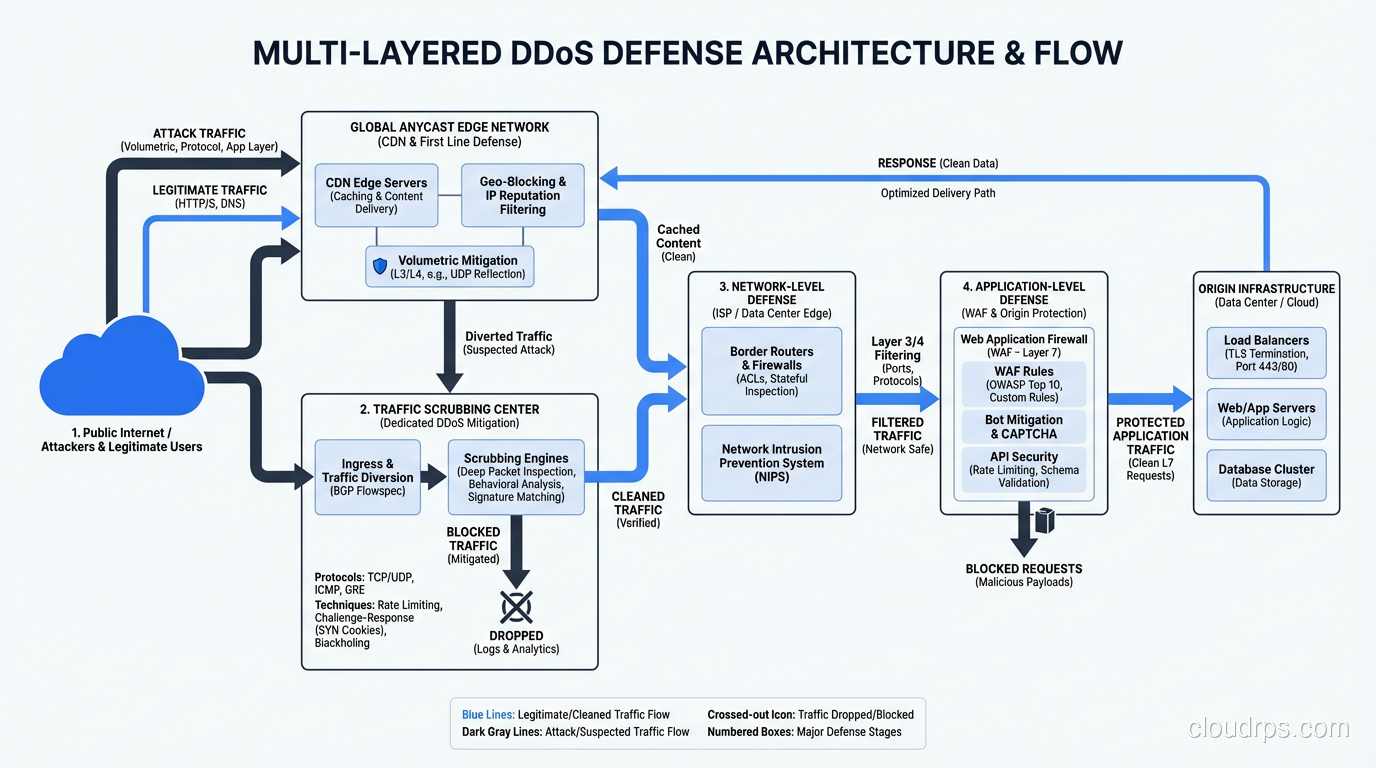
DDoS Attacks Explained: Types, Mitigation Strategies, and Real-World Defense
DDoS attacks explained by a veteran architect who has fought them in production. Learn attack types, mitigation strategies, and how to build resilient infrastructure.
