Encryption at Rest vs In Transit: A Complete Guide to Data Protection
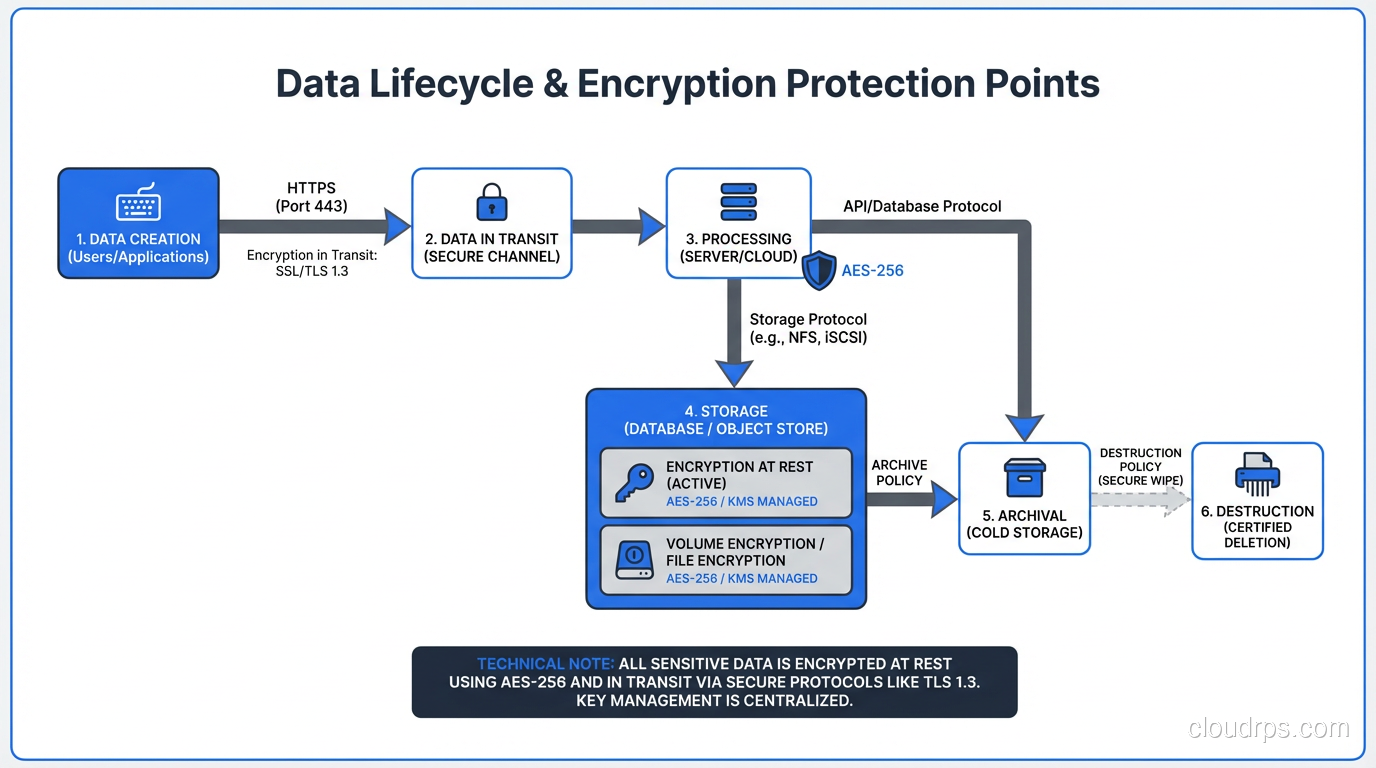
Comprehensive guide to encryption at rest and in transit covering implementation, key management, TLS configuration, performance impact, and compliance requirements.
