Security
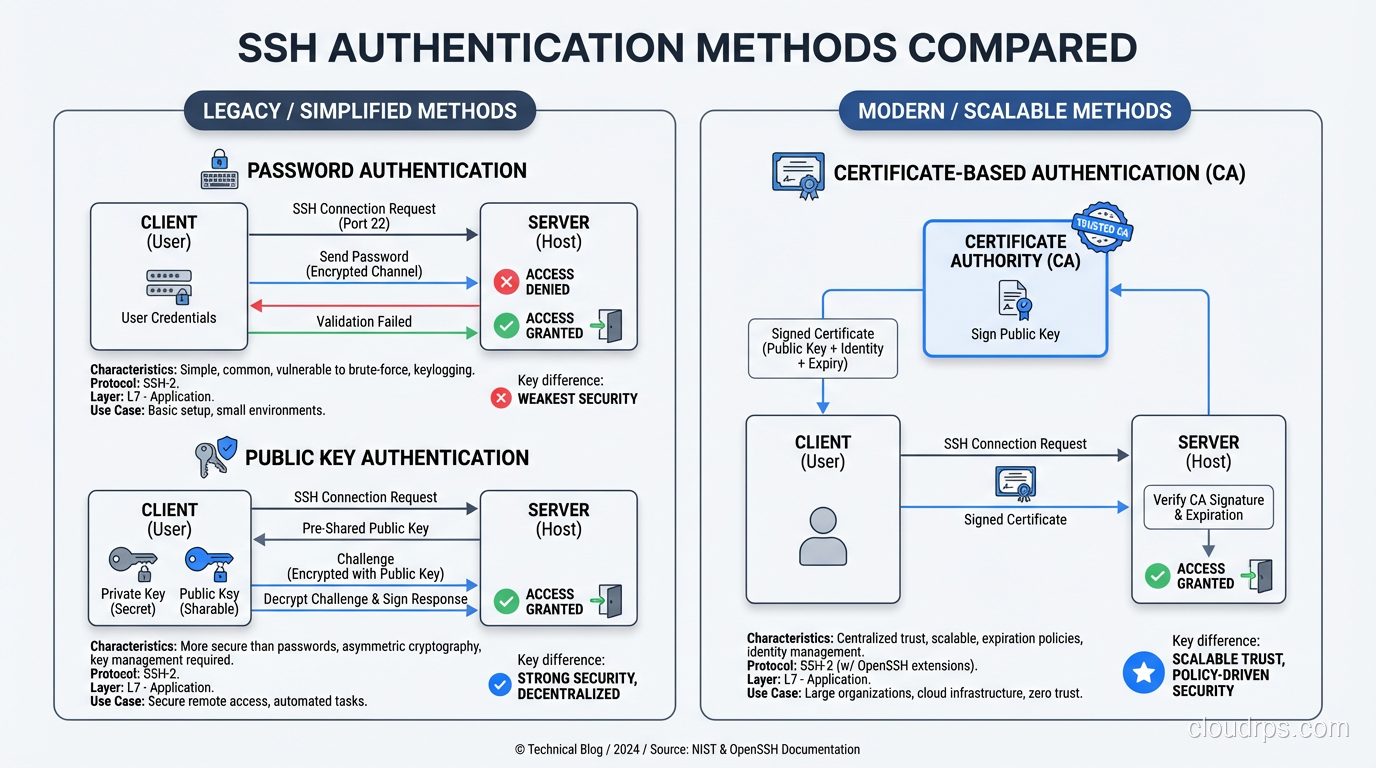
How SSH Works: Key Exchange, Authentication, and Tunneling Under the Hood
A deep dive into how the SSH protocol actually works: key exchange, host verification, authentication methods, and tunneling explained for practitioners.
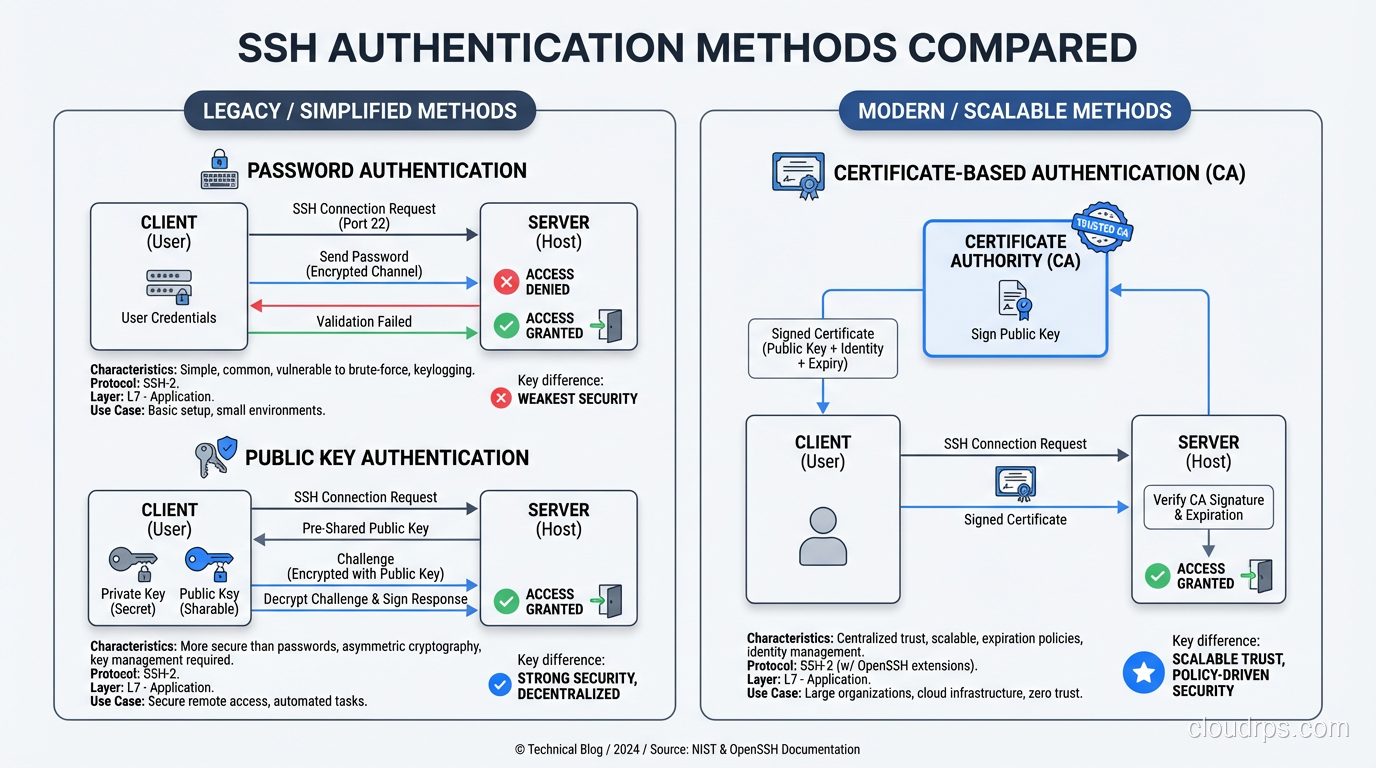
A deep dive into how the SSH protocol actually works: key exchange, host verification, authentication