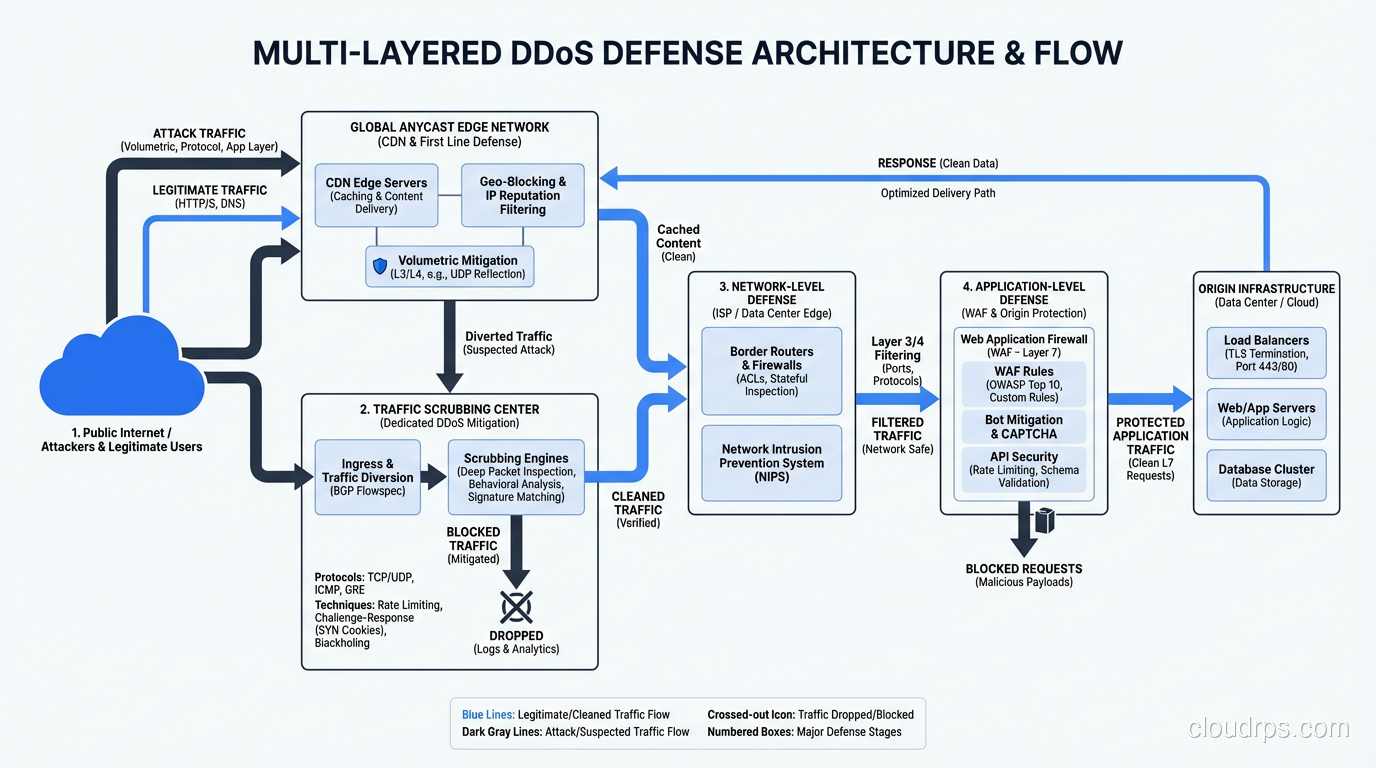
DDoS attacks explained by a veteran architect who has fought them in production. Learn attack types, mitigation strategies, and how to build resilient infrastructure.