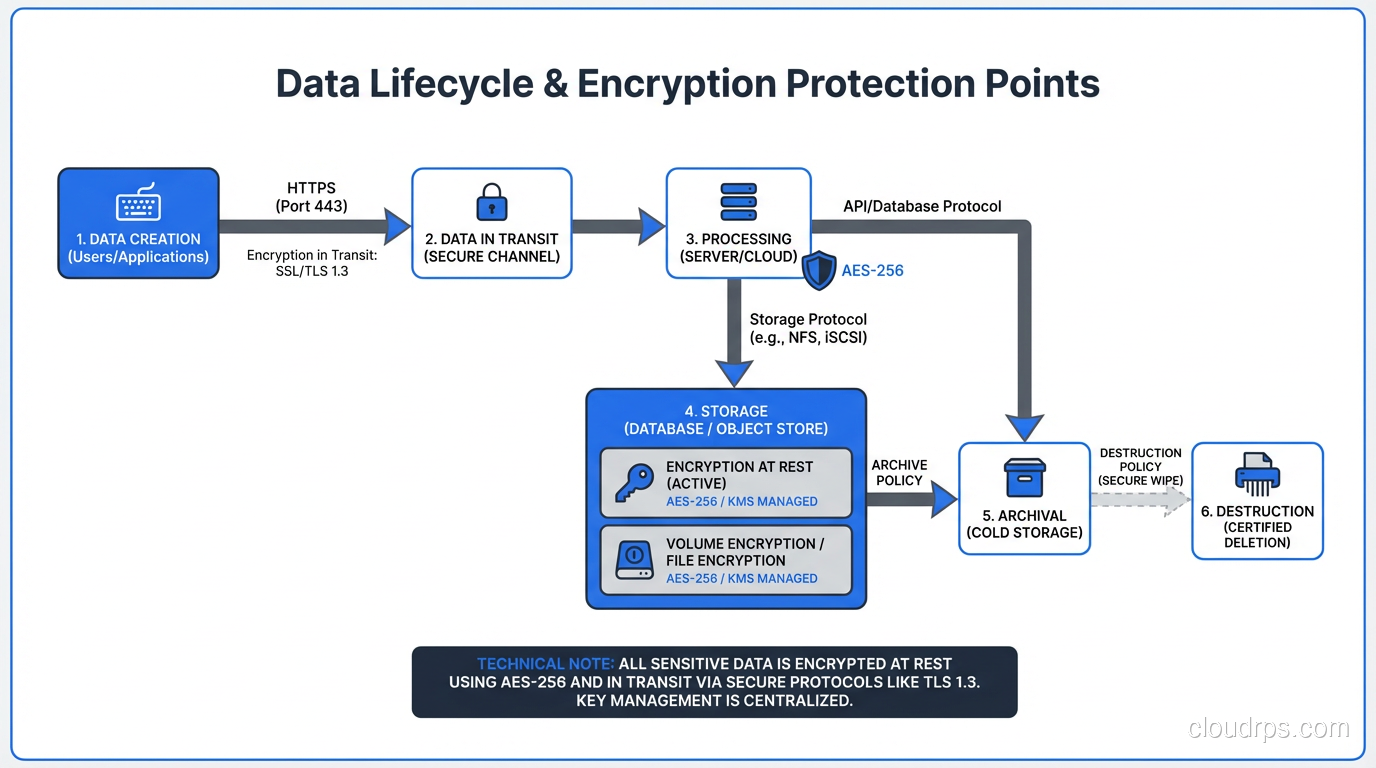
Comprehensive guide to encryption at rest and in transit covering implementation, key management, TLS configuration, performance impact, and compliance requirements.
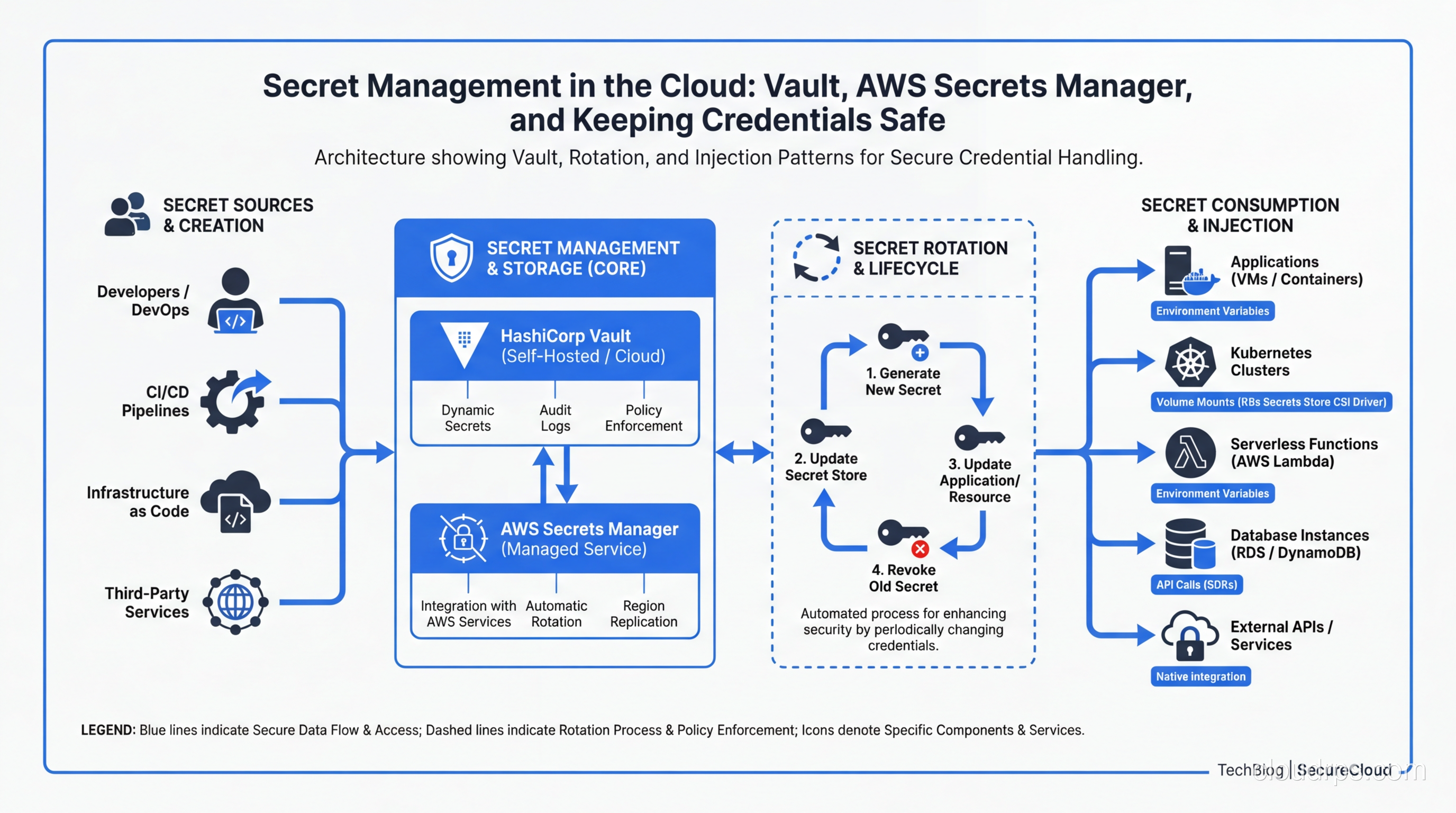
A practical guide to managing secrets in cloud infrastructure: comparing HashiCorp Vault, AWS