Encryption at Rest vs In Transit: A Complete Guide to Data Protection
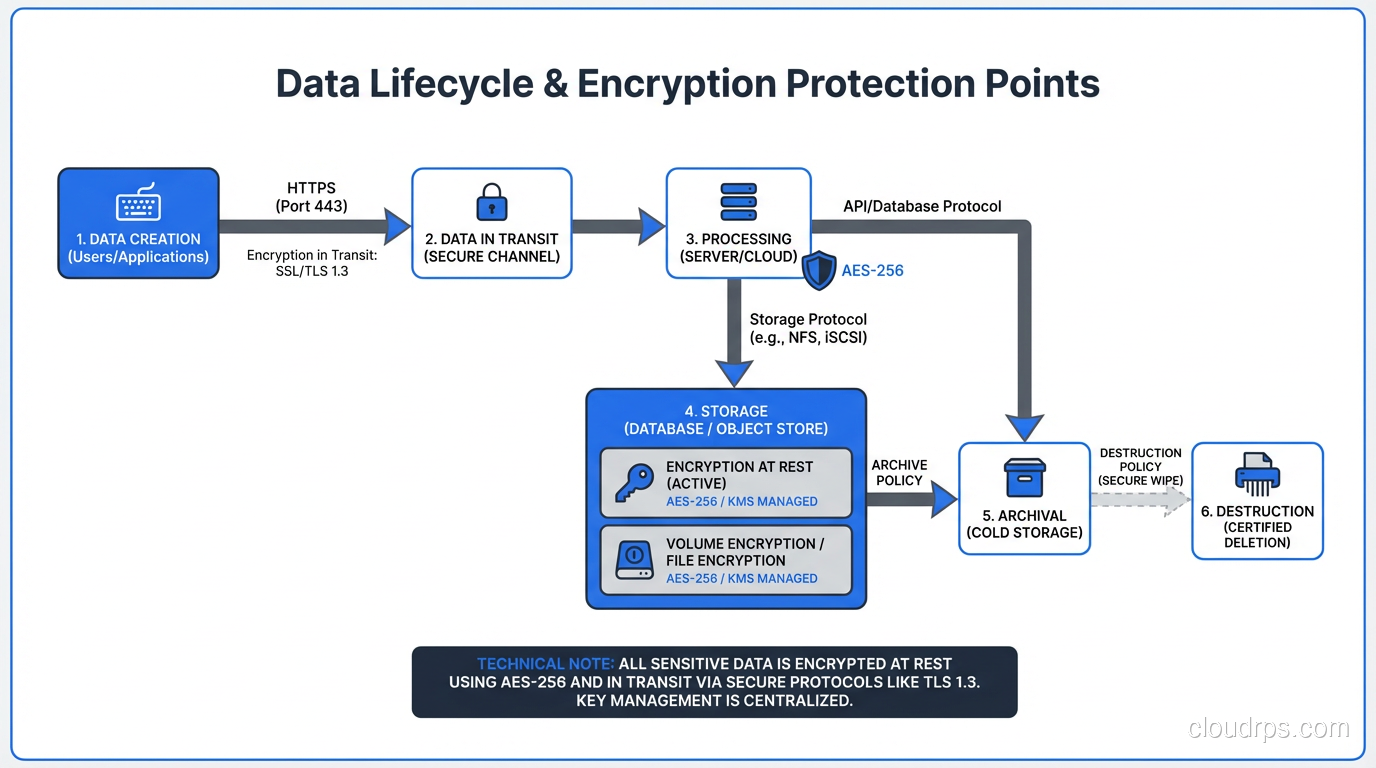
Comprehensive guide to encryption at rest and in transit covering implementation, key management, TLS configuration, performance impact, and compliance requirements.