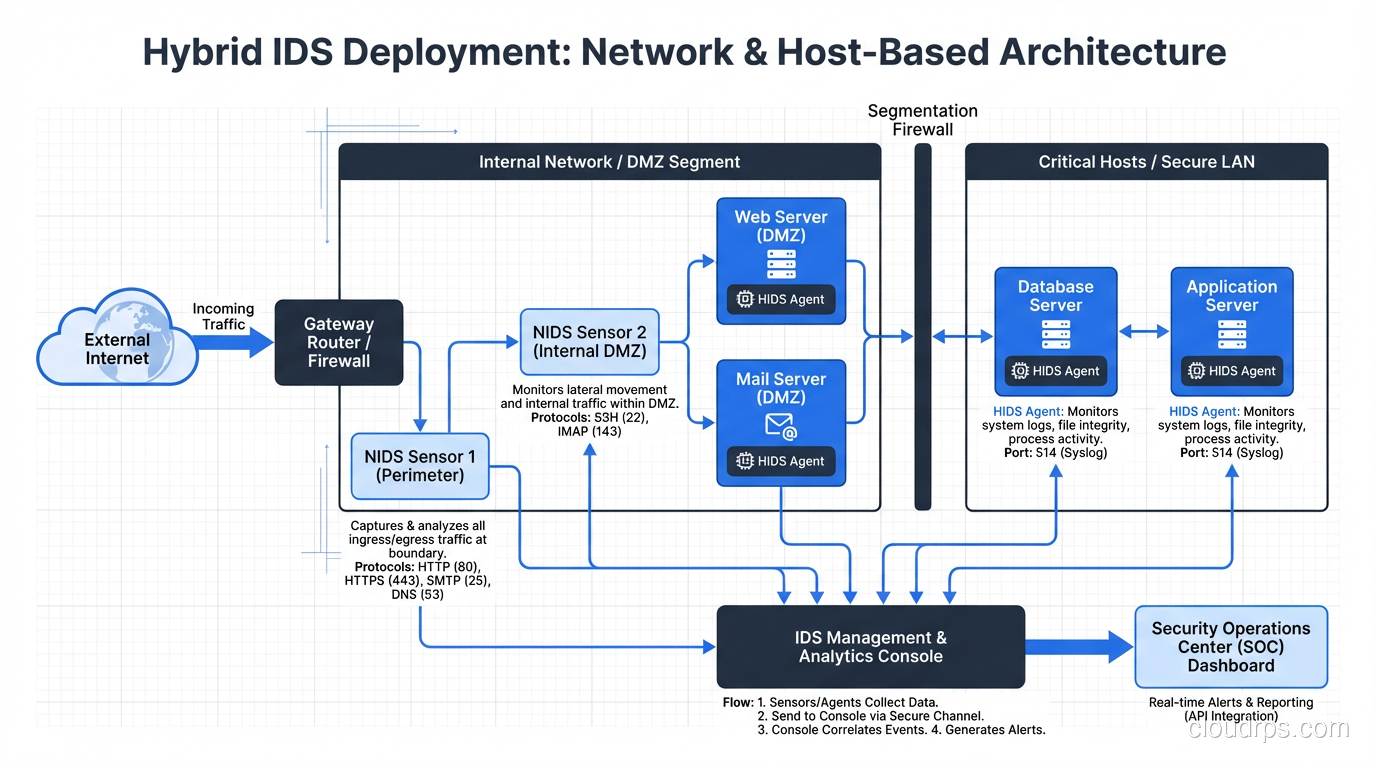
IDS vs IPS explained by a principal architect. Learn how intrusion detection and prevention systems work, when to use each, and how to deploy them in modern networks.
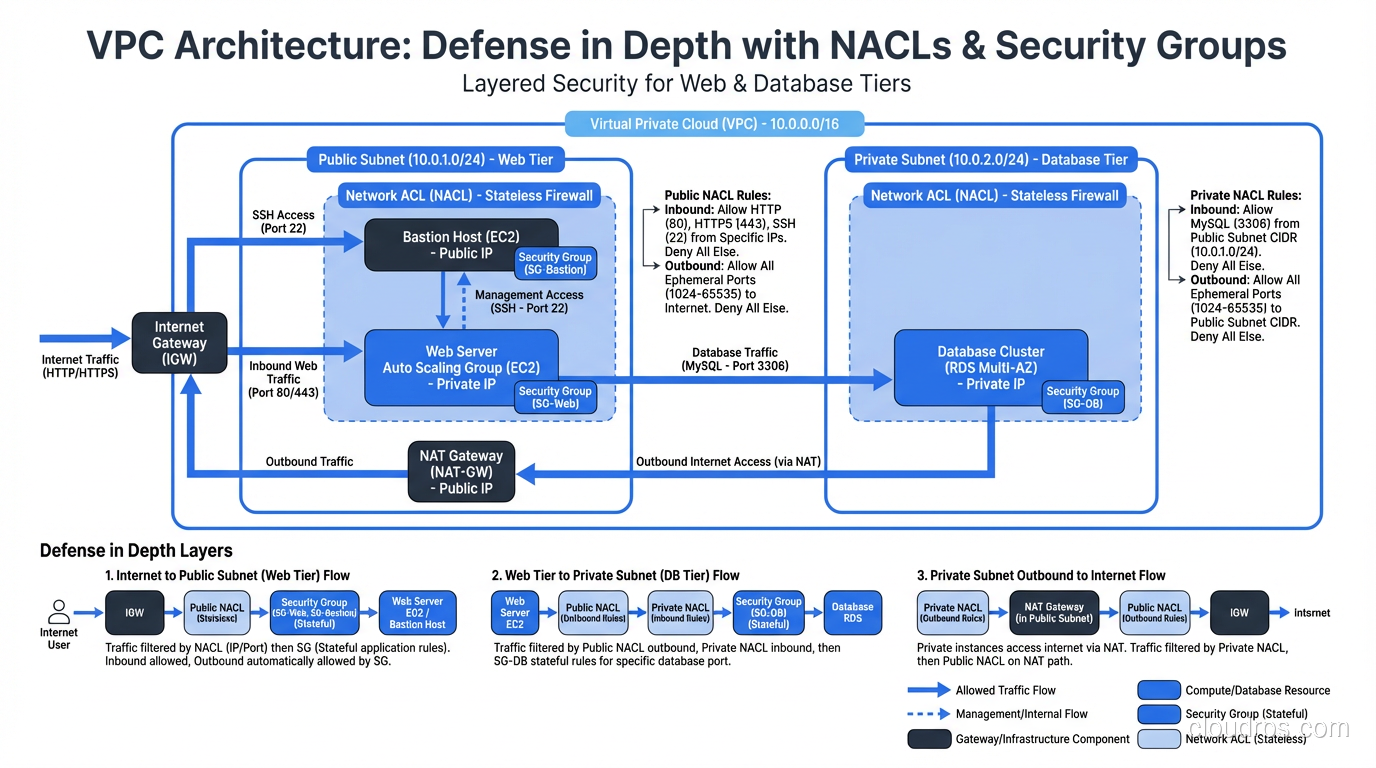
A practitioner's guide to security groups and network ACLs