Security
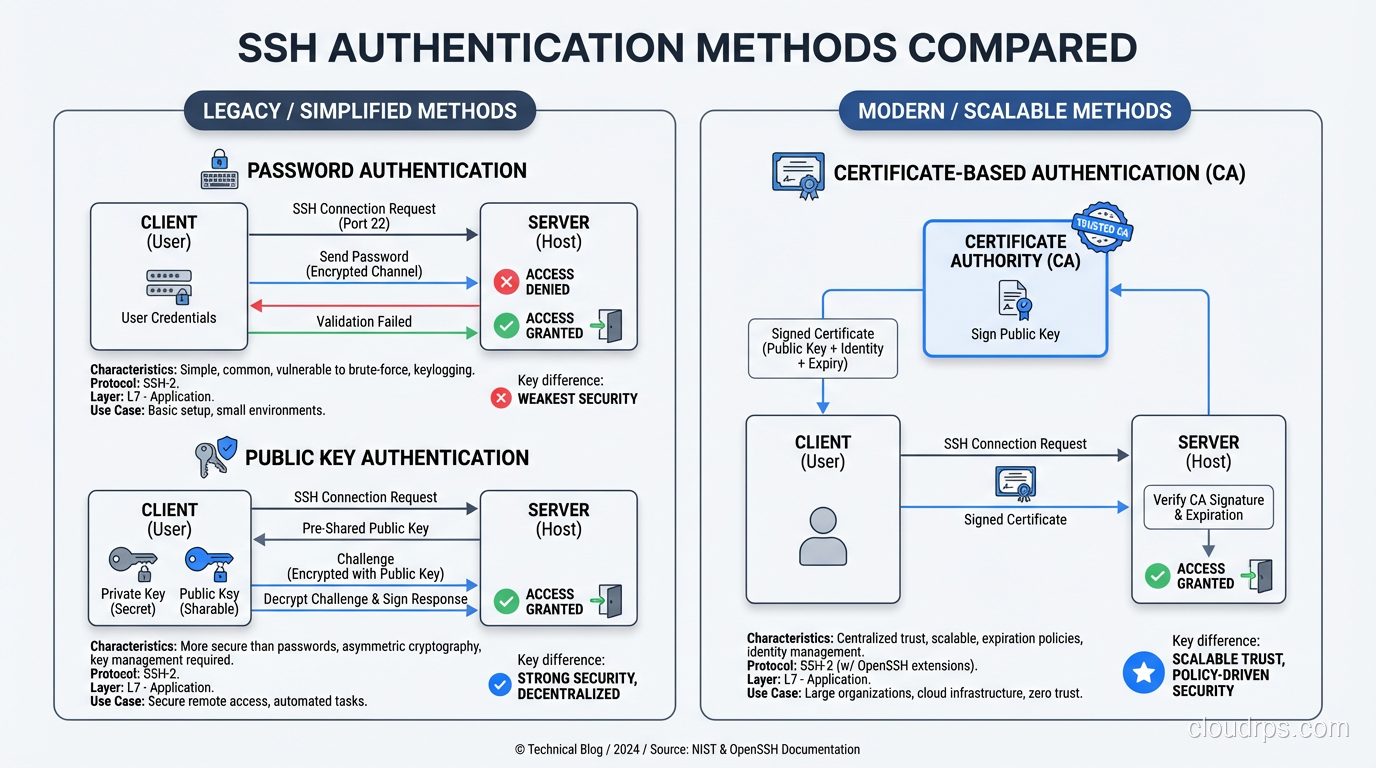
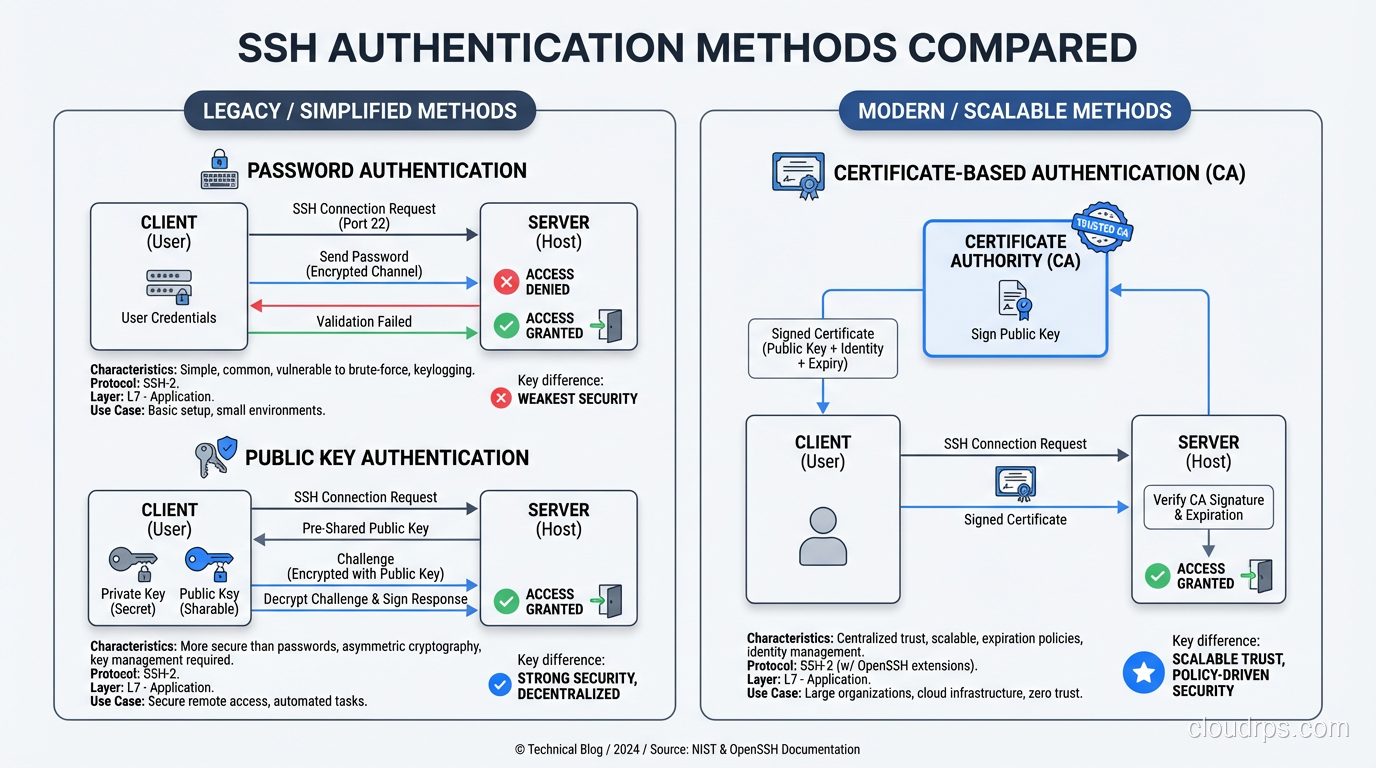
How SSH Works: Key Exchange, Authentication, and Tunneling Under the Hood
A deep dive into how the SSH protocol actually works: key exchange, host verification, authentication methods, and tunneling explained for practitioners.