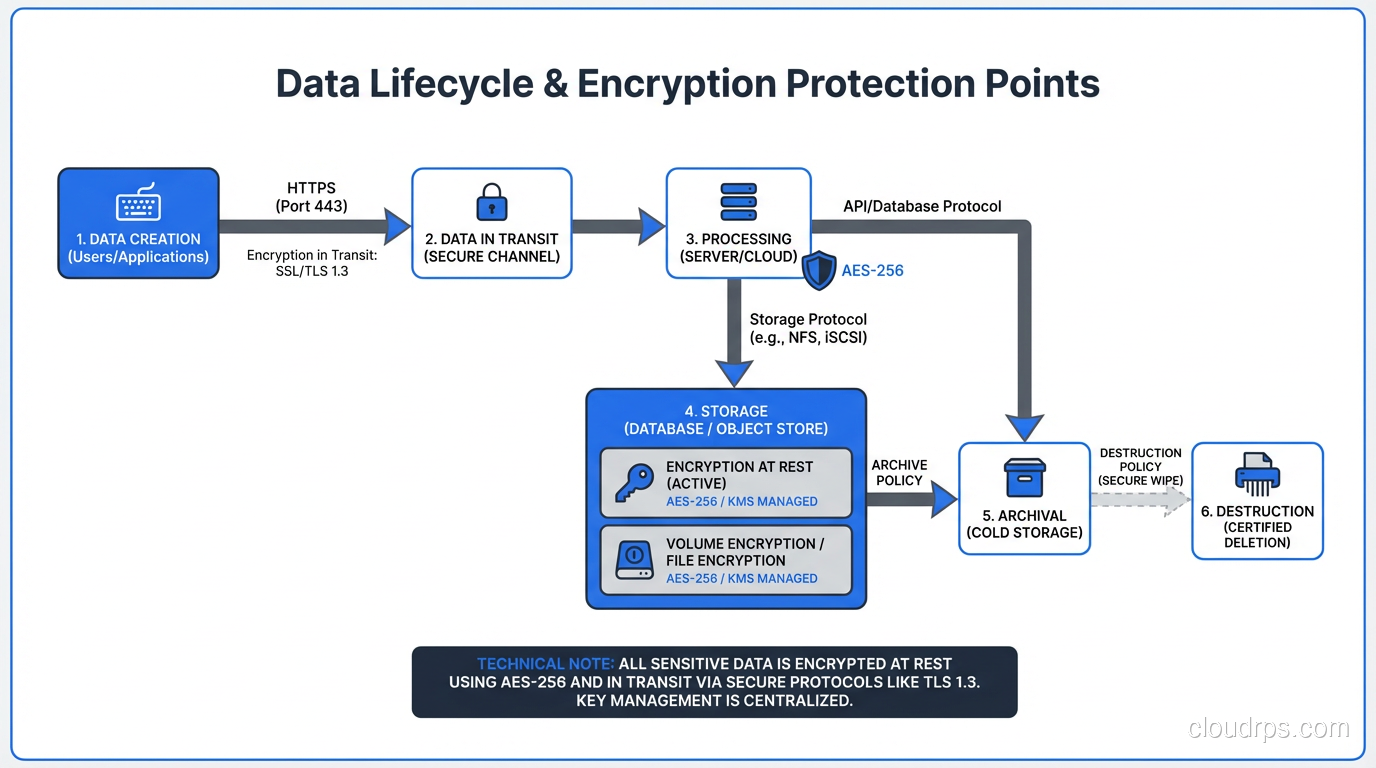
Comprehensive guide to encryption at rest and in transit covering implementation, key management, TLS configuration, performance impact, and compliance requirements.
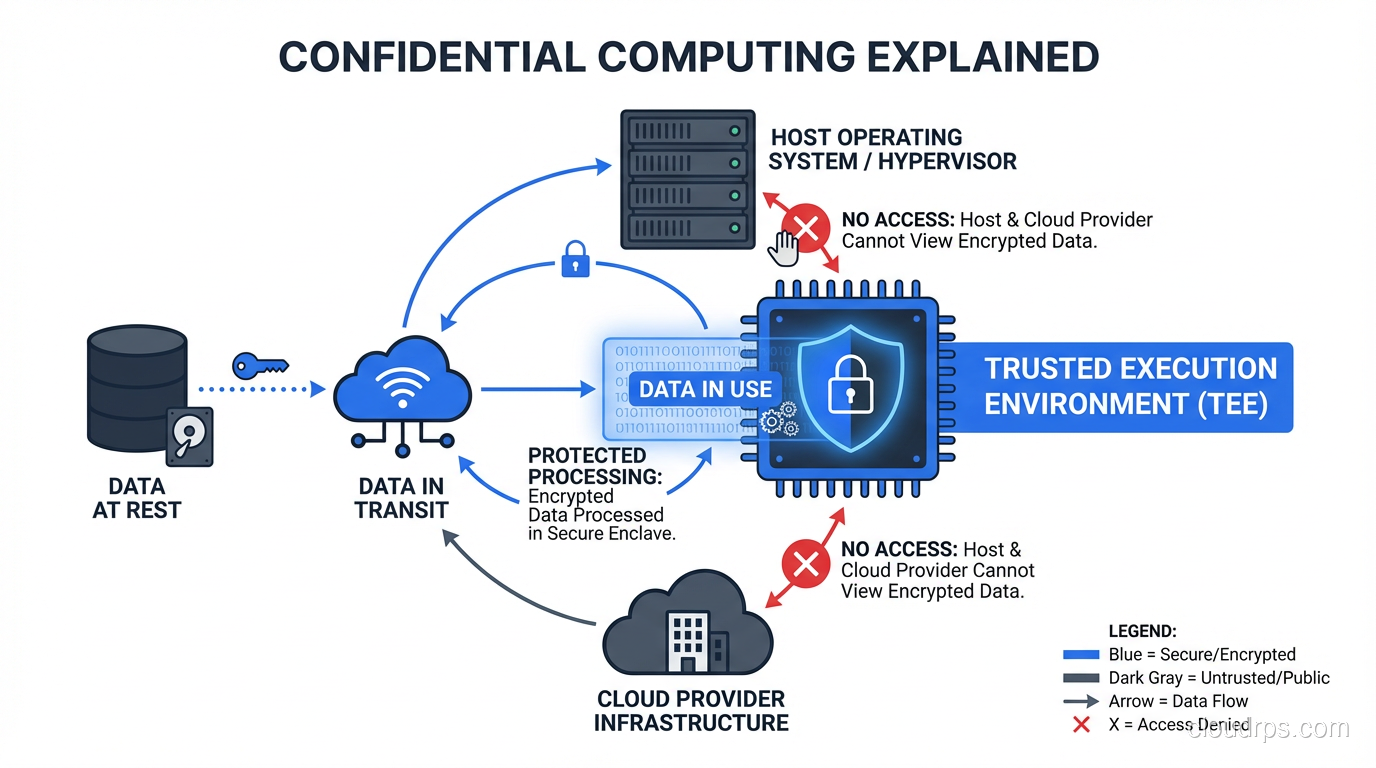