in cloud environments, covering how each works, key differences, and how to layer them for defense in depth.
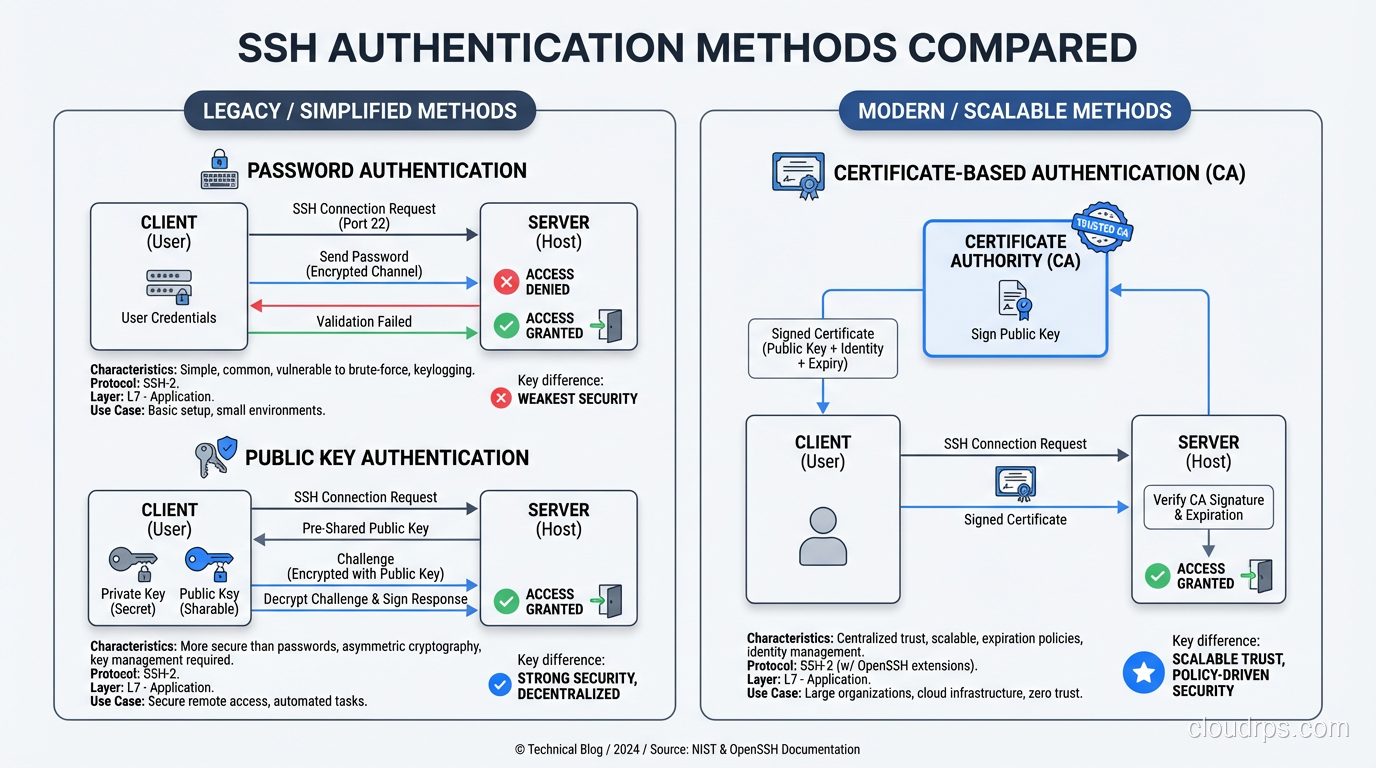
A deep dive into how the SSH protocol actually works: key exchange, host verification, authentication methods, and tunneling explained for practitioners.