Secrets Manager, and other tools, with real-world patterns for rotation, injection, and zero-trust secret delivery.
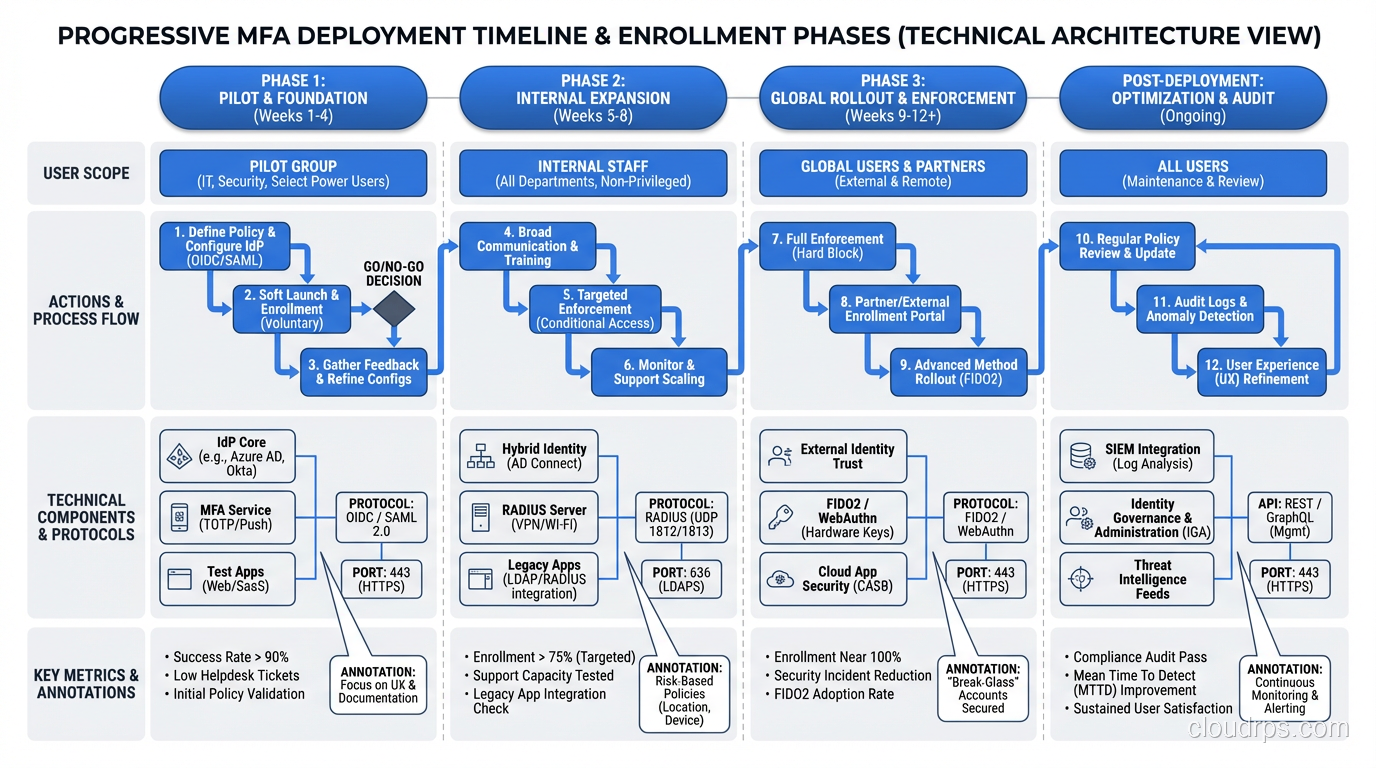
Multi-factor authentication explained by a veteran architect. Learn MFA methods, TOTP vs FIDO2, implementation patterns, and how to deploy MFA without destroying user experience.
