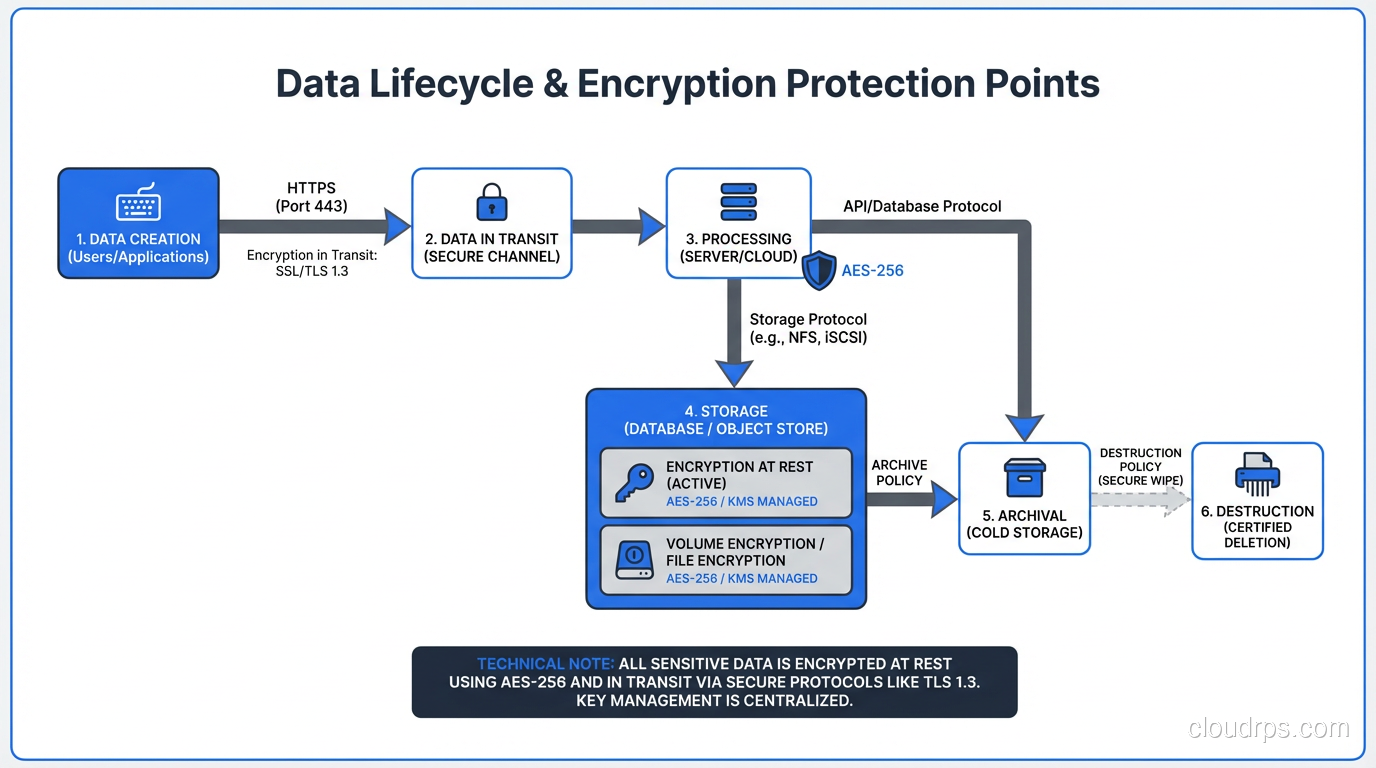
Encryption at Rest vs In Transit: A Complete Guide to Data Protection
Comprehensive guide to encryption at rest and in transit covering implementation, key management, TLS configuration, performance impact, and compliance requirements.
Practical deep dives on infrastructure, security, and scaling. No spam, no fluff.
By subscribing, you agree to receive emails. Unsubscribe anytime.