Learn how confidential computing and trusted execution environments (TEEs) protect data while it's being processed, with practical guidance on Intel SGX, AMD SEV, and cloud provider implementations.
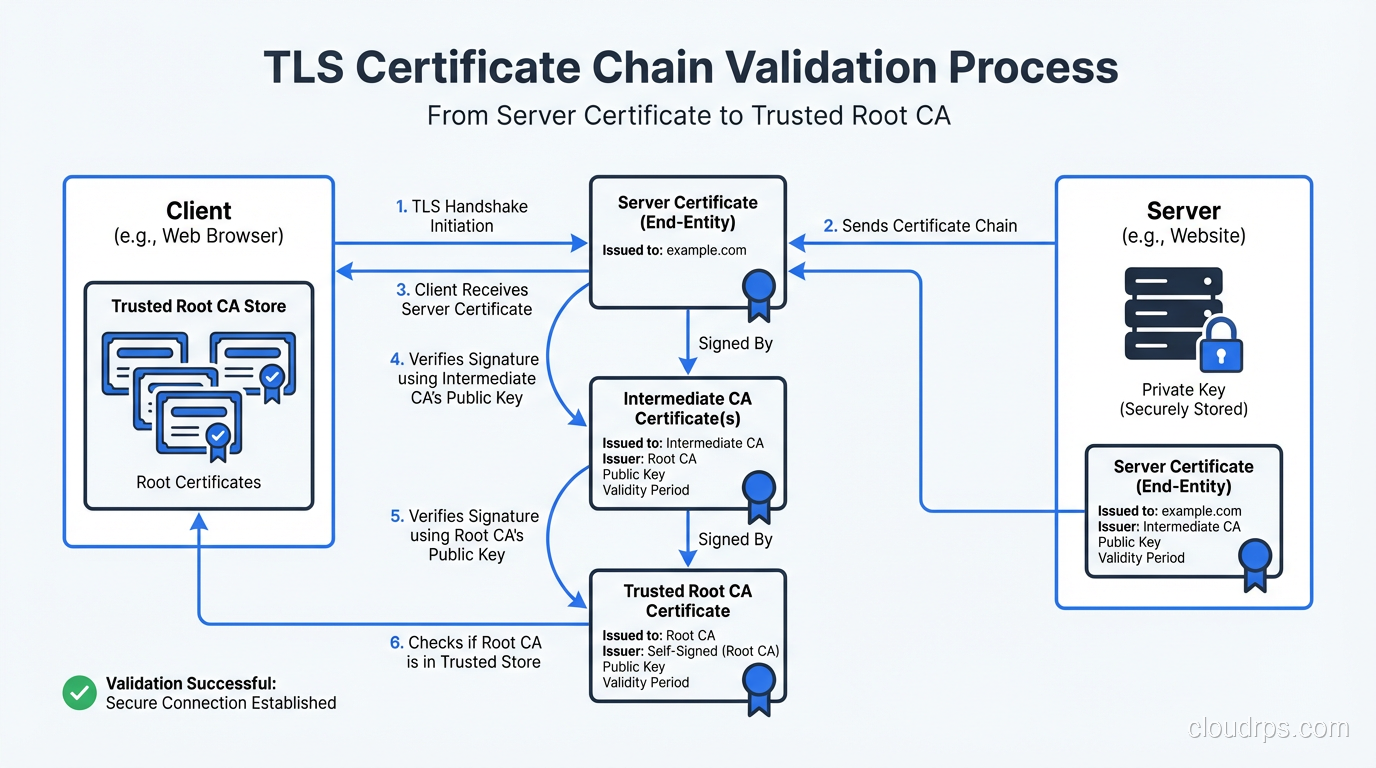
A practitioner's deep dive into how TLS works: the handshake, certificate