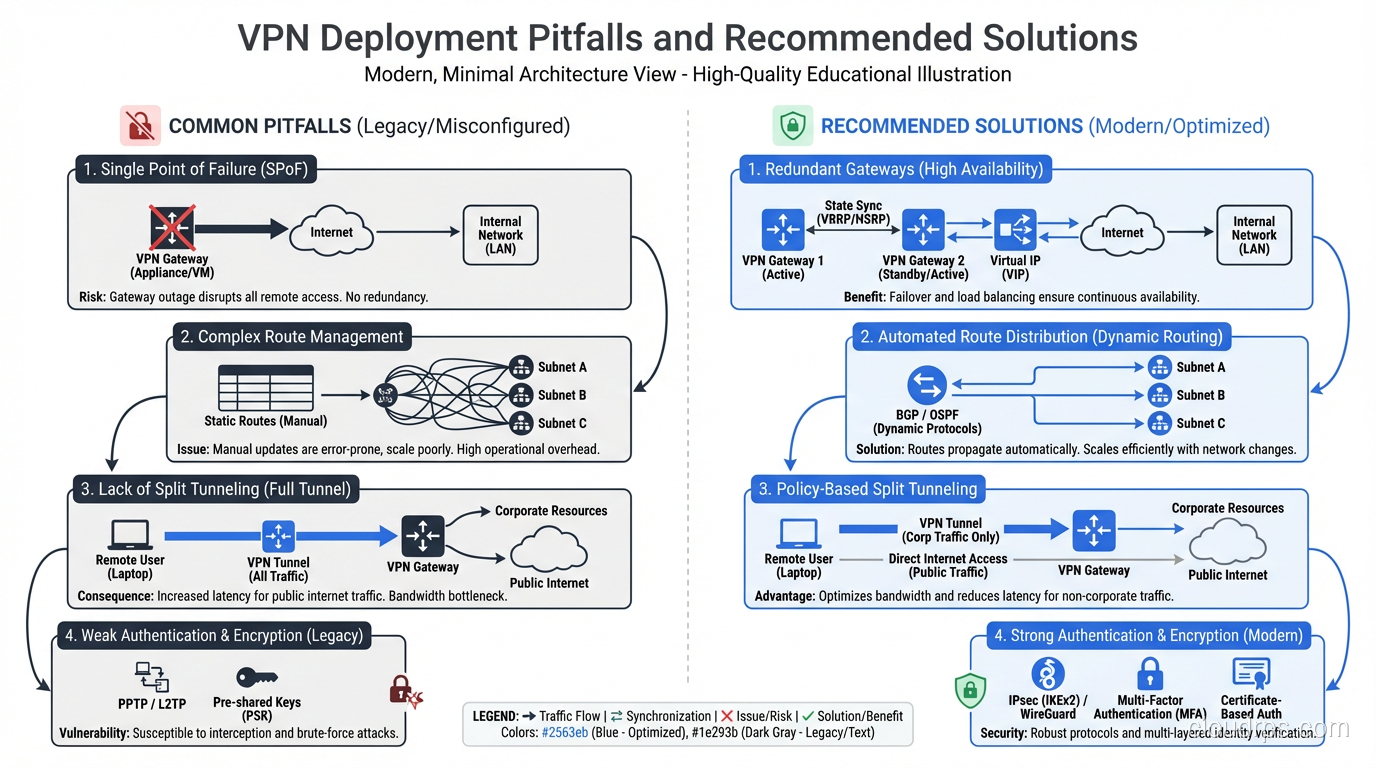
Understand how VPNs work under the hood: tunneling protocols, encryption, split tunneling, and real enterprise use cases beyond just hiding your IP address.
Practical deep dives on infrastructure, security, and scaling. No spam, no fluff.
By subscribing, you agree to receive emails. Unsubscribe anytime.