A deep dive into how the SSH protocol actually works: key exchange, host verification, authentication methods, and tunneling explained for practitioners.
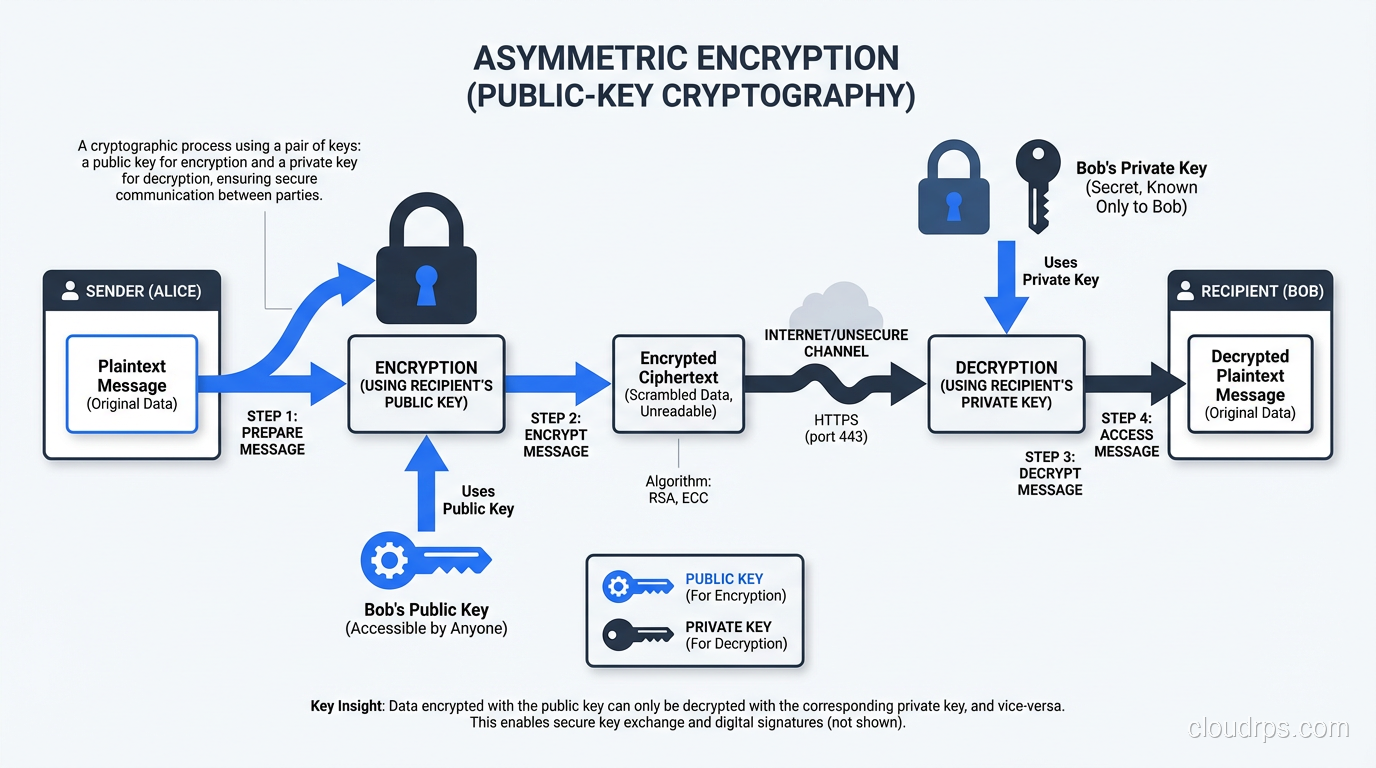
Understand the mechanics of symmetric and asymmetric encryption, compare AES vs RSA vs ECC, and learn how TLS combines both for real-world security.
Practical deep dives on infrastructure, security, and scaling. No spam, no fluff.
By subscribing, you agree to receive emails. Unsubscribe anytime.