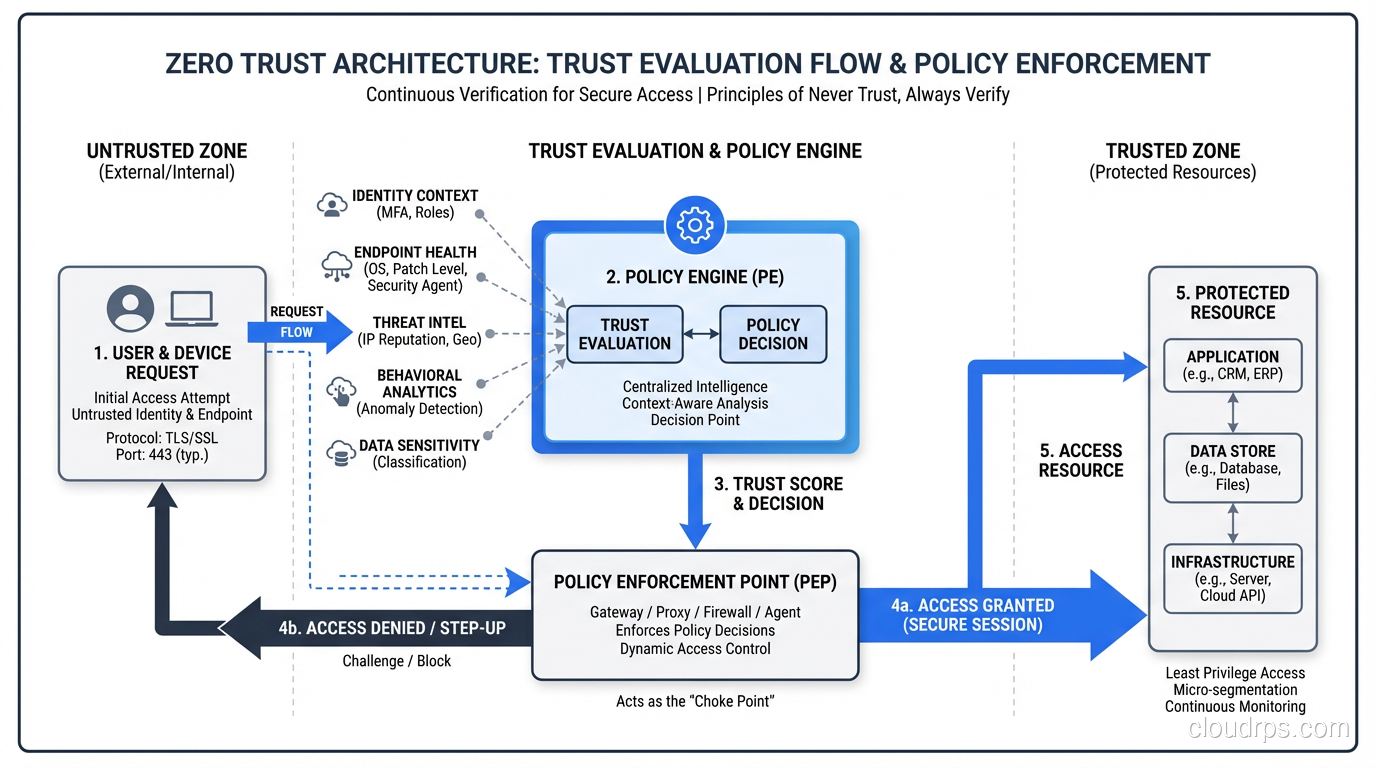
A practical guide to Zero Trust security architecture: core principles, real implementation strategies, and how to move beyond the perimeter model.