methods, and tunneling explained for practitioners.
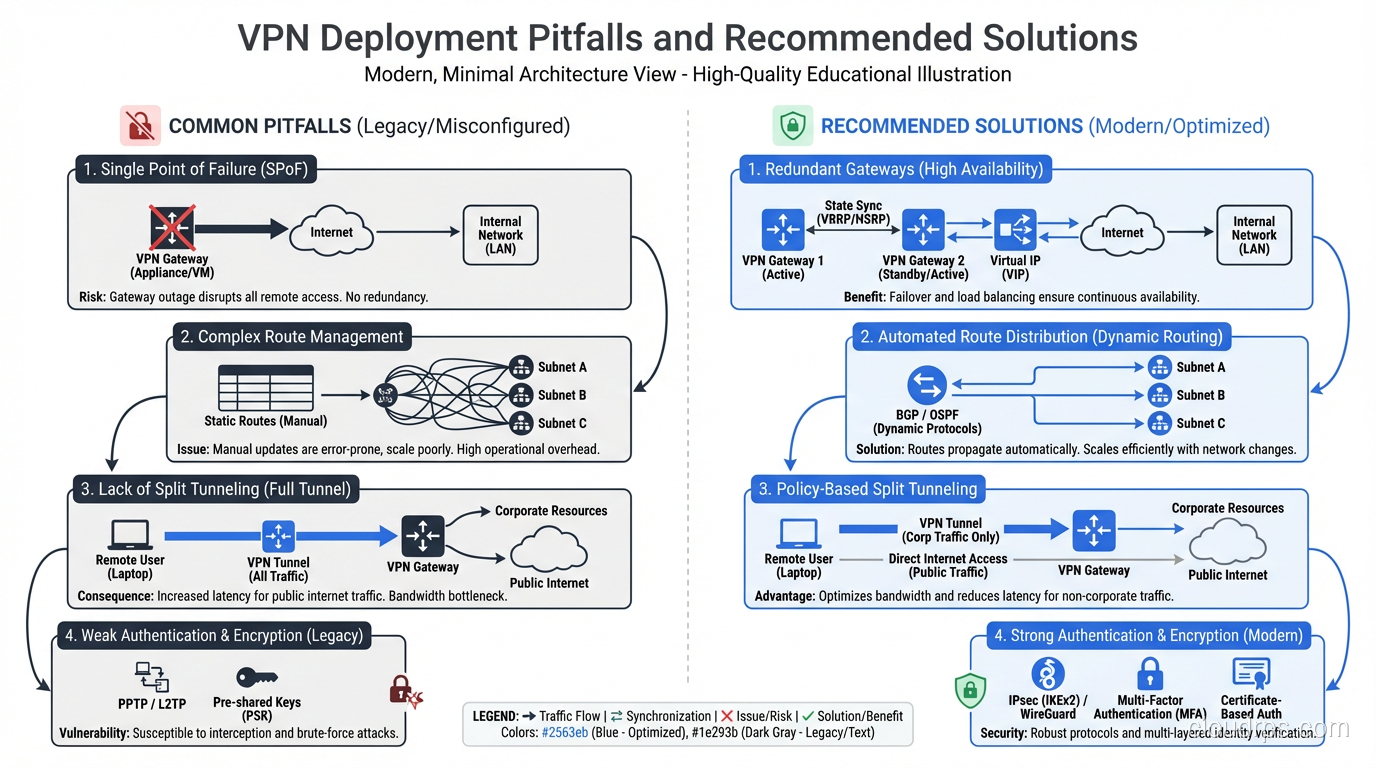
Understand how VPNs work under the hood: tunneling protocols, encryption, split tunneling, and real enterprise use cases beyond just hiding your IP address.
Practical deep dives on infrastructure, security, and scaling. No spam, no fluff.
By subscribing, you agree to receive emails. Unsubscribe anytime.