validation, cipher suites, and what actually happens when your browser connects over HTTPS.
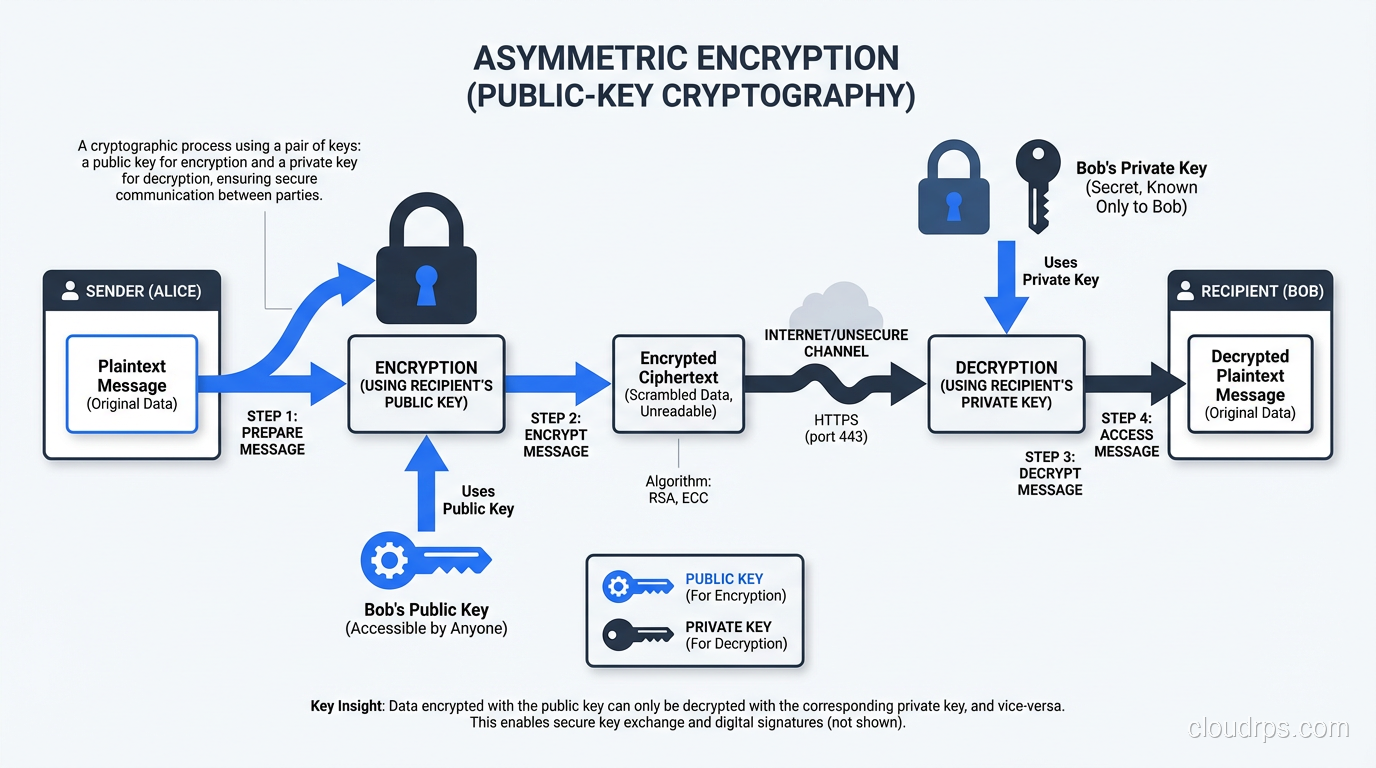
Understand the mechanics of symmetric and asymmetric encryption, compare AES vs RSA vs ECC, and learn how TLS combines both for real-world security.