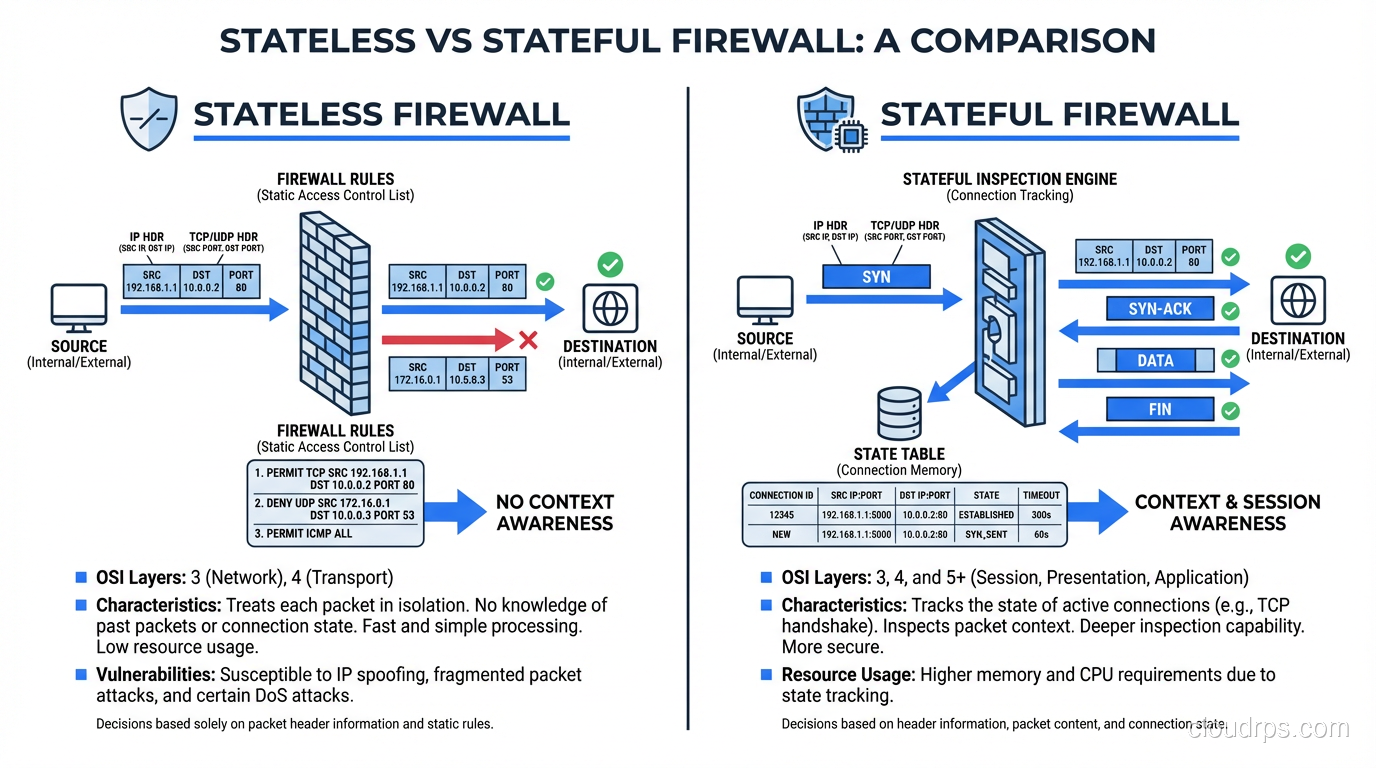
Learn the real differences between stateless and stateful firewalls, how each inspects traffic, and when to deploy them in production network architectures.
Practical deep dives on infrastructure, security, and scaling. No spam, no fluff.
By subscribing, you agree to receive emails. Unsubscribe anytime.