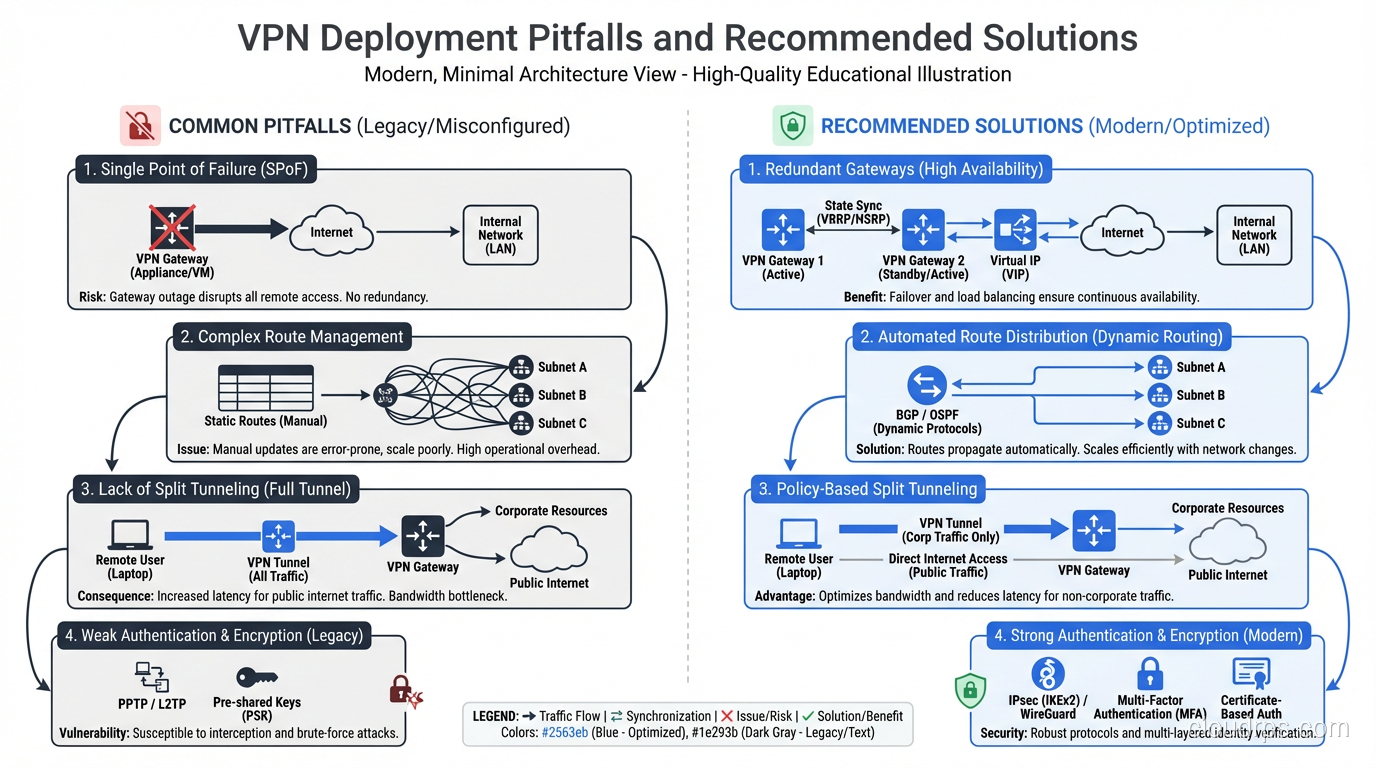
Understand how VPNs work under the hood: tunneling protocols, encryption, split tunneling, and real enterprise use cases beyond just hiding your IP address.
Practical deep dives on infrastructure, security, and scaling. No spam, no fluff.
By subscribing, you agree to receive emails. Unsubscribe anytime.